A Issue Of The Credentials From The Issuer Download Scientific Diagram

A Issue Of The Credentials From The Issuer Download Scientific Diagram Issue of the credentials from the issuer from publication: integration of self sovereign identity in security systems | transactions over the internet have increased rapidly and so is. Despite being largely applied in several computing areas, sgx has limitations and performance issues that must be addressed for the development of secure solutions.

A Issue Of The Credentials From The Issuer Download Scientific Diagram Below is a diagram showing how verifiable credentials work. first the issuer writes a decentralized identifier (did) together with its public key (and any other cryptographic material needed for the issuer’s verifiable credentials) to a blockchain (or other sufficiently trusted public utility). This specification describes the extensible data model for verifiable credentials, how they can be secured from tampering, and a three party ecosystem for the exchange of these credentials that is composed of issuers, holders, and verifiers. Learncard sdk prepares an initial, unsigned version of the credential data. the issuer then directs the learncard sdk to apply a digital signature using the issuer's unique cryptographic key (often associated with their decentralized identifier or did). Formalizes messages used to issue a credential whether the credential is jwt oriented, json ld oriented, or zkp oriented. the general flow is similar, and this protocol intends to handle all of them.
Company Credentials Diagram Showing Five Steps Ppt Images Gallery Learncard sdk prepares an initial, unsigned version of the credential data. the issuer then directs the learncard sdk to apply a digital signature using the issuer's unique cryptographic key (often associated with their decentralized identifier or did). Formalizes messages used to issue a credential whether the credential is jwt oriented, json ld oriented, or zkp oriented. the general flow is similar, and this protocol intends to handle all of them. The following diagram illustrates a typical workflow when the wallet downloads a verifiable credential using the pre authorized code flow. how the authorization server issues the pre authorized code, in steps 2 and 3, is implementation specific. In this flow, the credential holder interacts with the issuer to request a verifiable credential as illustrated in the following diagram. the holder starts the flow by using a browser or native application to access the issuer’s web frontend. Formalizes messages used to issue a credential whether the credential is jwt oriented, json ld oriented, or zkp oriented. the general flow is similar, and this protocol intends to handle all of them. The credential issuer service is an oauth 2.0 protected service with two endpoints. the first endpoint is the credentials endpoint, which encompasses proofs, in time issuance and the option to defer the issuance.
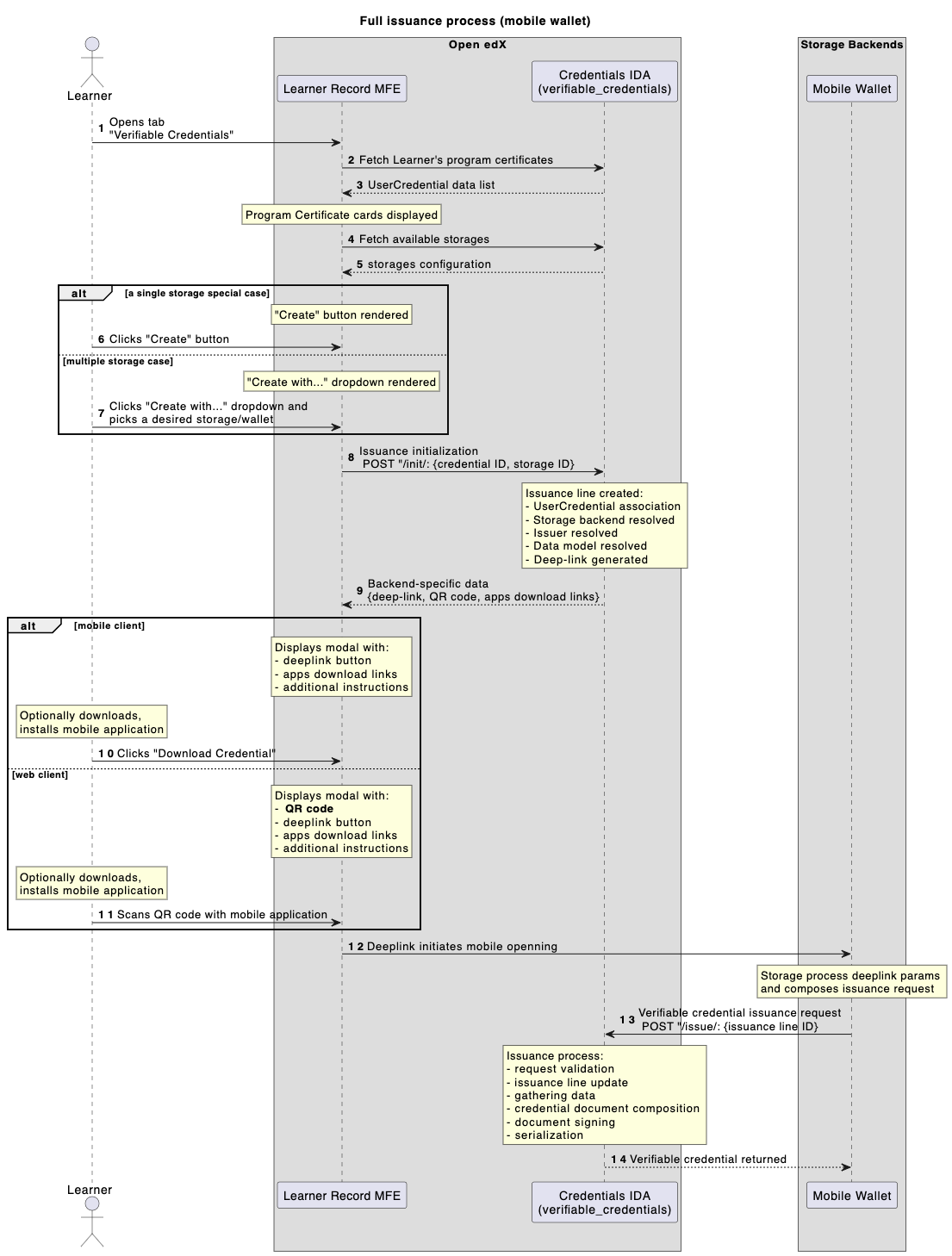
Implementation Details Edx Credentials 0 1 Documentation The following diagram illustrates a typical workflow when the wallet downloads a verifiable credential using the pre authorized code flow. how the authorization server issues the pre authorized code, in steps 2 and 3, is implementation specific. In this flow, the credential holder interacts with the issuer to request a verifiable credential as illustrated in the following diagram. the holder starts the flow by using a browser or native application to access the issuer’s web frontend. Formalizes messages used to issue a credential whether the credential is jwt oriented, json ld oriented, or zkp oriented. the general flow is similar, and this protocol intends to handle all of them. The credential issuer service is an oauth 2.0 protected service with two endpoints. the first endpoint is the credentials endpoint, which encompasses proofs, in time issuance and the option to defer the issuance.

Ted S Credentials Managed By Ted Issuer And Manager Download Formalizes messages used to issue a credential whether the credential is jwt oriented, json ld oriented, or zkp oriented. the general flow is similar, and this protocol intends to handle all of them. The credential issuer service is an oauth 2.0 protected service with two endpoints. the first endpoint is the credentials endpoint, which encompasses proofs, in time issuance and the option to defer the issuance.

Diagram Pdf
Comments are closed.