802 1x Network Basics

802 1x Pdf Computer Network Radius This guide provides an authoritative exploration of 802.1x, including core components, packet level flows, eapol frame types, authentication methods, fallback strategies, mdm uem deployment, advanced network segmentation, and future trends. You will learn the fundamentals of the 802.1x protocol and configuration, cisco ibns, configuring access for non supplicant devices, cisco ise deployment options, architectural components, considerations with 802.1x, and more.
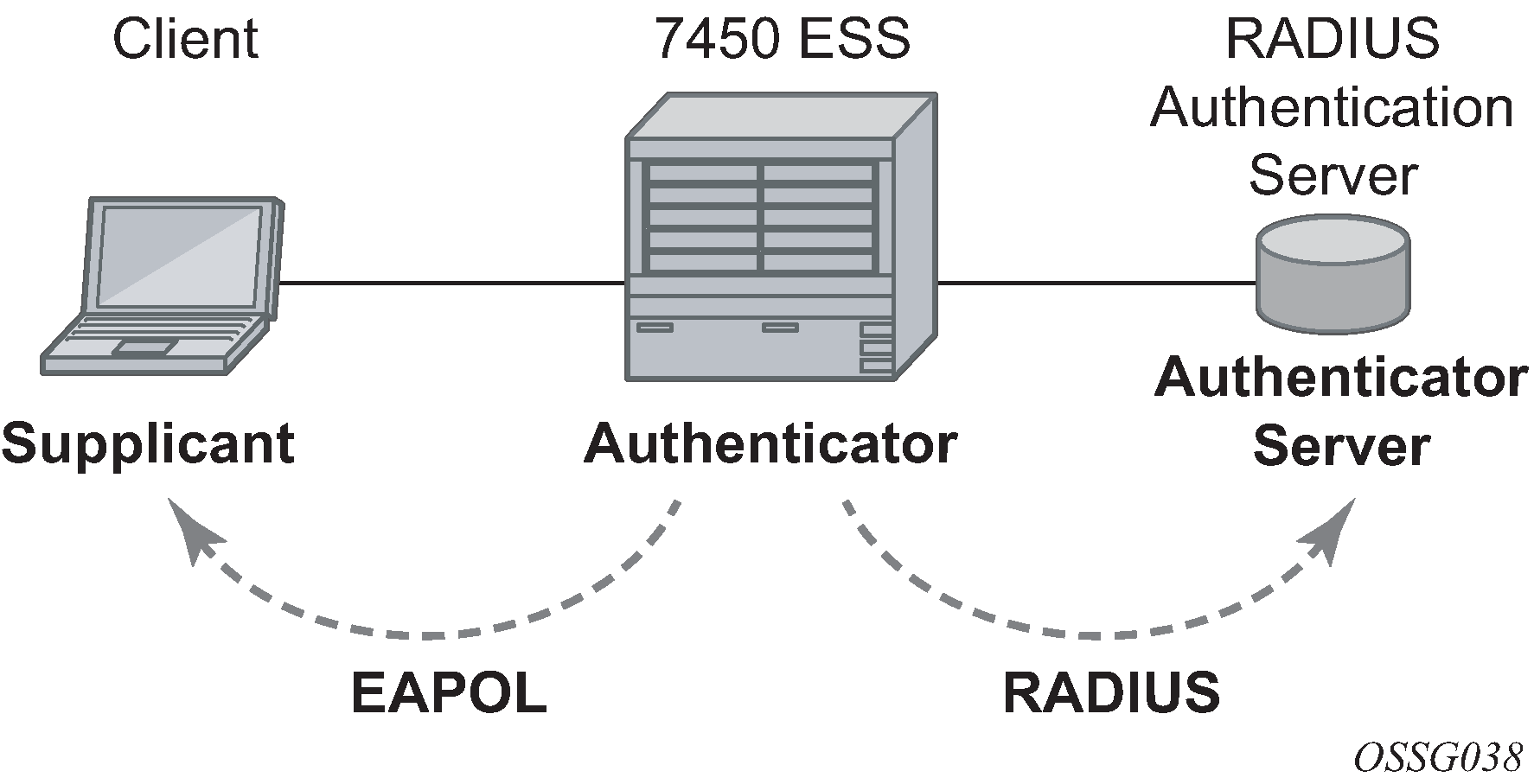
Aaa And 802 1x Authentication Ieee 802.1x is an ieee standard for port based network access control (pnac). it is part of the ieee 802.1 group of networking protocols. it provides an authentication mechanism to devices wishing to attach to a lan or wlan. In this lesson, we’ll break down the basics of 802.1x and how it controls who has access to wired network edge. why do we need ieee 802.1x? in the previous lesson, we discussed how the access layer of the network is typically its weakest point, as anyone can plug in a cable and gain access. 802,1x is an ieee standard for port based network access control (sometimes referred to as pnac or just nac). basically, it’s a layer 2 authentication method for devices that want to attach to a lan or wireless lan. What is 802.1x eap tls authentication? 802.1x authentication is many organizations’ first line of defense against online threats. this ieee standard defines how port based network access control should proceed, and it’s a common choice for enterprises.
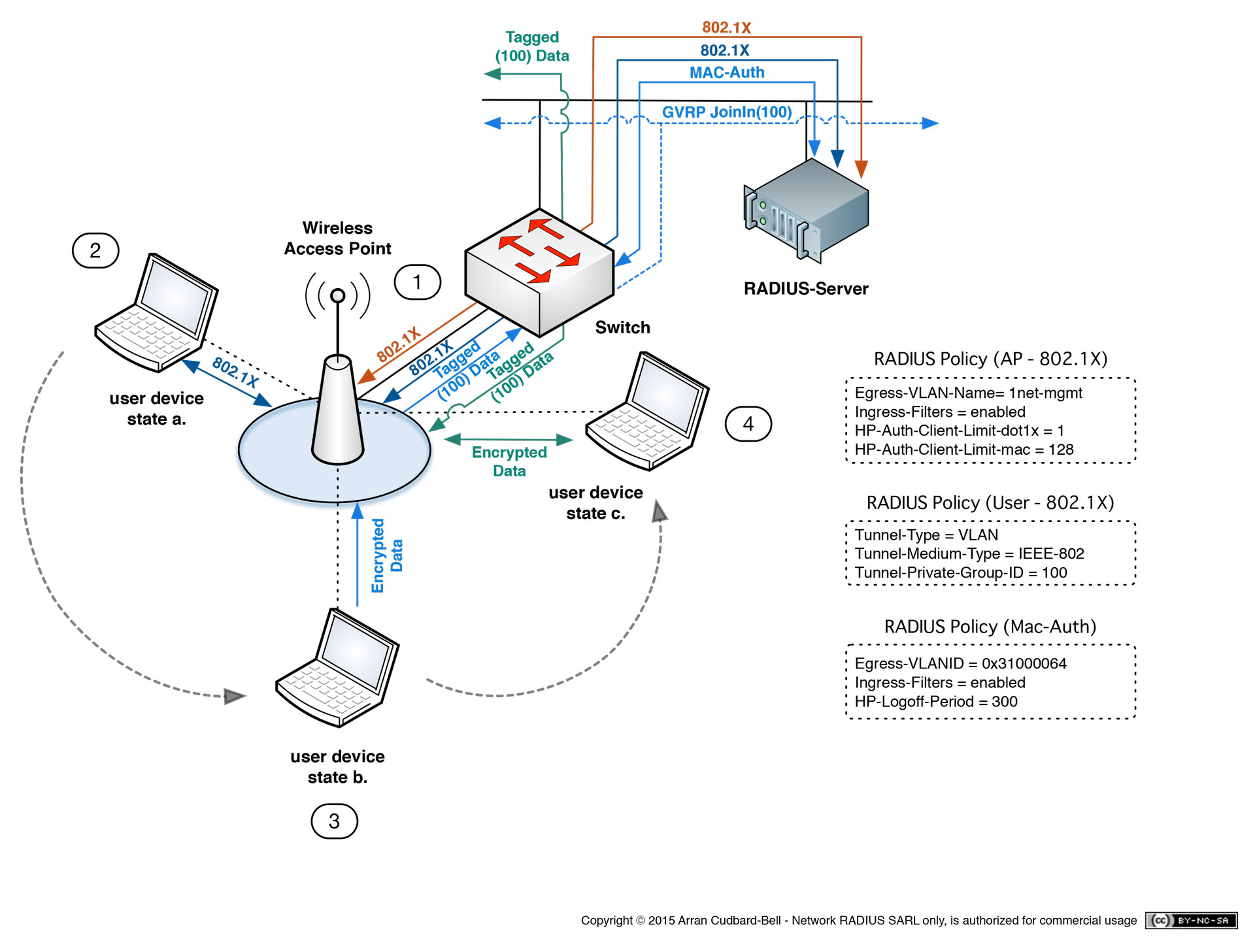
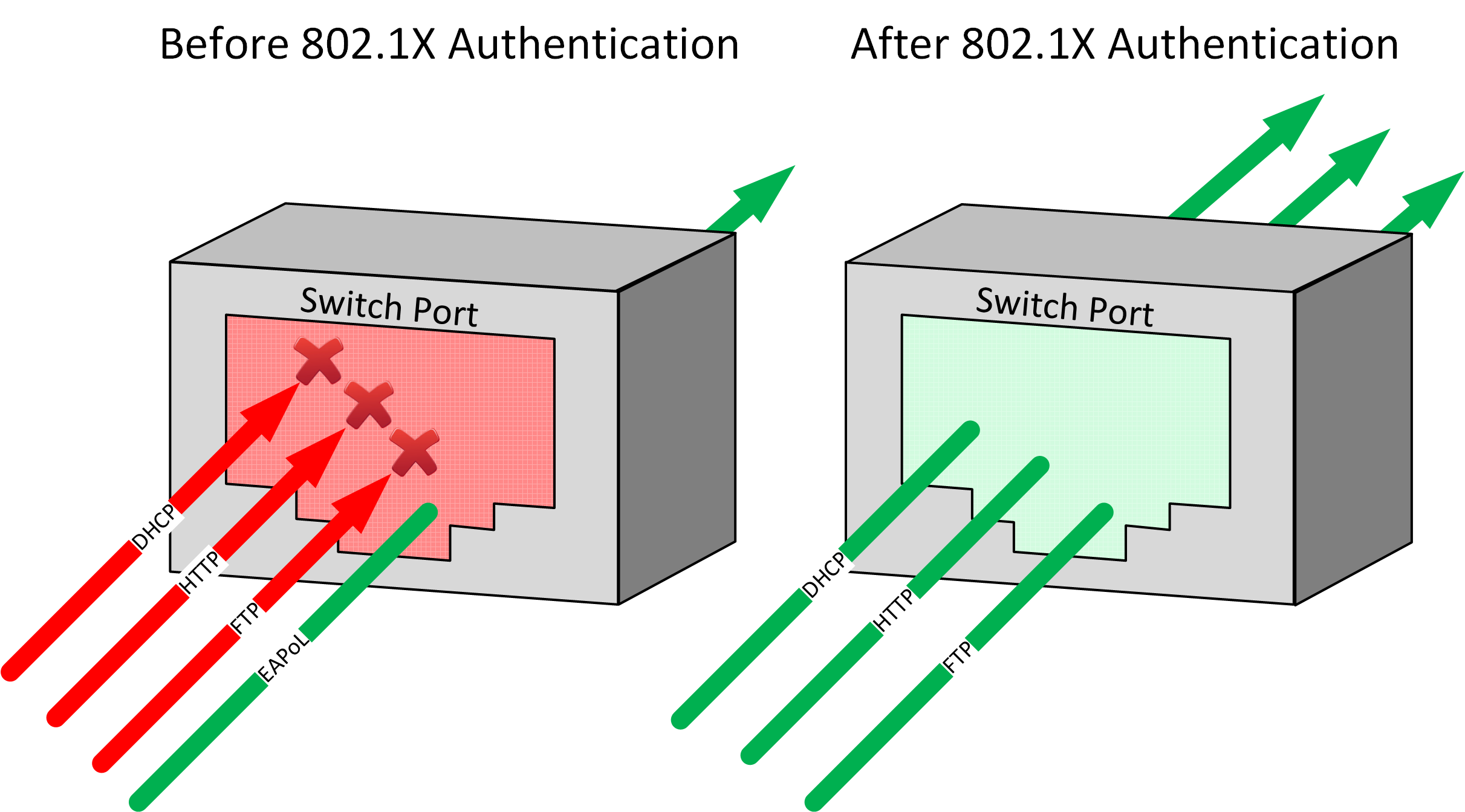
802 1x Freeradius Setup Networkradius 802,1x is an ieee standard for port based network access control (sometimes referred to as pnac or just nac). basically, it’s a layer 2 authentication method for devices that want to attach to a lan or wireless lan. What is 802.1x eap tls authentication? 802.1x authentication is many organizations’ first line of defense against online threats. this ieee standard defines how port based network access control should proceed, and it’s a common choice for enterprises. Learn what 802.1x authentication is, its main parts, how it works, and what you can do with it. learn why users can be authenticated, profiled, denied access, and restricted based on credentials. In this article, we'll delve into the basics of 802.1x and its role in enhancing network security. what is 802.1x? 802.1x is an ieee standard that defines port based network access control. it. 802.1x is used for port based authentication. when you think of a switchport, there is no authentication at all. with 802.1x, you have to authenticate first. Discover the ins and outs of 802.1x, a crucial protocol for network security, and learn how to implement it effectively in your organization.
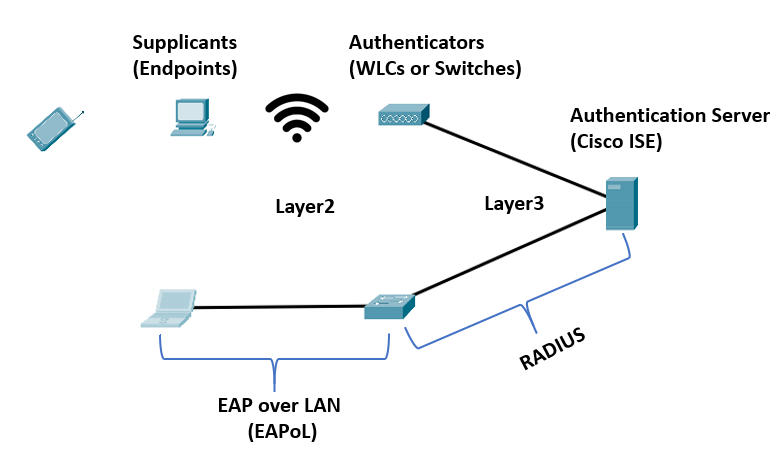
Ieee 802 1x Authentication Network Access Control Study Ccnp Learn what 802.1x authentication is, its main parts, how it works, and what you can do with it. learn why users can be authenticated, profiled, denied access, and restricted based on credentials. In this article, we'll delve into the basics of 802.1x and its role in enhancing network security. what is 802.1x? 802.1x is an ieee standard that defines port based network access control. it. 802.1x is used for port based authentication. when you think of a switchport, there is no authentication at all. with 802.1x, you have to authenticate first. Discover the ins and outs of 802.1x, a crucial protocol for network security, and learn how to implement it effectively in your organization.
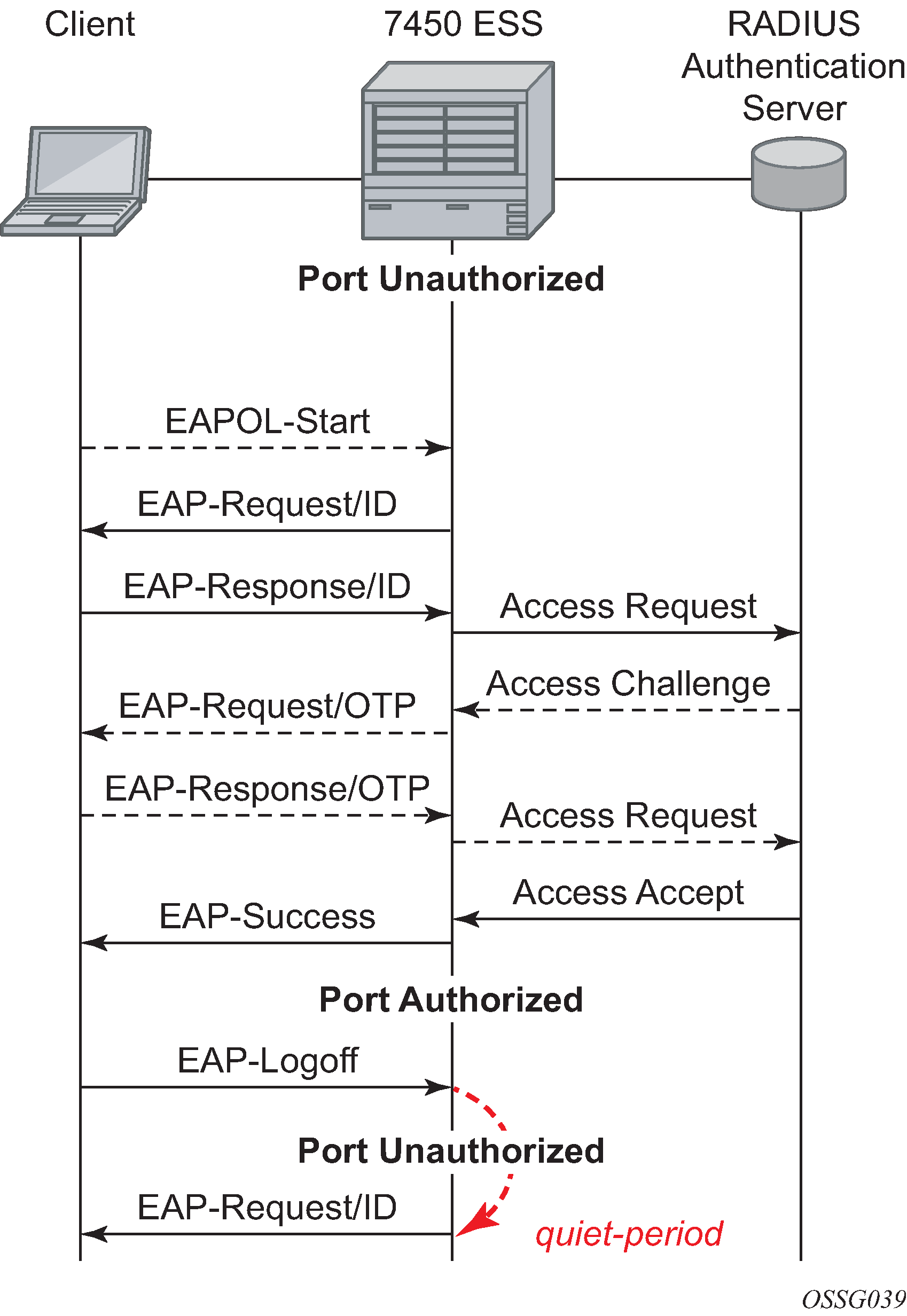
802 1x Basics 802.1x is used for port based authentication. when you think of a switchport, there is no authentication at all. with 802.1x, you have to authenticate first. Discover the ins and outs of 802.1x, a crucial protocol for network security, and learn how to implement it effectively in your organization.
802 1x Basics
Comments are closed.