Accessing Control Systems Securely Two Factor Authentication And
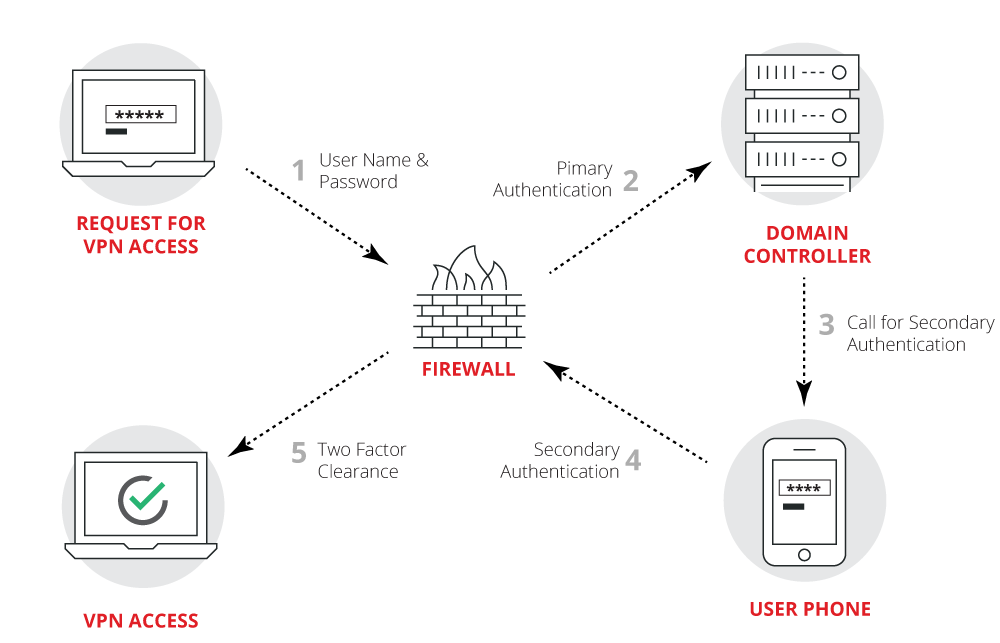
Accessing Control Systems Securely Two Factor Authentication And It is advisable to implement two factor authentication in all services considered critical, such as, for example, scada or auxiliary security services, and always where remote access is required. Welcome to our comprehensive guide on two factor authentication (2fa) in access control systems. in today’s digital age, securing user credentials and resources is of utmost importance.

Github Dark Data Twofactorauthentication In This Project We Integrating two factor authentication into access control in commercial settings makes security and surveillance systems much more effective. We describe a novel scheme which is provably secure if factoring is difficult and whose practical implementations are about two orders of magnitude faster than rsa based identification schemes. Zero trust operates on the premise that nothing is trusted initially, and identity validation is a constant requirement for accessing applications, data and infrastructure. this system is achieved by implementing mfa with risk based access controls where context driven factors define when extra authentication needs to be done. Two factor authentication (2fa) and access control authorization are two fundamental components of cybersecurity strategies aimed at safeguarding data and confidential information from unauthorized access.

Two Factor Authentication Examples For Enhanced Security Zero trust operates on the premise that nothing is trusted initially, and identity validation is a constant requirement for accessing applications, data and infrastructure. this system is achieved by implementing mfa with risk based access controls where context driven factors define when extra authentication needs to be done. Two factor authentication (2fa) and access control authorization are two fundamental components of cybersecurity strategies aimed at safeguarding data and confidential information from unauthorized access. Applying two factor authentication in an access control has a disadvantage. indeed, when using it, a delay of access is created and this can prevent a smooth working condition. Multi factor authentication is a security protocol that requires users to provide two or more verification factors to gain access to a system. unlike traditional methods that rely solely on a password, mfa compels users to prove their identity through various means. Defining multi factor authentication in a soc 2 context password plus a login screen is not a soc 2 access control strategy. in audit terms, multi factor authentication means a user must prove identity with at least two different factor types before getting access to a system, application, or data. This publication has been developed to provide guidance on what multi factor authentication is, different multi factor authentication methods that exist and why some multi factor authentication methods are more secure, and therefore more effective, than others.
Take The Security Of Your Access Control Operations To The Next Level Applying two factor authentication in an access control has a disadvantage. indeed, when using it, a delay of access is created and this can prevent a smooth working condition. Multi factor authentication is a security protocol that requires users to provide two or more verification factors to gain access to a system. unlike traditional methods that rely solely on a password, mfa compels users to prove their identity through various means. Defining multi factor authentication in a soc 2 context password plus a login screen is not a soc 2 access control strategy. in audit terms, multi factor authentication means a user must prove identity with at least two different factor types before getting access to a system, application, or data. This publication has been developed to provide guidance on what multi factor authentication is, different multi factor authentication methods that exist and why some multi factor authentication methods are more secure, and therefore more effective, than others.
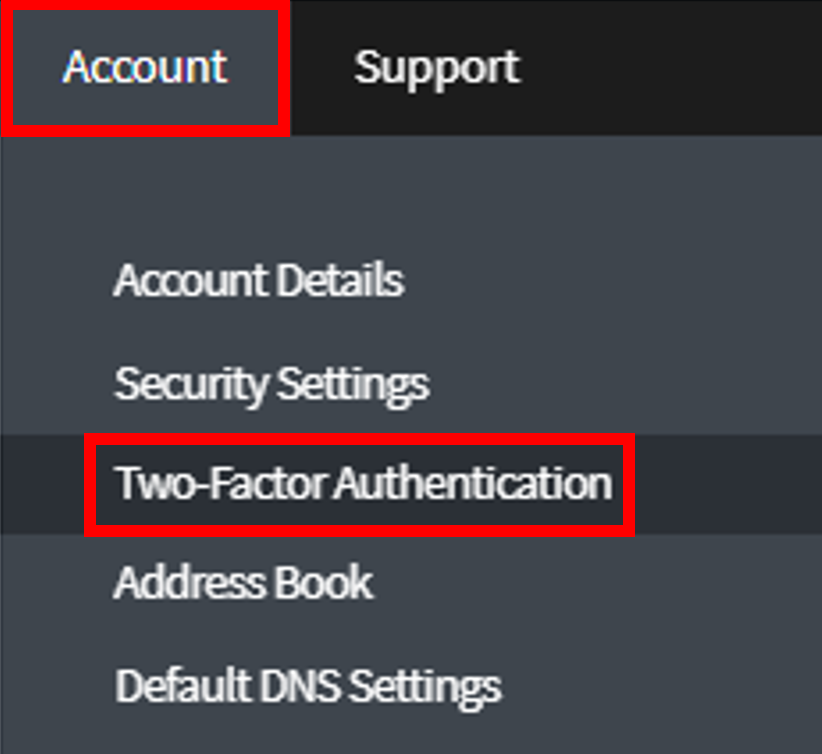
Enabling Two Factor Authentication For The Control Panel Customer Defining multi factor authentication in a soc 2 context password plus a login screen is not a soc 2 access control strategy. in audit terms, multi factor authentication means a user must prove identity with at least two different factor types before getting access to a system, application, or data. This publication has been developed to provide guidance on what multi factor authentication is, different multi factor authentication methods that exist and why some multi factor authentication methods are more secure, and therefore more effective, than others.
Comments are closed.