Zero Trust U S Army Cyber Command

Zero Trust U S Army Cyber Command What is zero trust (zt)? the department of defense (dod) and the national institute of standards and technology define zt as an “evolving set of cybersecurity paradigms that move defenses from. We all must play a role in combating our adversaries by acting quickly and correctly to address security threats wherever and whenever they arise. zero trust is much more than an it solution .

Operate Defend Attack U S Army Cyber Command In a decisive step toward fortifying its defenses against growing cyber threats, the u.s. army has launched an initiative to overhaul its cybersecurity framework, focusing on a. What is zero trust (zt)? the department of defense (dod) and the national institute of standards and technology define zt as an “evolving set of cybersecurity paradigms that move defenses. What is zero trust (zt)? the department of defense (dod) and the national institute of standards and technology define zt as an “evolving set of cybersecurity paradigms that move defenses. Zt is a modern approach to cybersecurity that operates on a simple but powerful principle: never trust, always verify. unlike traditional security models that assume everything inside a network.

Zero Trust Article The United States Army What is zero trust (zt)? the department of defense (dod) and the national institute of standards and technology define zt as an “evolving set of cybersecurity paradigms that move defenses. Zt is a modern approach to cybersecurity that operates on a simple but powerful principle: never trust, always verify. unlike traditional security models that assume everything inside a network. The zero trust model, with its emphasis on continuous verification, granular access control, and least privilege access, offers a more comprehensive approach to cybersecurity. This article examines the army's zero trust cybersecurity initiative to enhance data protection and modernize defenses. U.s. army cyber command integrates and conducts cyberspace operations, electromagnetic warfare, and information operations, ensuring decision dominance and freedom of action for friendly. As the nation's first line of defense in cyberspace, we operate at the speed, relevance, and scale necessary to win. learn about the code here.
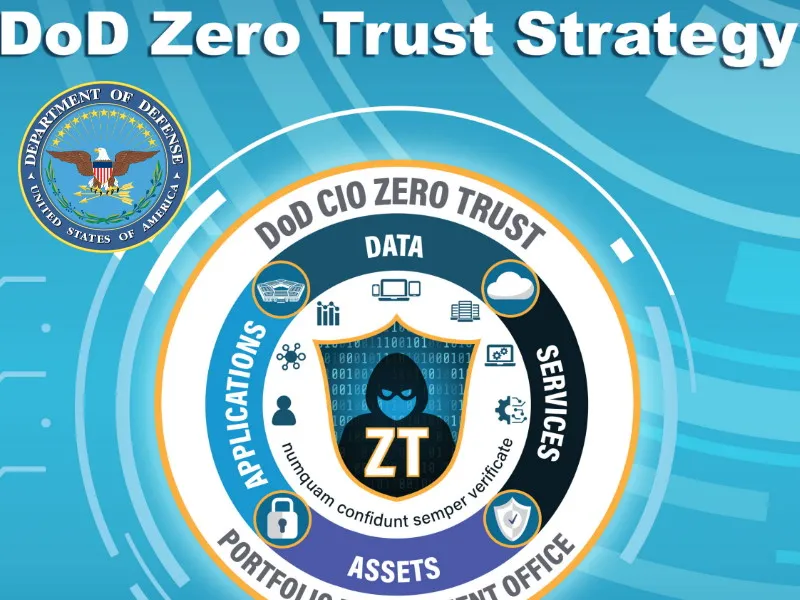
Dod Zero Trust Strategy Industrial Cyber The zero trust model, with its emphasis on continuous verification, granular access control, and least privilege access, offers a more comprehensive approach to cybersecurity. This article examines the army's zero trust cybersecurity initiative to enhance data protection and modernize defenses. U.s. army cyber command integrates and conducts cyberspace operations, electromagnetic warfare, and information operations, ensuring decision dominance and freedom of action for friendly. As the nation's first line of defense in cyberspace, we operate at the speed, relevance, and scale necessary to win. learn about the code here.

U S Army Cyber Command On Linkedin Army Cyber Command Arcyber U.s. army cyber command integrates and conducts cyberspace operations, electromagnetic warfare, and information operations, ensuring decision dominance and freedom of action for friendly. As the nation's first line of defense in cyberspace, we operate at the speed, relevance, and scale necessary to win. learn about the code here.

Zerotrust Cybersecurity Dod Stayprotected Army Chief Information
Comments are closed.