12 4 Kickoff For Secure Software Composition Analysis
Software Composition Analysis For Custom Applications Red Hawk 12 4 kickoff for secure software composition analysis gitlab unfiltered 42k subscribers subscribe. Learn what software composition analysis (sca) is, how sca tools work, and how cloudsec and appsec teams use sca to manage open source and supply chain risk.

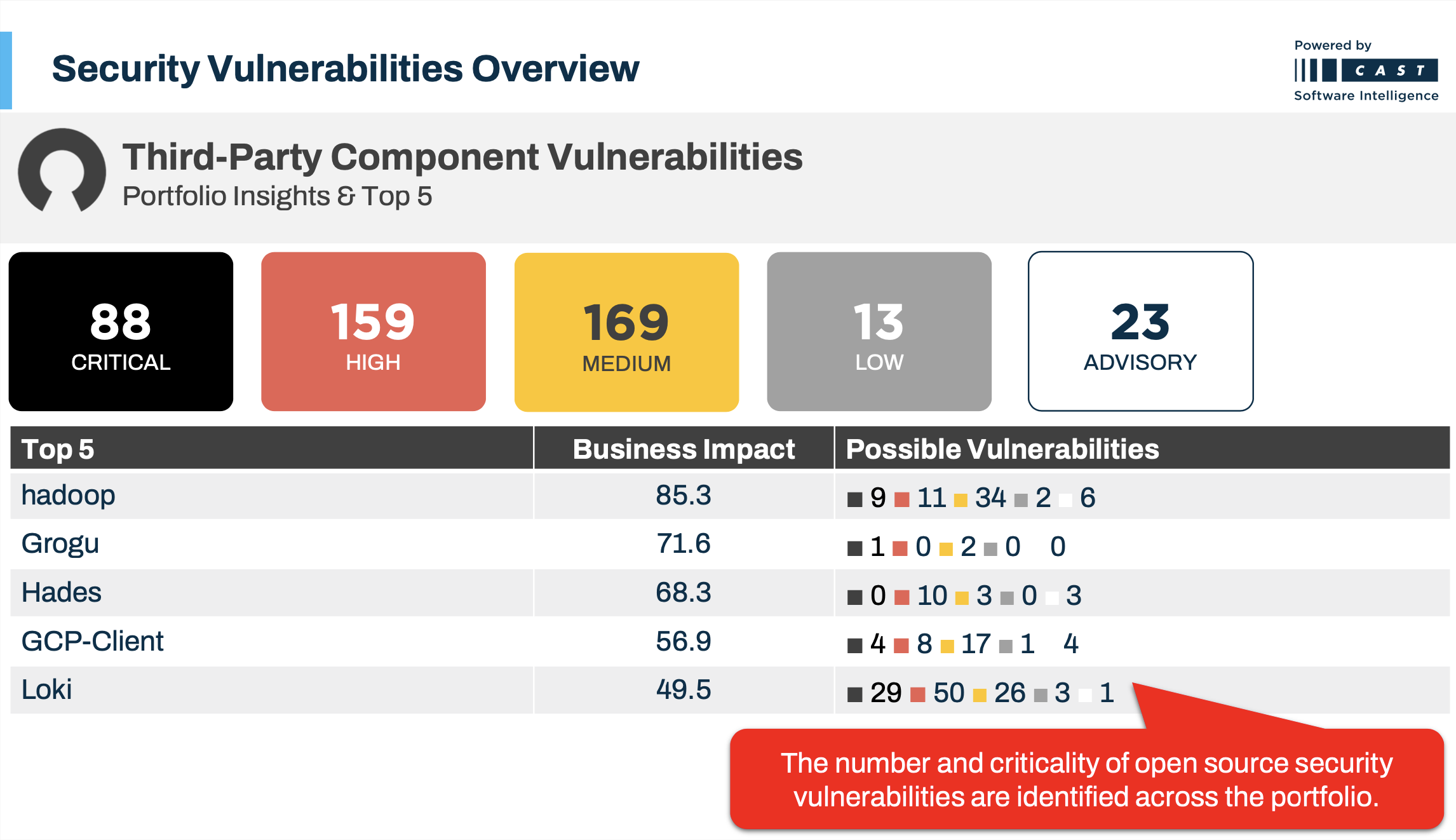
Protecting Your Software With Component Analysis Apex The College The goal of sca is to identify potential security vulnerabilities, licensing issues, or outdated components in the software being developed or used. this article focuses on discussing software composition analysis (sca) in detail. Software composition analysis (sca) is the process of analyzing software—most commonly software built from open source components—to ensure that the components are up to date, secure and in license compliance. The composition analysis group at gitlab is charged with developing solutions which perform container scanning, and software composition analysis. see the exhaustive list of projects the group maintains. In this blog, i will explore the top 10 sca tools for 2025, highlighting their primary use cases and key features. along with practical insights, i’ll share brief hands on experiences to help you understand how each tool fits into modern software security workflows.

Software Composition Analysis Beginners Advanced Practitioners The composition analysis group at gitlab is charged with developing solutions which perform container scanning, and software composition analysis. see the exhaustive list of projects the group maintains. In this blog, i will explore the top 10 sca tools for 2025, highlighting their primary use cases and key features. along with practical insights, i’ll share brief hands on experiences to help you understand how each tool fits into modern software security workflows. Black duck helps organizations secure their software supply chain by providing deep visibility into open source components, licenses, and vulnerabilities. black duck solutions help ensure compliance, accelerate development, provide clarity into ai coding, and prevent costly security events. Learn how software composition analysis (sca) safeguards applications by identifying risks, ensuring compliance, and upholding software quality. First, we detail common open source risks enterprises encounter. then, we provide 12 practices to augment your sca strategy while minimizing friction with developers. in the end, we include a checklist you can follow and dev friendly tool recommendations. In this article, we'll explore what software composition analysis is and how it fits into your organization’s broader security strategy. we'll walk through how sca works and discuss its benefits and challenges.

Software Composition Analysis Oss Risk Management Barrier Barrier Black duck helps organizations secure their software supply chain by providing deep visibility into open source components, licenses, and vulnerabilities. black duck solutions help ensure compliance, accelerate development, provide clarity into ai coding, and prevent costly security events. Learn how software composition analysis (sca) safeguards applications by identifying risks, ensuring compliance, and upholding software quality. First, we detail common open source risks enterprises encounter. then, we provide 12 practices to augment your sca strategy while minimizing friction with developers. in the end, we include a checklist you can follow and dev friendly tool recommendations. In this article, we'll explore what software composition analysis is and how it fits into your organization’s broader security strategy. we'll walk through how sca works and discuss its benefits and challenges.
Comments are closed.