Accidentally Leaked Your Api Keys On Github %f0%9f%9a%80 Techhacks Git Techtech Github Githubrepository
Leaked Bitcoin Private Keys From Github This tutorial walks you through what to do if you've accidentally committed a secret to your repository, or if you've been alerted to a secret leak in your repository. Emergency steps when api keys or passwords are accidentally pushed to github. from credential revocation to full history removal with git filter repo bfg.
Securely Using Api Keys In Postman Learn what to do immediately, how to prevent future leaks, and what tools can automatically scan your repos for secrets. it happens to almost every developer at least once: you accidentally commit an api key, database password, or private token to a public github repository. We've all been there, accidentally pushing sensitive information like passwords, tokens, or api keys into a repository. even if your repo is internal, these leaks are serious and require. According to the state of secret sprawls 2025 report 1, gitguardian detected almost 24 million secrets in public github commits in 2024! in the following blog post i will explore different options of preventing leaking secrets in the first place and what to do when you were unable to prevent it. Deleted api keys stay in git history forever. this article shows you how to detect leaked secrets with gitleaks, remove them from history, and prevent future leaks with pre commit hooks and proper secret management.
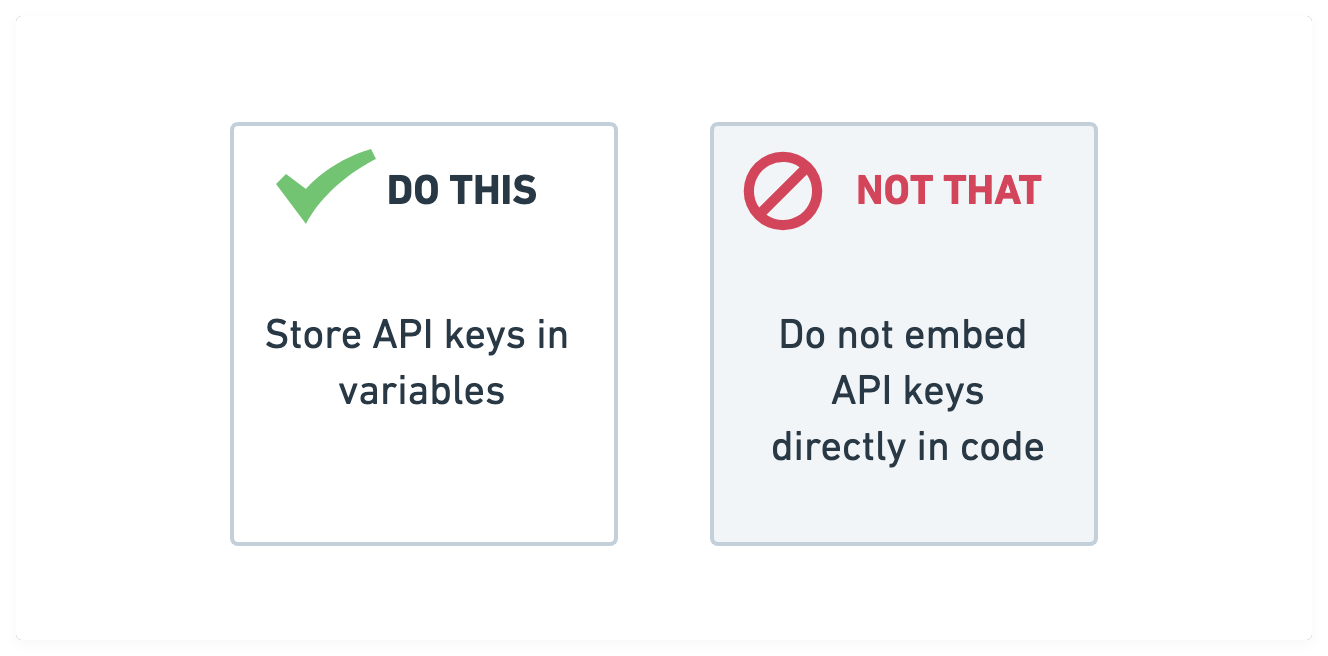
Generate Images With Dall E 2 And The Openai Api Real Python According to the state of secret sprawls 2025 report 1, gitguardian detected almost 24 million secrets in public github commits in 2024! in the following blog post i will explore different options of preventing leaking secrets in the first place and what to do when you were unable to prevent it. Deleted api keys stay in git history forever. this article shows you how to detect leaked secrets with gitleaks, remove them from history, and prevent future leaks with pre commit hooks and proper secret management. You will need to rewrite all the git commits that contain sensitive data in your repository history and prune empty commits that result. this process of removing your secrets creates new commits with new sha 1 ids. two methods that accomplish this are described below. Have you ever had that heart sinking moment when you realized you accidentally pushed sensitive secret keys to your github repository? guess what, you are not alone. i’ve been there… and not just once, but quite a few times. but the good news is that we can totally fix it without having our secrets linger in the repo’s history. This guide covers how to keep secrets out of your repository in the first place, with code examples and tooling that makes it automatic. when an api key ends up in a git repository, it's not just in the latest commit — it's in the commit history forever (unless you rewrite it). Turns out, any api key, even from a free tier, can be abused. someone could spam the service using your key, drain your usage limits, or use it in phishing schemes that get traced back to you.

Swerikcodes These 5 Github Repositories Are Crucial For Any Aspiring You will need to rewrite all the git commits that contain sensitive data in your repository history and prune empty commits that result. this process of removing your secrets creates new commits with new sha 1 ids. two methods that accomplish this are described below. Have you ever had that heart sinking moment when you realized you accidentally pushed sensitive secret keys to your github repository? guess what, you are not alone. i’ve been there… and not just once, but quite a few times. but the good news is that we can totally fix it without having our secrets linger in the repo’s history. This guide covers how to keep secrets out of your repository in the first place, with code examples and tooling that makes it automatic. when an api key ends up in a git repository, it's not just in the latest commit — it's in the commit history forever (unless you rewrite it). Turns out, any api key, even from a free tier, can be abused. someone could spam the service using your key, drain your usage limits, or use it in phishing schemes that get traced back to you.

Swerikcodes These 5 Github Repositories Are Crucial For Any Aspiring This guide covers how to keep secrets out of your repository in the first place, with code examples and tooling that makes it automatic. when an api key ends up in a git repository, it's not just in the latest commit — it's in the commit history forever (unless you rewrite it). Turns out, any api key, even from a free tier, can be abused. someone could spam the service using your key, drain your usage limits, or use it in phishing schemes that get traced back to you.

Cloud Monitoring With The 1 Status Page Aggregator Statusgator
Comments are closed.