Active Attack Vs Passive Attack Pdf
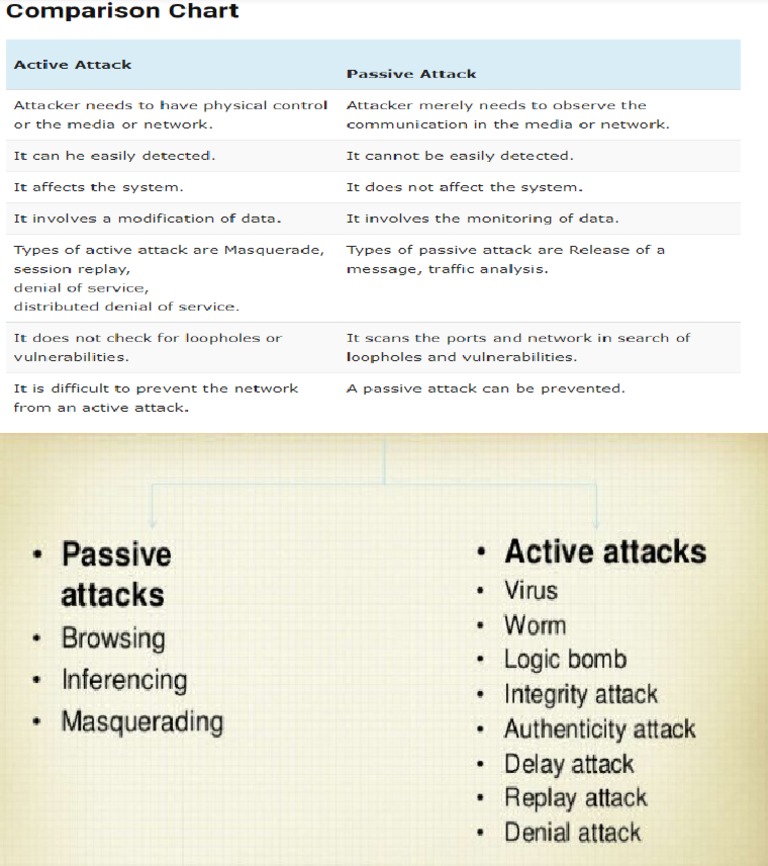
Active Attack Vs Passive Attack Pdf Appropriate relevant solutions are presented based on literature study to overcome insecure wireless network usage practices in order to avoid active and passive attacks. The document outlines two types of security attacks: passive and active. passive attacks involve monitoring and observing data without altering it, while active attacks involve modifying data and disrupting system resources.

Difference Between Active Attack And Passive Attack Pdf Fault Observes passively without interacting or leaving traces. requires deep packet inspection, anomaly detection, and encrypted channels to uncover. Therefore, there are two types of major attacks from wireless network that users and organizations should be aware of, which are passive attacks (fig. 2) and active attacks (fig. 1). This research is aimed to identify the impacts of active and passive attacks on network layer in a manet. outcomes of this research will be help to re design routing protocol with an adaptive model to handle network layer attacks in manet. In the field of cybersecurity, attacks on networks and systems are broadly classified into two categories: active and passive attacks. it is, therefore, important to understand the differences between these two types of attacks so that adequate security measures can be formulated.

Active And Passive Attack Pdf Denial Of Service Attack Computer This research is aimed to identify the impacts of active and passive attacks on network layer in a manet. outcomes of this research will be help to re design routing protocol with an adaptive model to handle network layer attacks in manet. In the field of cybersecurity, attacks on networks and systems are broadly classified into two categories: active and passive attacks. it is, therefore, important to understand the differences between these two types of attacks so that adequate security measures can be formulated. Any attack on ad hoc networks can also be categorized as active and passive attacks. in an active attack, the misbehaving node actively disturbs the normal operation of the network with attempts to alter or destroy the data being exchanged in the network. Password cracking seems to be frequent for active attacks on confidentiality while port scanning and ping sweeps seem to be more frequent as a passive attack. other confidentiality attacks include social engineering, phishing, pharming, keylogging and wiretapping. Unit – 1 security attacks: useful means of classifying security attacks, used both in x.800 and rfc 4949, is in terms of passive attacks and active attacks (figure 1.2). The attackers will perform passive attacks in order to collect information before they start performing an active attack. the attackers try to disrupt and break into the system.

Active Attack Vs Passive Attack What S The Difference Any attack on ad hoc networks can also be categorized as active and passive attacks. in an active attack, the misbehaving node actively disturbs the normal operation of the network with attempts to alter or destroy the data being exchanged in the network. Password cracking seems to be frequent for active attacks on confidentiality while port scanning and ping sweeps seem to be more frequent as a passive attack. other confidentiality attacks include social engineering, phishing, pharming, keylogging and wiretapping. Unit – 1 security attacks: useful means of classifying security attacks, used both in x.800 and rfc 4949, is in terms of passive attacks and active attacks (figure 1.2). The attackers will perform passive attacks in order to collect information before they start performing an active attack. the attackers try to disrupt and break into the system.
Comments are closed.