6 3 4 Implement Intrusion Prevention

Implementing Intrusion Prevention With Snort In Pfsense Course Hero A deep dive into deploying intrusion prevention systems. we cover the difference between detection and active prevention, signature based rules, and how to harden your network against real time. Start snort on the wan interface. under the snort status column, select the arrow. wait for a checkmark to appear, indicating that snort was started successfully.
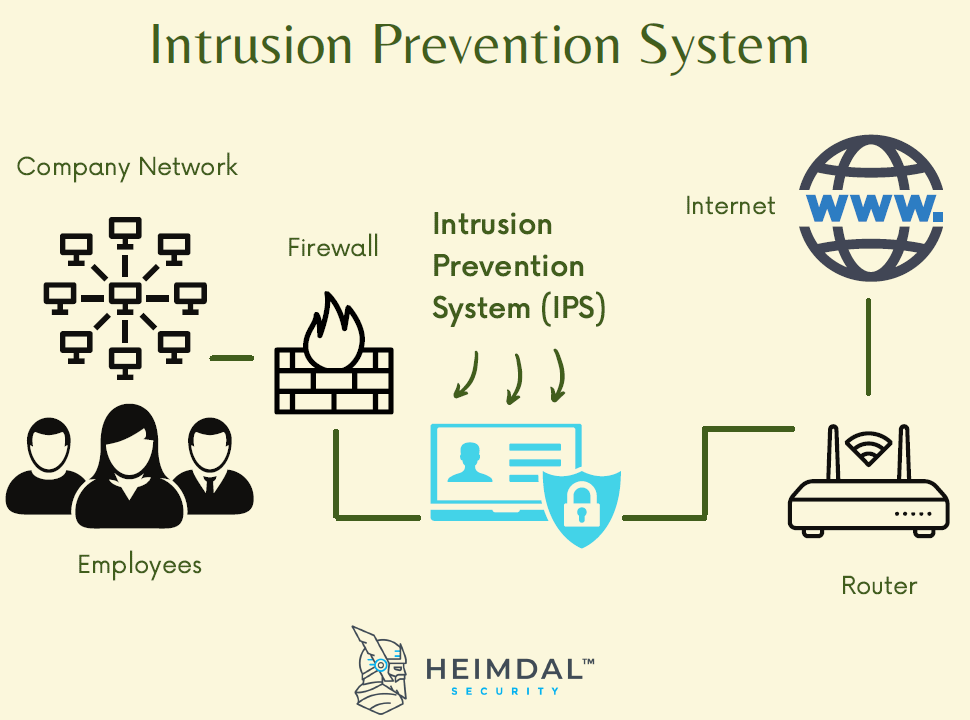
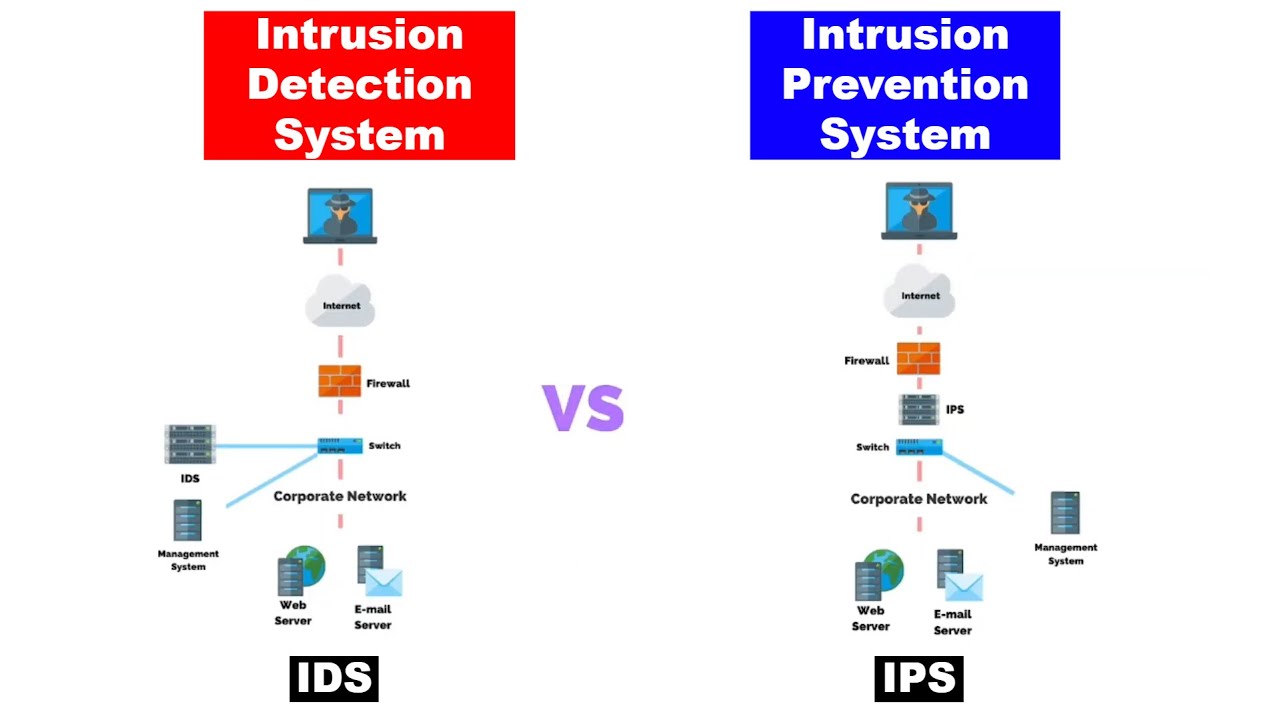
What Is An Intrusion Prevention System Ips This lab demonstrates how to implement intrusion prevention systems (ips) to actively detect and block malicious activity in real time, strengthening network security as part of a defense in depth strategy. 6.4.4 implementing intrusion prevention with pfsense configuration subject: cybersecurity cte 126 documents. An intrusion prevention system (ips) actively monitors network and system traffic to detect and block malicious activity in real time. it extends traditional ids capabilities by not only identifying threats but also automatically preventing attacks before they cause damage. 🔐 security lab 6.3.4 — implement intrusion prevention this lab demonstrates how to implement intrusion prevention systems (ips) to actively detect and block malicious activity in real time.
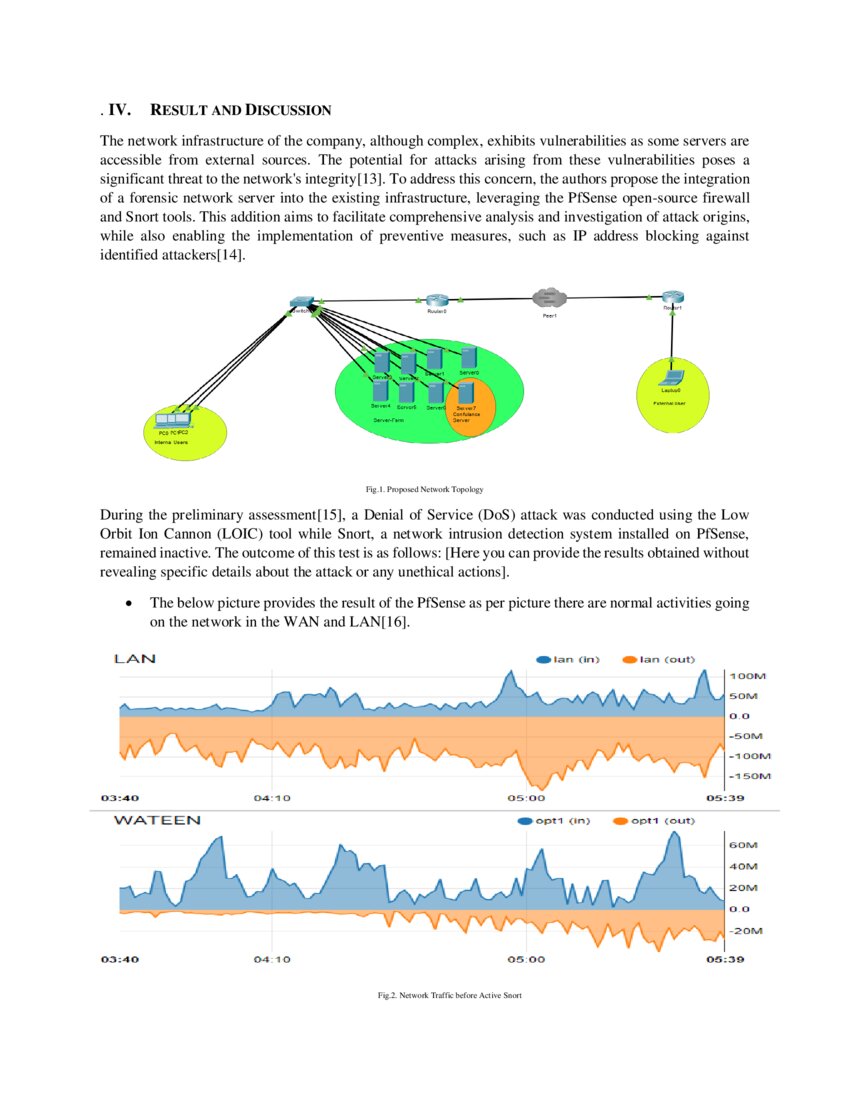
Implementing Snort Intrusion Prevention System Ips For Network An intrusion prevention system (ips) actively monitors network and system traffic to detect and block malicious activity in real time. it extends traditional ids capabilities by not only identifying threats but also automatically preventing attacks before they cause damage. 🔐 security lab 6.3.4 — implement intrusion prevention this lab demonstrates how to implement intrusion prevention systems (ips) to actively detect and block malicious activity in real time. In an effort to protect your network from security threats and hackers, you have add. Use pfsense's snort to complete the following:sign in to pfsense using:username: adminpassword: p@ssw0rd (zero)enable downloading of the following:snort free. As an implementation of the ieee 802.2 3 standards, the ethernet frame provides mac addressing and error checking. the layer 2 addressing provided by ethernet supports unicast, multicast, and broadcast communications. Identifying critical assets: begin by identifying the critical assets within your network. these could include servers containing sensitive data, customer information databases, or proprietary.

Intrusion Detection In an effort to protect your network from security threats and hackers, you have add. Use pfsense's snort to complete the following:sign in to pfsense using:username: adminpassword: p@ssw0rd (zero)enable downloading of the following:snort free. As an implementation of the ieee 802.2 3 standards, the ethernet frame provides mac addressing and error checking. the layer 2 addressing provided by ethernet supports unicast, multicast, and broadcast communications. Identifying critical assets: begin by identifying the critical assets within your network. these could include servers containing sensitive data, customer information databases, or proprietary.
What Is A Network Intrusion Detection System At Duane Gordon Blog As an implementation of the ieee 802.2 3 standards, the ethernet frame provides mac addressing and error checking. the layer 2 addressing provided by ethernet supports unicast, multicast, and broadcast communications. Identifying critical assets: begin by identifying the critical assets within your network. these could include servers containing sensitive data, customer information databases, or proprietary.

Implement Intrusion Prevention With Snort On Pfsense Course Hero
Comments are closed.