Access Device Via Mac Address And Ip Address Saswhat
Access Device Via Mac Address And Ip Address Saswhat In this article, we'll teach you how to access a device using its mac address and the precautions you should take to do so safely and legally. guide to connecting to a device using its mac address. In this post, we show you how to manually find a device or ip address using mac address but also we list the best tools to ease this process.
Access Device Via Mac Address And Ip Address Flojza Both mac address & ip address are unique identifiers that connect to those systems which have an internet connectivity. they differ in the aspect that mac address is a local area network address, whereas ip address is a global area network. In this blog post, i will explain what mac address and ip address are, why you might want to use mac address filtering, and how to do it on your router. i will also provide some frequently asked questions and answers related to this topic. In short, address resolution protocol, or arp, is a communication protocol that connects an ip address of a device to its mac address. typically, this protocol sends a request to all machines within the lan to check which device uses an ip address. Understanding how to find any device’s ip address, mac address, and other network connection details is fundamental for effective network management, security, and troubleshooting.

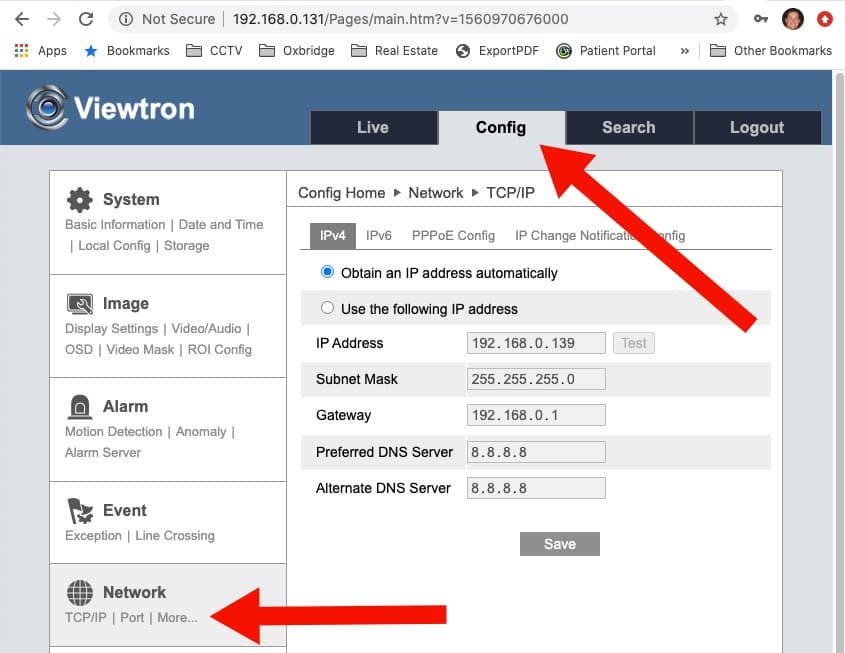
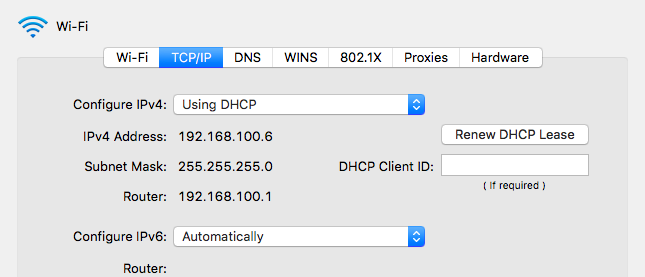
Access Device Via Mac Address And Ip Address Flojza In short, address resolution protocol, or arp, is a communication protocol that connects an ip address of a device to its mac address. typically, this protocol sends a request to all machines within the lan to check which device uses an ip address. Understanding how to find any device’s ip address, mac address, and other network connection details is fundamental for effective network management, security, and troubleshooting. To make your layer 4 browser access a certain layer 1 mac address, you have to create a static layer 1.5 arp entry for an imaginary ip address and then have your application access that imaginary ip. Every network connected device — computers, smartphones, tablets, smart home gadgets, and more — has an ip address and a unique mac address that identify it on your network. here's how to find that information on all the devices you might have lying around. To find the device or ip address associated with a mac (media access control) address, you can use several methods depending on your network setup and tools available. In this guide, you’ll learn what a mac address means, how it works behind the scenes, and how it differs from an ip address — but we’ll go one step further: you’ll see how this tiny detail shapes real world networking, security, and even your day to day development practices.

Access Device Via Mac Address Dudetop To make your layer 4 browser access a certain layer 1 mac address, you have to create a static layer 1.5 arp entry for an imaginary ip address and then have your application access that imaginary ip. Every network connected device — computers, smartphones, tablets, smart home gadgets, and more — has an ip address and a unique mac address that identify it on your network. here's how to find that information on all the devices you might have lying around. To find the device or ip address associated with a mac (media access control) address, you can use several methods depending on your network setup and tools available. In this guide, you’ll learn what a mac address means, how it works behind the scenes, and how it differs from an ip address — but we’ll go one step further: you’ll see how this tiny detail shapes real world networking, security, and even your day to day development practices.

How To Access Device Via Mac Address Gaisbook To find the device or ip address associated with a mac (media access control) address, you can use several methods depending on your network setup and tools available. In this guide, you’ll learn what a mac address means, how it works behind the scenes, and how it differs from an ip address — but we’ll go one step further: you’ll see how this tiny detail shapes real world networking, security, and even your day to day development practices.
Comments are closed.