006 Host Security Application Management Overview

Module 6 Application Deployment And Security Pdf Cloud Computing Cybersecurity course 3 unit 1 video 6. This document discusses managing data, application, and host security. it covers topics like application security methods, data security goals and techniques, managing device and host security, and mobile security controls.
Ppt Host And Application Security Powerpoint Presentation Free Explore key strategies for securing cloud infrastructure at host, network, and application levels, focusing on hardening, monitoring, and encryption. Hardware security module (hsm) is similar to tpm modules, but hsms are removable or external devices that can be added later. both are used for encryption using rsa keys. Systematically protect your cloud container engine (cce) and on premises container clusters throughout their lifecycles with our asset management, image security, cluster security, and runtime intrusion detection features. Host security overview: host security refers to the protection of physical and virtual servers (hosts) from vulnerabilities and attacks. this includes the implementation of security measures at the operating system and hardware levels.
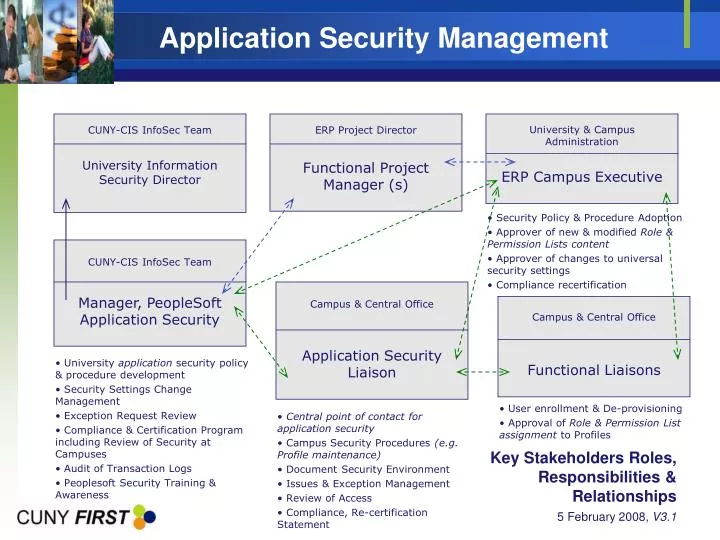
Ppt Application Security Management Powerpoint Presentation Free Systematically protect your cloud container engine (cce) and on premises container clusters throughout their lifecycles with our asset management, image security, cluster security, and runtime intrusion detection features. Host security overview: host security refers to the protection of physical and virtual servers (hosts) from vulnerabilities and attacks. this includes the implementation of security measures at the operating system and hardware levels. This document discusses managing data, application, and host security. it covers topics like application security methods, data security goals and techniques, managing device and host security, and mobile security controls. This guide offers an overview of the security development life cycle (secdl) and host of security features supported by nutanix. it also demonstrates how nutanix complies with security regulations to streamline infrastructure security management. Network security starts with securing the individual host on the network. host security is the next layer of security in defense in depth that should be taken care of. this module focuses on security measures and techniques required for securing individual hosts. Implement policies, plan backup strategies, and test functionality. follow guidelines to secure a device: harden base system or install latest firmware. implement security recommendations and strict access controls. implement and configure all suggested router security settings. implement nat or nps.
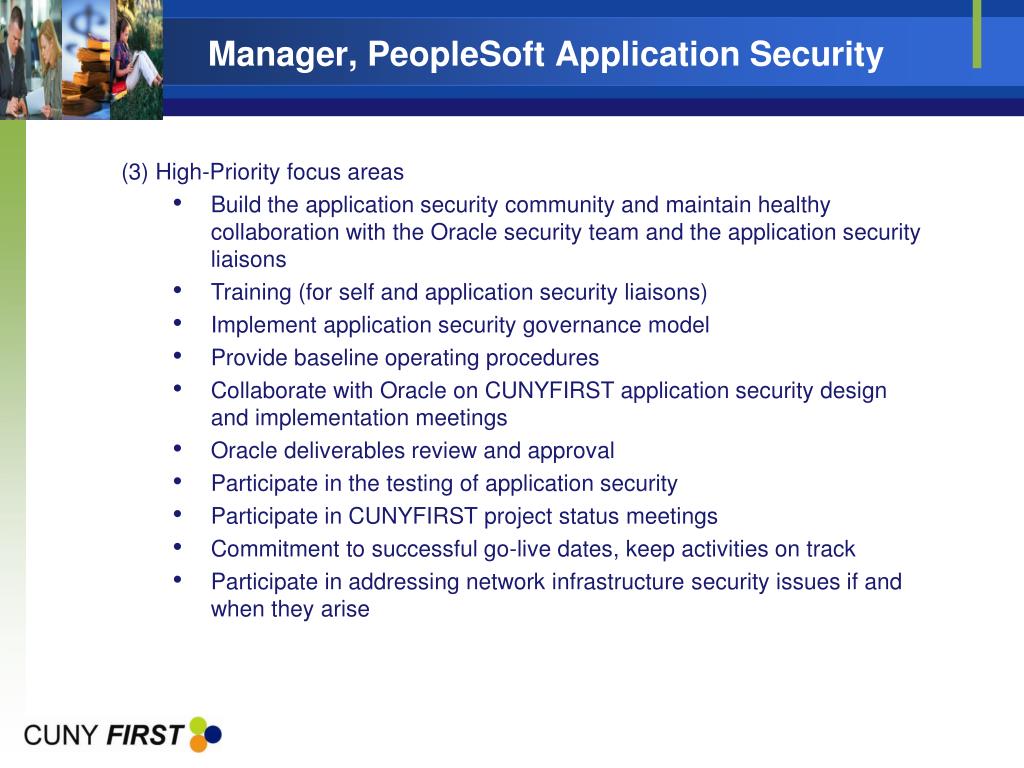
Ppt Application Security Management Powerpoint Presentation Free This document discusses managing data, application, and host security. it covers topics like application security methods, data security goals and techniques, managing device and host security, and mobile security controls. This guide offers an overview of the security development life cycle (secdl) and host of security features supported by nutanix. it also demonstrates how nutanix complies with security regulations to streamline infrastructure security management. Network security starts with securing the individual host on the network. host security is the next layer of security in defense in depth that should be taken care of. this module focuses on security measures and techniques required for securing individual hosts. Implement policies, plan backup strategies, and test functionality. follow guidelines to secure a device: harden base system or install latest firmware. implement security recommendations and strict access controls. implement and configure all suggested router security settings. implement nat or nps.

Application Security Architecture Securesky Strengthens Your Defenses Network security starts with securing the individual host on the network. host security is the next layer of security in defense in depth that should be taken care of. this module focuses on security measures and techniques required for securing individual hosts. Implement policies, plan backup strategies, and test functionality. follow guidelines to secure a device: harden base system or install latest firmware. implement security recommendations and strict access controls. implement and configure all suggested router security settings. implement nat or nps.

Application Security Services Ibm
Comments are closed.