55 Side Channel Analysis Information Security 5 Secure Systems Engineering

Performing Side Channel Attack Keeloq25c3 2 Pdf Information And Welcome to 'information security 5 secure systems engineering' course !this lecture provides a broad overview of side channel analysis, a powerful class of a. Noc: information security 5 secure systems engineering, iit madras prof. chester rebeiro.
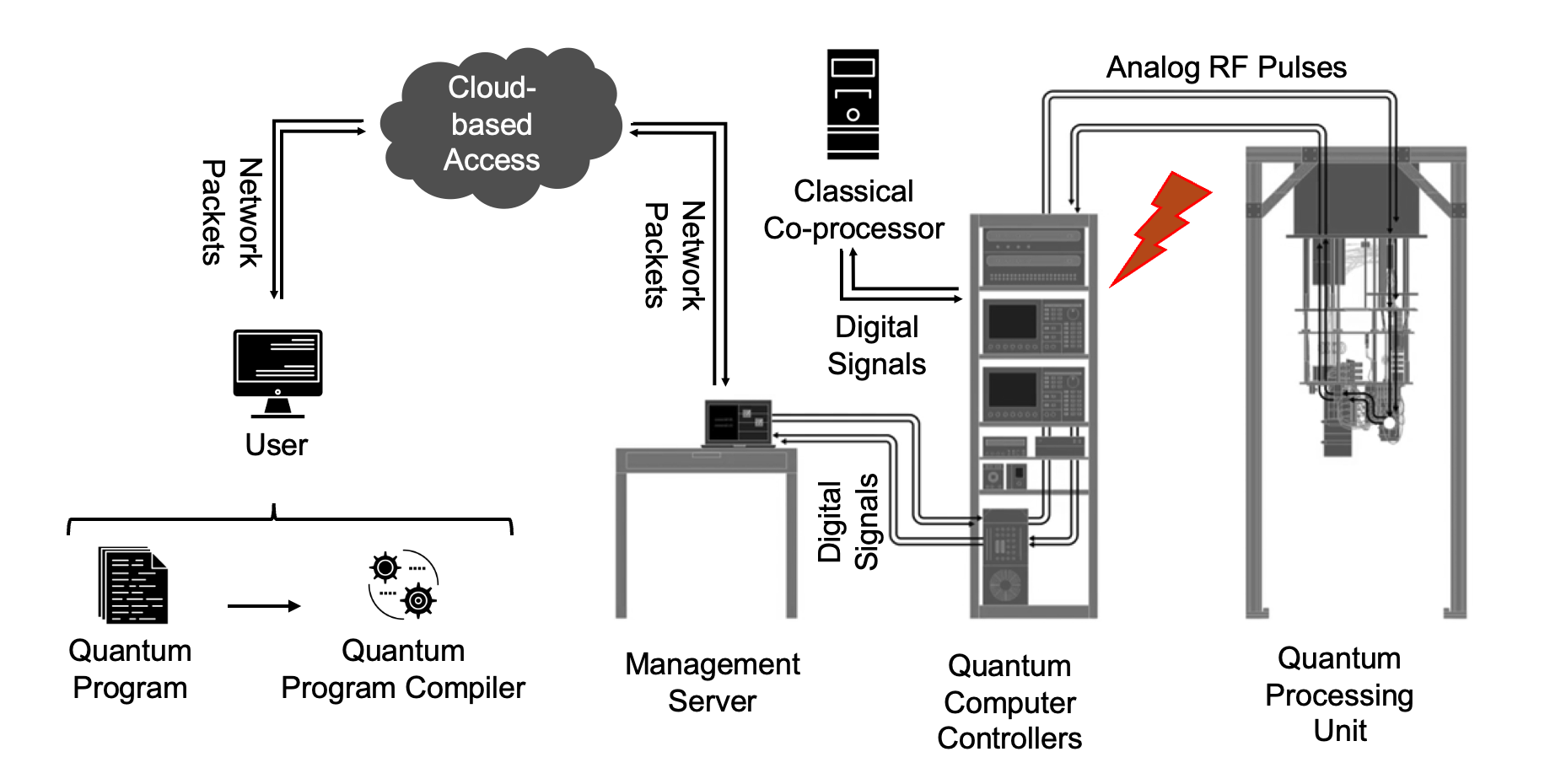
Quantum Computer Side Channel And Fault Injection Security Analysis Hello and welcome to this video lecture in the course for secure systems engineering, in this particular video lecture we will be looking at a brief introduction to side channel analysis. Lecture 55 side channel analysis 1x search within video (e.g: "algorithm", "compiler" or "coding theory") speech recogniser status: not recognising search and play video home previous next. This repository contains comprehensive study materials for the nptel course secure systems engineering offered by iit madras. the resources included here are useful for students and professionals looking to deepen their understanding of secure system design and implementation. The videos discuss various threats, including buffer overflows, integer overflows, memory management issues, discretionary and mandatory access control, side channel attacks, hardware trojans,.
Side Channel Analysis Of Embedded Systems An Efficient Algorithmic This repository contains comprehensive study materials for the nptel course secure systems engineering offered by iit madras. the resources included here are useful for students and professionals looking to deepen their understanding of secure system design and implementation. The videos discuss various threats, including buffer overflows, integer overflows, memory management issues, discretionary and mandatory access control, side channel attacks, hardware trojans,. We will see how these vulnerabilities can arise from simple programming flaws like a buffer that overflows, to complex application runtime characteristics that get manifested through side channels such as the execution time and power consumption of the device. Both papers study implementations on a cortex m4: the cortex family is well used studied in the context of symmetric crypto implementations and there is ample evidence that no serious side channel security is possible. Side channel analysis (sca) is a class of implementation level cryptanalytic techniques that exploit unintended information leakage from hardware or software systems to recover secret data such as cryptographic keys, model parameters, or confidential user information. This thorough research gives a full evaluation of side channel assaults, concentrating on their methodology, effect, and the increasing realm of response tactics. understanding the subtleties of side channel attacks is crucial to strengthening the security of cryptographic systems.

Electromagnetic Side Channel Analysis Of Cryptographically Protected We will see how these vulnerabilities can arise from simple programming flaws like a buffer that overflows, to complex application runtime characteristics that get manifested through side channels such as the execution time and power consumption of the device. Both papers study implementations on a cortex m4: the cortex family is well used studied in the context of symmetric crypto implementations and there is ample evidence that no serious side channel security is possible. Side channel analysis (sca) is a class of implementation level cryptanalytic techniques that exploit unintended information leakage from hardware or software systems to recover secret data such as cryptographic keys, model parameters, or confidential user information. This thorough research gives a full evaluation of side channel assaults, concentrating on their methodology, effect, and the increasing realm of response tactics. understanding the subtleties of side channel attacks is crucial to strengthening the security of cryptographic systems.
Comments are closed.