5 Expert Tips For Developers To Avoid Cyber Attacks
5 Expert Tips For Developers To Avoid Cyber Attacks This guide dives into essential cybersecurity principles, explains common vulnerabilities like sql injection, and offers actionable strategies to fortify your code. Oliver green, the author of autoclicker.io and a cyber security specialist, offers five suggestions for game publishers on how to best safeguard their developers’ online activity.

How To Prevent Cyber Attacks Here Are 5 Tips World Economic Forum In today’s digital landscape, cybersecurity isn’t just a feature — it’s a fundamental responsibility. as developers, we hold the keys to protecting sensitive data and maintaining user trust. Discover expert approved cybersecurity practices to safeguard your software against modern threats. real world examples and actionable tips inside. Utilize full stack development skills to prevent cyber attacks by implementing secure coding practices, validating user inputs, strengthening authentication and authorization mechanisms, and. For developers handling sensitive code, client data, or intellectual property, understanding and implementing robust cybersecurity practices is non negotiable. this guide provides practical advice and tools to help remote developers safeguard their digital environment.
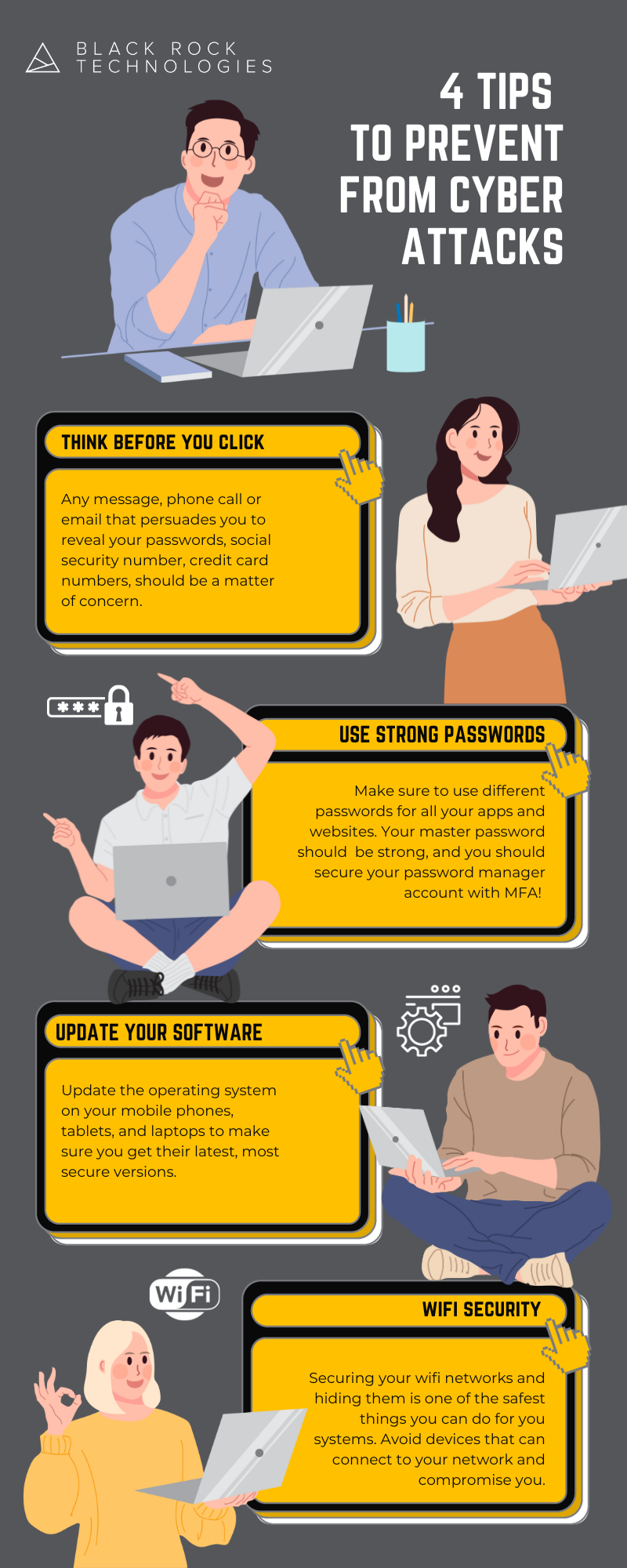
4 Tips To Prevent Cyber Attacks Black Rock Technologies Utilize full stack development skills to prevent cyber attacks by implementing secure coding practices, validating user inputs, strengthening authentication and authorization mechanisms, and. For developers handling sensitive code, client data, or intellectual property, understanding and implementing robust cybersecurity practices is non negotiable. this guide provides practical advice and tools to help remote developers safeguard their digital environment. This statistic highlights the urgent need for development teams to adopt cybersecurity best practices tailored to remote work environments. as cyber threats grow in complexity and frequency, remote dev teams must proactively strengthen defenses to protect critical assets from breaches, ransomware, and data leaks. In a recent forbes article, stoyan mitov, ceo of dreamix, a custom software development company, dives into five best practices for ensuring security in software development in 2024 including zero trust architecture, devsecops, advanced threat intelligence, quantum safe cryptography, and human centric security. By integrating secure coding practices, developers can protect applications from attacks. input validation, parameterized queries, encryption, and error handling are vital components of secure coding. Learn secure coding practices to protect applications, prevent cyber attacks, and build robust, safe, and reliable software.

4 Tips To Prevent Cyber Attacks E Learning Infographics This statistic highlights the urgent need for development teams to adopt cybersecurity best practices tailored to remote work environments. as cyber threats grow in complexity and frequency, remote dev teams must proactively strengthen defenses to protect critical assets from breaches, ransomware, and data leaks. In a recent forbes article, stoyan mitov, ceo of dreamix, a custom software development company, dives into five best practices for ensuring security in software development in 2024 including zero trust architecture, devsecops, advanced threat intelligence, quantum safe cryptography, and human centric security. By integrating secure coding practices, developers can protect applications from attacks. input validation, parameterized queries, encryption, and error handling are vital components of secure coding. Learn secure coding practices to protect applications, prevent cyber attacks, and build robust, safe, and reliable software.

How To Prevent Cyber Attacks Cybersecurity Tips Actual Human By integrating secure coding practices, developers can protect applications from attacks. input validation, parameterized queries, encryption, and error handling are vital components of secure coding. Learn secure coding practices to protect applications, prevent cyber attacks, and build robust, safe, and reliable software.
Comments are closed.