Activity 3rd Party Apps Sumuri
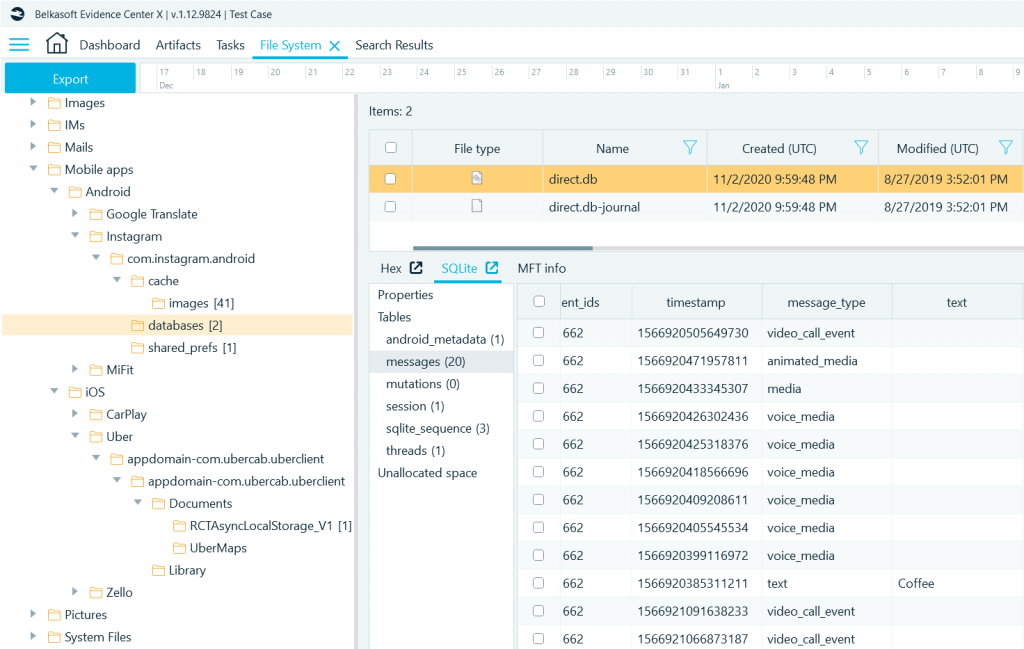
Activity 3rd Party Apps Sumuri Module 05 – understanding android artifacts locate the user’s 3rd party apps not decoded by bec x open and review the app folder structure examine the app data open and […]. Module 3 – mobile device acquisitions activity – logical acquisition of an iphone using the afc method activity – logical acquisition of an iphone using the itunes backup method activity – logical acquisition of an android phone using the adb backup method activity – logical acquisition of an android phone using the mtp ptp method.
Activity 3rd Party Apps Sumuri Activity – logical acquisition of an iphone using the afc method activity – logical acquisition of an iphone using the itunes backup method activity – logical acquisition of an android phone using the adb backup method activity – logical acquisition of an android phone using the mtp ptp method. Module 04 – understanding apple ios artifacts overview each app is an island sandboxed independent folder structure access to primarily information within the app may have limited access to other […]. Activity – logical acquisition of an iphone using the itunes backup method activity – logical acquisition of an android phone using the adb backup method activity – logical acquisition of an android phone using the mtp ptp method activity – manual acquisition of an android phone using the screen capturer method quiz – module 3. From there, you can learn how the third party app or service uses your data and how they keep it safe. you can allow third party apps and services some access to your google account.

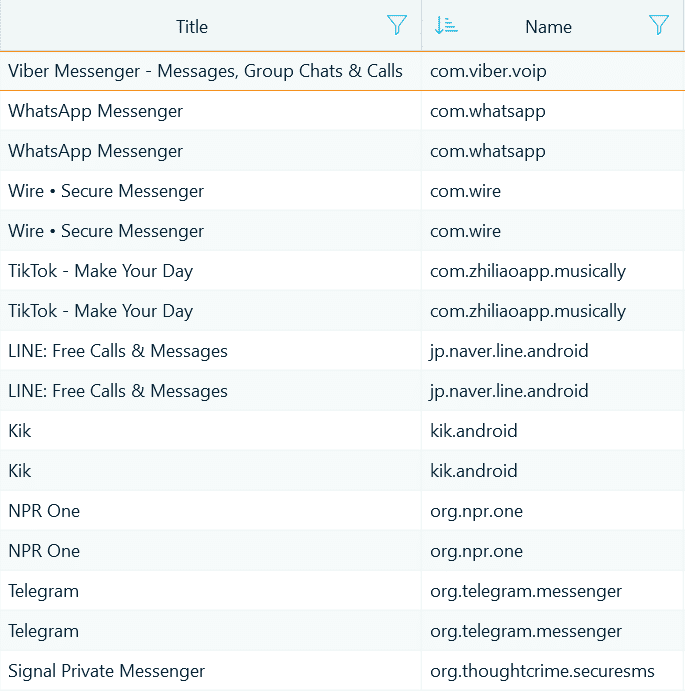
Activity Filtering Sumuri Activity – logical acquisition of an iphone using the itunes backup method activity – logical acquisition of an android phone using the adb backup method activity – logical acquisition of an android phone using the mtp ptp method activity – manual acquisition of an android phone using the screen capturer method quiz – module 3. From there, you can learn how the third party app or service uses your data and how they keep it safe. you can allow third party apps and services some access to your google account. Recurring recent security activity notification already replied & not listed in 3rd party apps? i keep receiving a recent security activity notification from google play that i've. There is a way to check third party app access history. go to myactivity.google myactivity?pli=1 and search for that app. Uses of social media uses of social media activity #1: basic google searching activity #2: advanced google searching activity #3: facebook searches activity #4: twitter searches activity #5: instagram searches activity #6: tumblr searches activity #7: searches 8 lessons. While many are safe, downloading third party apps from unverified sources can be risky. knowing the differences can help you avoid potential issues. below, we’ll discuss the types of third party apps (with examples) and what sets them apart from first party ones.
Sumuri Digital Forensics Solutions Recurring recent security activity notification already replied & not listed in 3rd party apps? i keep receiving a recent security activity notification from google play that i've. There is a way to check third party app access history. go to myactivity.google myactivity?pli=1 and search for that app. Uses of social media uses of social media activity #1: basic google searching activity #2: advanced google searching activity #3: facebook searches activity #4: twitter searches activity #5: instagram searches activity #6: tumblr searches activity #7: searches 8 lessons. While many are safe, downloading third party apps from unverified sources can be risky. knowing the differences can help you avoid potential issues. below, we’ll discuss the types of third party apps (with examples) and what sets them apart from first party ones.
Sumuri Digital Forensics Solutions Uses of social media uses of social media activity #1: basic google searching activity #2: advanced google searching activity #3: facebook searches activity #4: twitter searches activity #5: instagram searches activity #6: tumblr searches activity #7: searches 8 lessons. While many are safe, downloading third party apps from unverified sources can be risky. knowing the differences can help you avoid potential issues. below, we’ll discuss the types of third party apps (with examples) and what sets them apart from first party ones.
Comments are closed.