4 Pseudonymization Techniques For Privacy Enhancing Technologies
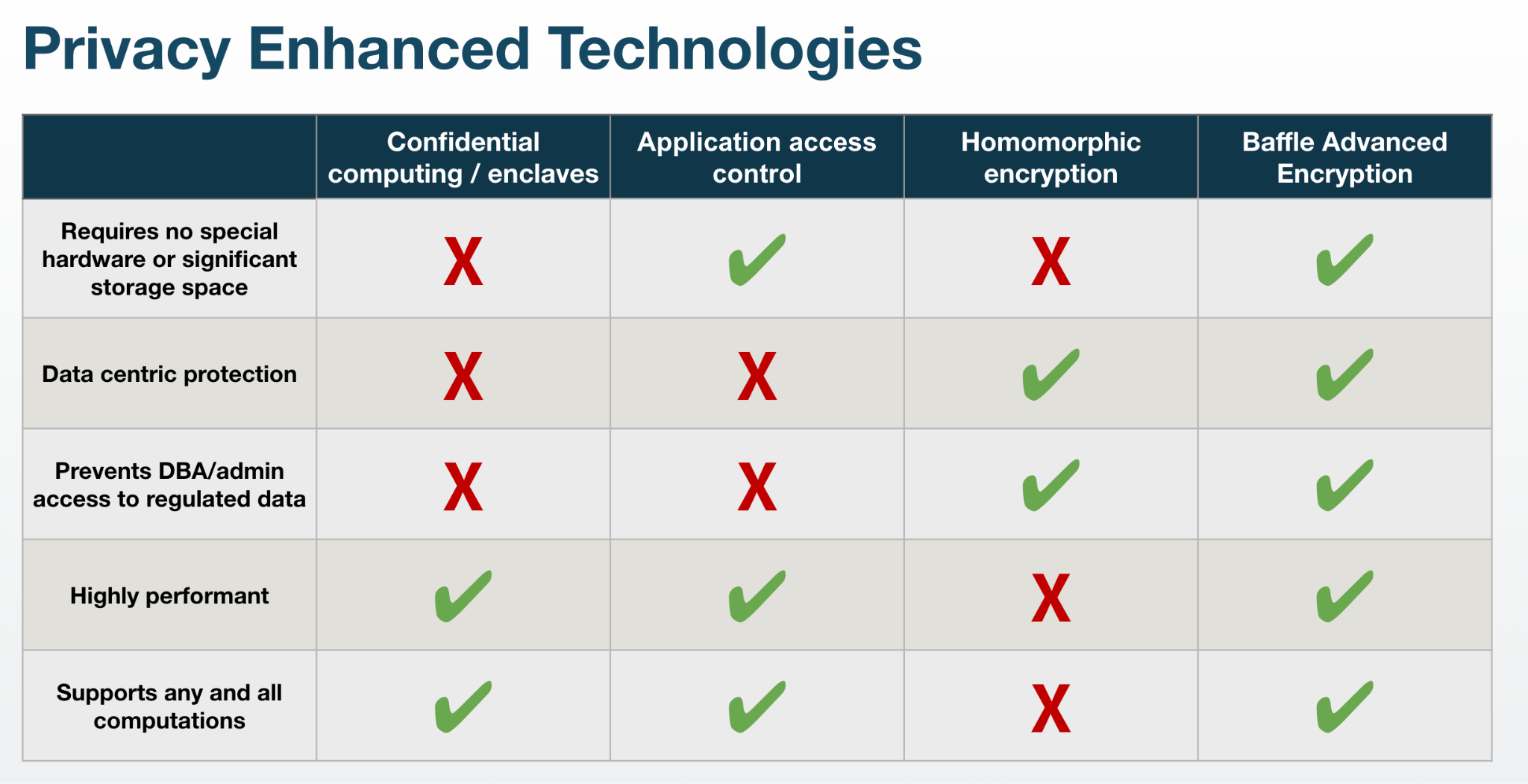
Privacy Enhanced Computation Technologies Advantages And Disadvantages This may include implementing pseudonymization techniques alongside other privacy enhancing measures such as access controls, data anonymization, and privacy by design principles. Explore further advanced pseudonymisation techniques which were not covered in prior enisa’s work, based on cryptographic algorithms and privacy enhancing technologies.
Privacy Enhancing Computation Powerpoint And Google Slides Template Techniques include data masking, generalization, and aggregation, ensuring that original data cannot be reconstructed. methods may include tokenization, encryption, or hashing, ensuring that data can be re associated with its original subject when necessary. Explore key anonymization and pseudonymization techniques vital for data privacy, compliance with gdpr, and enhancing security in insurance and data protection. The most efficient psi protocols are highly scalable and use a variety of methods, including other privacy enhancing techniques such as hashing or homomorphic encryption. This research was conducted to find out information technology adoption in msmes in blitar city.

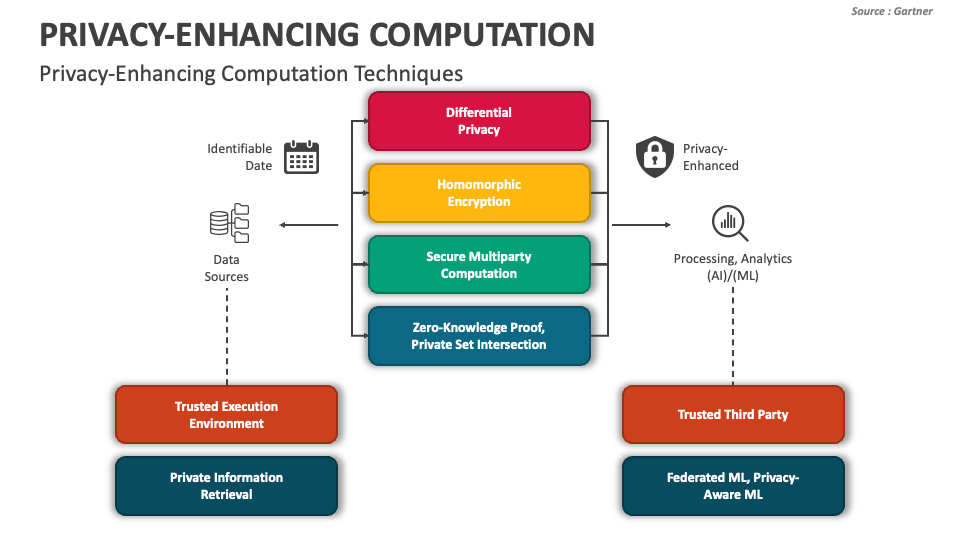
Protecting Personal Data With Pseudonymization Datatas The most efficient psi protocols are highly scalable and use a variety of methods, including other privacy enhancing techniques such as hashing or homomorphic encryption. This research was conducted to find out information technology adoption in msmes in blitar city. The use of privacy enhancing technologies, such as anonymization and pseudonymization, can significantly reduce the risk of data misuse and protect personal information. This report will focus on these technical approaches; specifically, the report will define and categorize a set of tools and techniques classified as privacy enhancing technologies (pets) that help maintain the security and privacy of data. Pseudonymization is a data protection technique that replaces identifiable information within a dataset with pseudonyms. this process reduces the risk of re identification while allowing the data to remain useful for analysis and processing. The future of data protection lies in sophisticated combinations of these techniques, enhanced by emerging technologies like homomorphic encryption and federated learning.

4 Pseudonymization Techniques For Privacy Enhancing Technologies The use of privacy enhancing technologies, such as anonymization and pseudonymization, can significantly reduce the risk of data misuse and protect personal information. This report will focus on these technical approaches; specifically, the report will define and categorize a set of tools and techniques classified as privacy enhancing technologies (pets) that help maintain the security and privacy of data. Pseudonymization is a data protection technique that replaces identifiable information within a dataset with pseudonyms. this process reduces the risk of re identification while allowing the data to remain useful for analysis and processing. The future of data protection lies in sophisticated combinations of these techniques, enhanced by emerging technologies like homomorphic encryption and federated learning.

4 Pseudonymization Techniques For Privacy Enhancing Technologies Pseudonymization is a data protection technique that replaces identifiable information within a dataset with pseudonyms. this process reduces the risk of re identification while allowing the data to remain useful for analysis and processing. The future of data protection lies in sophisticated combinations of these techniques, enhanced by emerging technologies like homomorphic encryption and federated learning.
Comments are closed.