50 Vulnerability Examples 2026

50 Vulnerability Examples 2026 Whether organizations are planning patching capacity, writing coordinated vulnerability disclosure reports, or developing detection signatures for siem, edr, or ids platforms, understanding the expected volume of vulnerabilities enables better resource allocation and strategic decision making. From the fbi breach to the darksword iphone exploit, these are the biggest cyber attacks and security failures that have shaped 2026 so far.

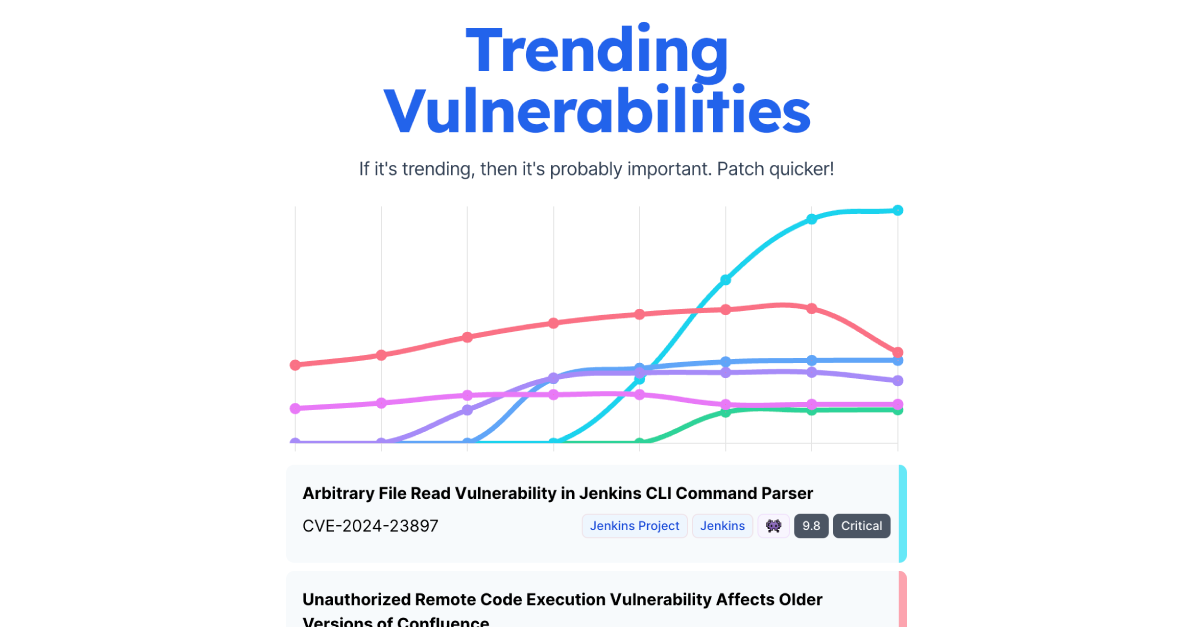
Threatscope Vulnerability Trends 05 11 Jan 2026 Read the 2026 vulnerability report. discover why exploit velocity outpaced patching and how to secure edge devices against zero day threats. The vulnerability statistics page is updated daily and is designed to be easily screenshotable and shareable. The cybersecurity landscape in 2026 has been marked by an unprecedented surge in critical vulnerabilities, with over 21,500 cves disclosed in the first half of the year alone, representing a 16 18% increase compared to 2024. For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—cisa maintains the authoritative source of vulnerabilities that have been exploited in the wild.
2026 Cyber Security Vulnerability Stats Trends Securityvulnerability Io The cybersecurity landscape in 2026 has been marked by an unprecedented surge in critical vulnerabilities, with over 21,500 cves disclosed in the first half of the year alone, representing a 16 18% increase compared to 2024. For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—cisa maintains the authoritative source of vulnerabilities that have been exploited in the wild. This article covers the key vulnerability statistics for 2026 across discovery, exploitation, industry impact, and notable cve s, with a focus on what the numbers mean for how your team prioritizes and responds. Identify, define, and catalog publicly disclosed cybersecurity vulnerabilities. there are currently over 324,000 cve records accessible via download or keyword search above. the cve program partners with community members worldwide to grow cve content and expand its usage. Discover the top cybersecurity threats shaping 2026—from ai driven attacks to supply chain risks—with key stats, real world examples, and actionable defense strategies. At the end of last year, ibm security experts shared their predictions with ibm think, forecasting some of the cyberthreats and solutions that are already trending in 2026–including new risks from artificial intelligence (ai), new challenges to identity management and more.
Comments are closed.