Zerocompromise Cyberdoctrine Zerointernet Cybercommanders

U S Cyber Command On Twitter U S Cyber Command Is The World S It’s an operational doctrine that replaces zero trust, audits your assumptions, and enforces zero internet, zero exposure, and zero cross contamination. The ccdcoe cyber commanders’ handbook 2 is a practical guide designed to support commanders and decision makers in understanding, integrating, and employing cyber capabilities within multi domain operations.
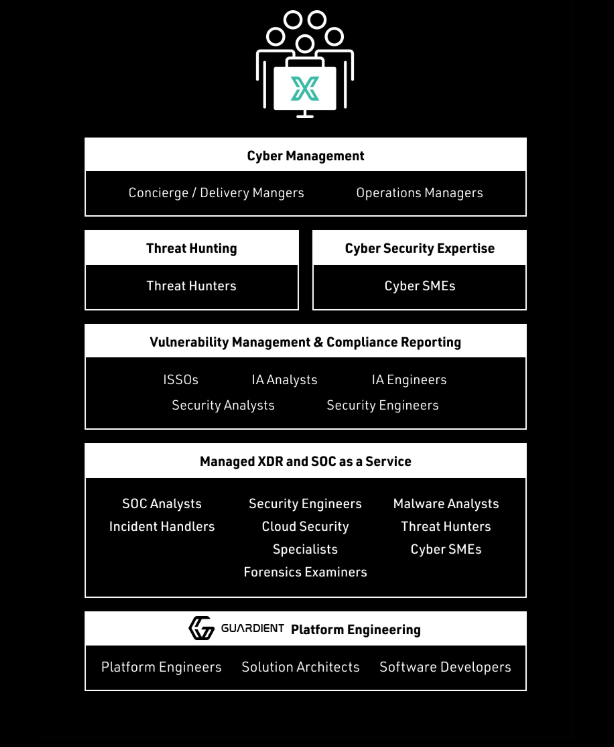
About Us Usx Cyber The ccdcoe cyber commanders’ handbook 2 is a practical guide designed to support commanders and decision makers in understanding, integrating, and employing cyber capabilities within multi domain operations. Each episode decodes real world breaches, insider threats, and systemic vulnerabilities through the lens of zero trust, zero exposure, and zero internet principles — enforced by protocols like dna™, stealth™, trustnet™, and titanai™. Establishes the zero trust (zt) portfolio management office (pfmo) and describes its responsibilities to coordinate, synchronize, and accelerate the dod enterprise’s adoption of zt architecture and cybersecurity framework, modernizing the dod’s ability to impede malicious threat actors in cyberspace. This handbook will help cyber commanders to command cyber operations efficiently and avoid stumbling blocks that may be found due to the specifics of cyber space.

Zero Trust Is Needed To Win The Cyber War Webinar Stream Fedinsider Establishes the zero trust (zt) portfolio management office (pfmo) and describes its responsibilities to coordinate, synchronize, and accelerate the dod enterprise’s adoption of zt architecture and cybersecurity framework, modernizing the dod’s ability to impede malicious threat actors in cyberspace. This handbook will help cyber commanders to command cyber operations efficiently and avoid stumbling blocks that may be found due to the specifics of cyber space. That’s why i wrote the zero doctrine™ — a sovereign grade cybersecurity philosophy rooted in: zero internet zero exposure zero compromise this isn’t a framework. In this episode of zero compromise™, manuel w. lloyd breaks down the nro’s aggressive satellite expansion and the massive cybersecurity implications of proliferated constellations. “zero trust is the term for an evolving set of cybersecurity paradigms that move defenses from static, network based perimeters to focus on users, assets, and resources. Zero trust is a collection of concepts and ideas that assume no trust exists within a defined enterprise network. the defense department recently released a series of "zero trust overlays" meant to help dod implement zero trust concepts across the department.
Comments are closed.