Active Ftp Issue With Azure Firewall

Azure Active Ftp Filezilla Works Perracing By default, active ftp is disabled on azure firewall. enable it by using powershell, cli, or an arm template. By default, active ftp is disabled on azure firewall. you can enable it using powershell, cli, and arm template.
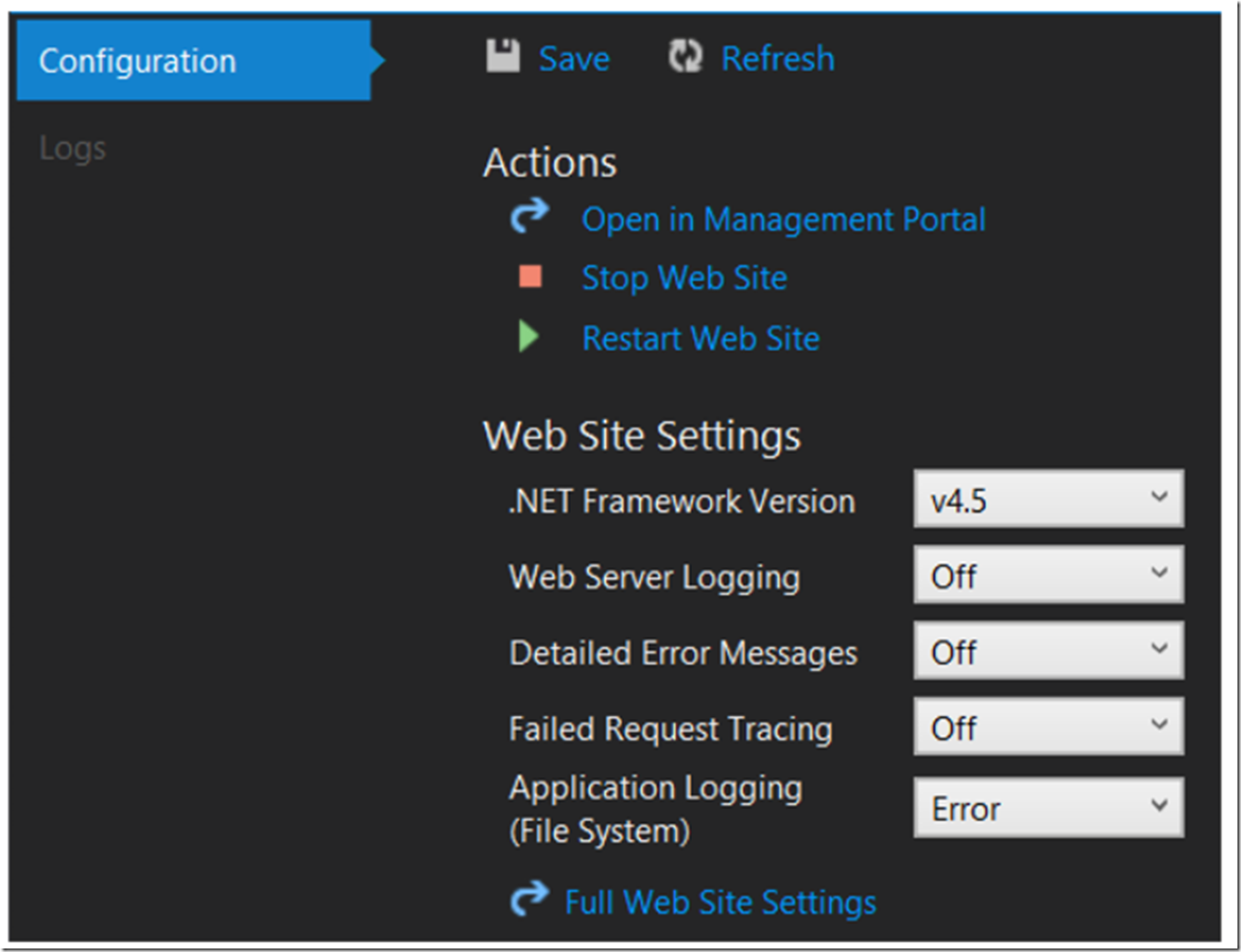
Azure Active Ftp Filezilla Works Winsexi By default, passive ftp is enabled and active ftp support is disabled to protect against ftp bounce attacks using the ftp port command. however, you can enable active ftp when you deploy using azure powershell, the azure cli, or an azure arm template. The ftp server has "firewall passive connection settings" configured with the correct public ip and a port range. i don't think this should matter for the active connection but mentioning just in case. In this guide, we will cover the necessary steps to deploy an ftp service in azure using azure blob storage for file storage, and we will implement security best practices to ensure safe file transfers. You should enable active ftp support on azure firewall. the simplest way to do this is to export the firewall template and redeploy with the additional properties updated to allow active ftp.
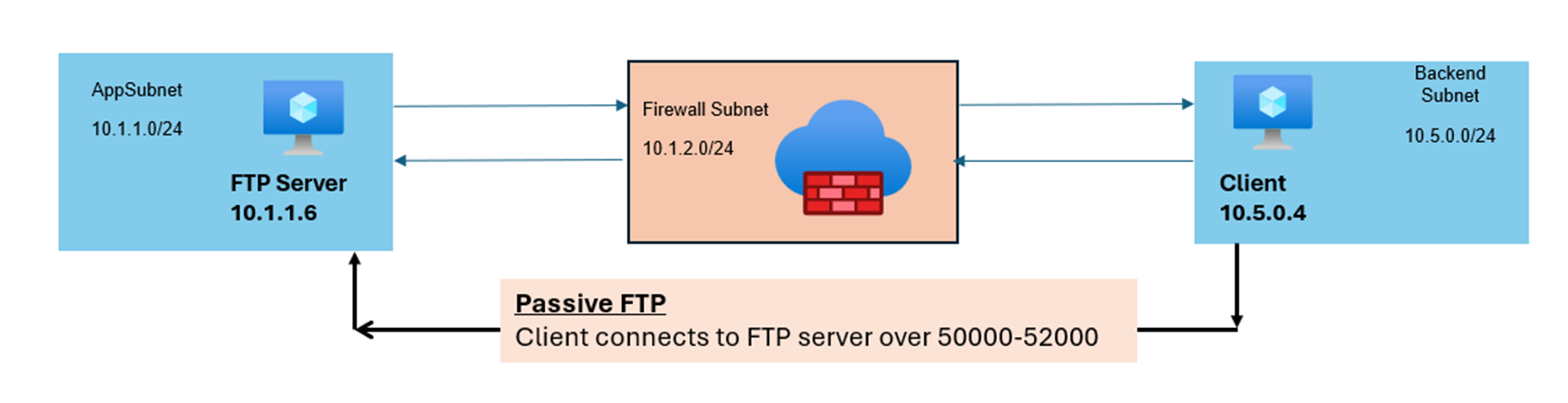
Validating Ftp Traffic Scenarios With Azure Firewall Microsoft In this guide, we will cover the necessary steps to deploy an ftp service in azure using azure blob storage for file storage, and we will implement security best practices to ensure safe file transfers. You should enable active ftp support on azure firewall. the simplest way to do this is to export the firewall template and redeploy with the additional properties updated to allow active ftp. You should enable active ftp support on azure firewall. the simplest way to do this is to export the firewall template and redeploy with the additional properties updated to allow active ftp. Passive ftp over the internet is currently unsupported because the data path traffic (from the internet client via azure firewall) can potentially use a different ip address (due to the load balancer). By default, passive ftp is enabled, and active ftp support is disabled to protect against ftp bounce attacks using the ftp port command. read the blog: validating ftp traffic scenarios with azure firewall microsoft community hub. Likewise for internet ftp traffic, it is recommended to provision azure firewall with a single public ip for ftp connectivity. it is recommended to use nat gateway to avoid snat exhaustion.
Comments are closed.