Zig Sha3 Hashing
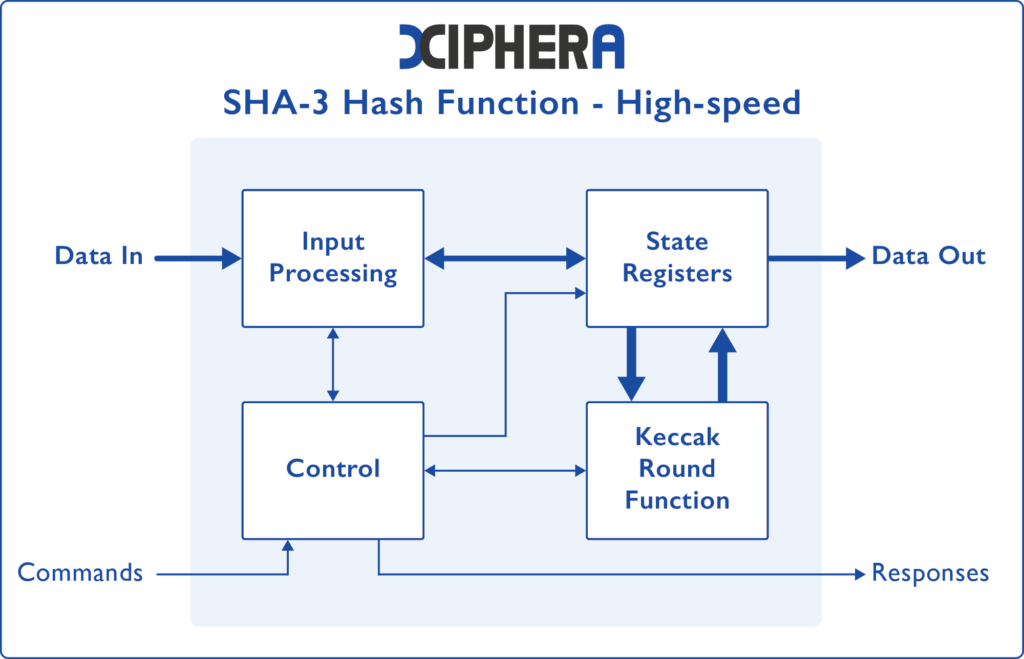
Sha 3 Xiphera Explore sha3 128 implementation in zig. learn techniques, examples, and best practices for secure hash functions in your zig programming projects. Sha 3 was known as keccak and is a hash function designed by guido bertoni, joan daemen, michaël peeters, and gilles van assche. md5 and sha 0 have been shown to be susceptible to attacks, along with theoretical attacks on sha 1.
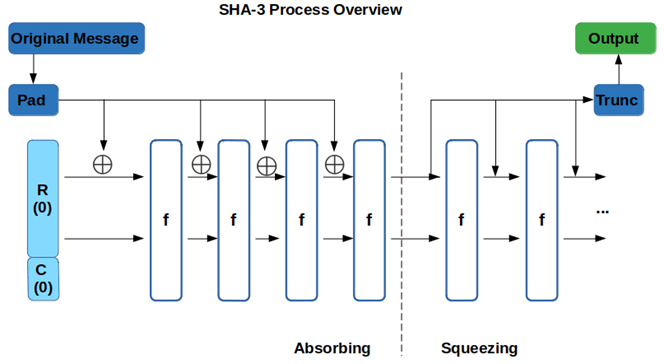
Hash Algorithm Comparison Md5 Sha 1 Sha 2 Sha 3 When you need to securely hash data in your zig applications, especially for integrity checks or password storage, understanding sha3 128 is crucial. this guide walks you through implementing sha3 128 directly within zig, without relying on external c libraries. Securing sensitive data often requires robust cryptographic hashing, but implementing these algorithms correctly can be complex. this guide dives into sha3 128 using zig, providing a clear, performant implementation for your projects. Zig is a relatively new programming language and which is simple to use. in this case, we will use the crypto library to integrate with the hashing methods of sha 1, sha 2 (sha 224, sha 256) , and sha 3 (sha3 224, sha3 256, sha3 384 and sha3 512). Learn how to implement sha3 224 in zig with our step by step guide, examples, and tips for secure hashing in your applications.
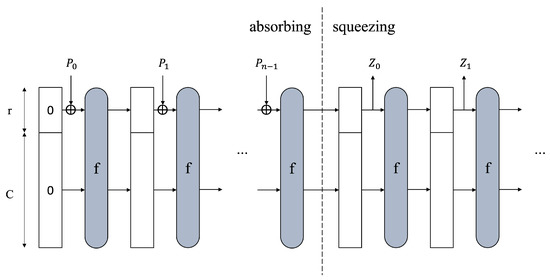
Improved Low Depth Sha3 Quantum Circuit For Fault Tolerant Quantum Zig is a relatively new programming language and which is simple to use. in this case, we will use the crypto library to integrate with the hashing methods of sha 1, sha 2 (sha 224, sha 256) , and sha 3 (sha3 224, sha3 256, sha3 384 and sha3 512). Learn how to implement sha3 224 in zig with our step by step guide, examples, and tips for secure hashing in your applications. Securing data with strong cryptographic hashing is crucial, but implementing algorithms like sha3 256 correctly in zig can be challenging. this guide breaks down how to leverage zig's standard library or external packages to integrate sha3 256 hashing into your applications. This guide walks you through implementing hmac sha3 128 using zig's standard library capabilities, demonstrating how to generate and verify message authentication codes efficiently. Learn how to implement hmac sha3 128 in zig with step by step guidance and examples for secure hashing and data integrity in your applications. This guide shows you how to implement hmac sha3 128 in zig, providing a robust way to verify that messages haven't been tampered with and originate from a trusted source.
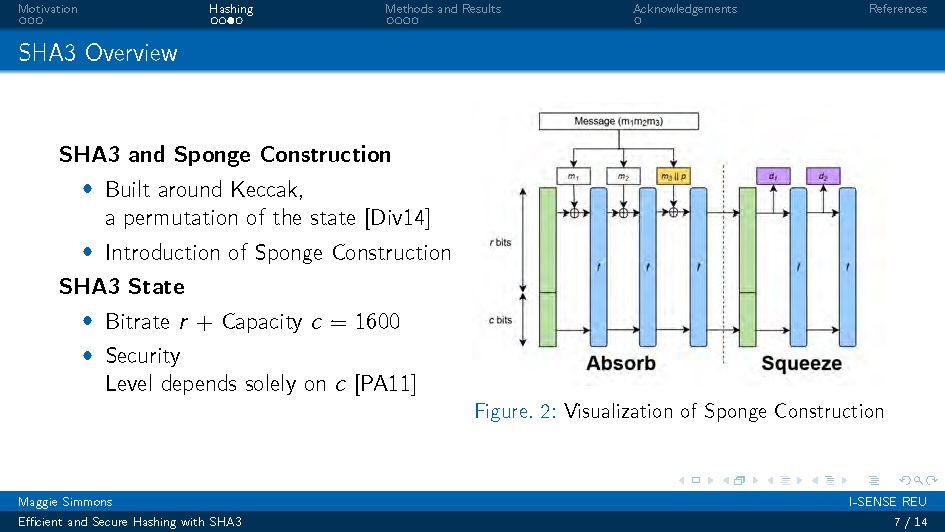
Efficient And Secure Hashing With Sha3 Florida Atlantic University Securing data with strong cryptographic hashing is crucial, but implementing algorithms like sha3 256 correctly in zig can be challenging. this guide breaks down how to leverage zig's standard library or external packages to integrate sha3 256 hashing into your applications. This guide walks you through implementing hmac sha3 128 using zig's standard library capabilities, demonstrating how to generate and verify message authentication codes efficiently. Learn how to implement hmac sha3 128 in zig with step by step guidance and examples for secure hashing and data integrity in your applications. This guide shows you how to implement hmac sha3 128 in zig, providing a robust way to verify that messages haven't been tampered with and originate from a trusted source.

Back To Basics Secure Hash Algorithms Analog Devices Learn how to implement hmac sha3 128 in zig with step by step guidance and examples for secure hashing and data integrity in your applications. This guide shows you how to implement hmac sha3 128 in zig, providing a robust way to verify that messages haven't been tampered with and originate from a trusted source.

Back To Basics Secure Hash Algorithms Analog Devices
Comments are closed.