Zero Trust That Actually Ships Moving From Strategy Decks To Real Security Rohan Ravindranath
Zero Trust Strategy A Business Aligned Approach To Modern Security Most enterprise organizations have been working at zero trust for years but many fail to deliver truly secure environments. rohan ravindranath shares valuable insights that zappsec has gained from guiding the global teams that are getting it right. Most enterprise organizations have been working at zero trust for years but many fail to deliver truly secure environments.
Zero Trust Insights Watch his insightful guidance on how to make sure your organization actually reaps the benefits of zero trust, versus just going through the motions of implementing it. Most enterprise organizations have been working at zero trust for years but many fail to deliver truly secure environments. rohan ravindranath shares valuable insights that zappsec has gained from guiding the global teams that are getting it right. Delivered hybrid cloud modernization and zero trust deployment to combat ransomware and ensure consistent security policies. we are experts in cloud solutions, specializing in multi cloud environments like aws, azure, and gcp. To help you better understand the components, complexities, and challenges that come with such an undertaking, security chiefs share their experiences on the road to zero trust.

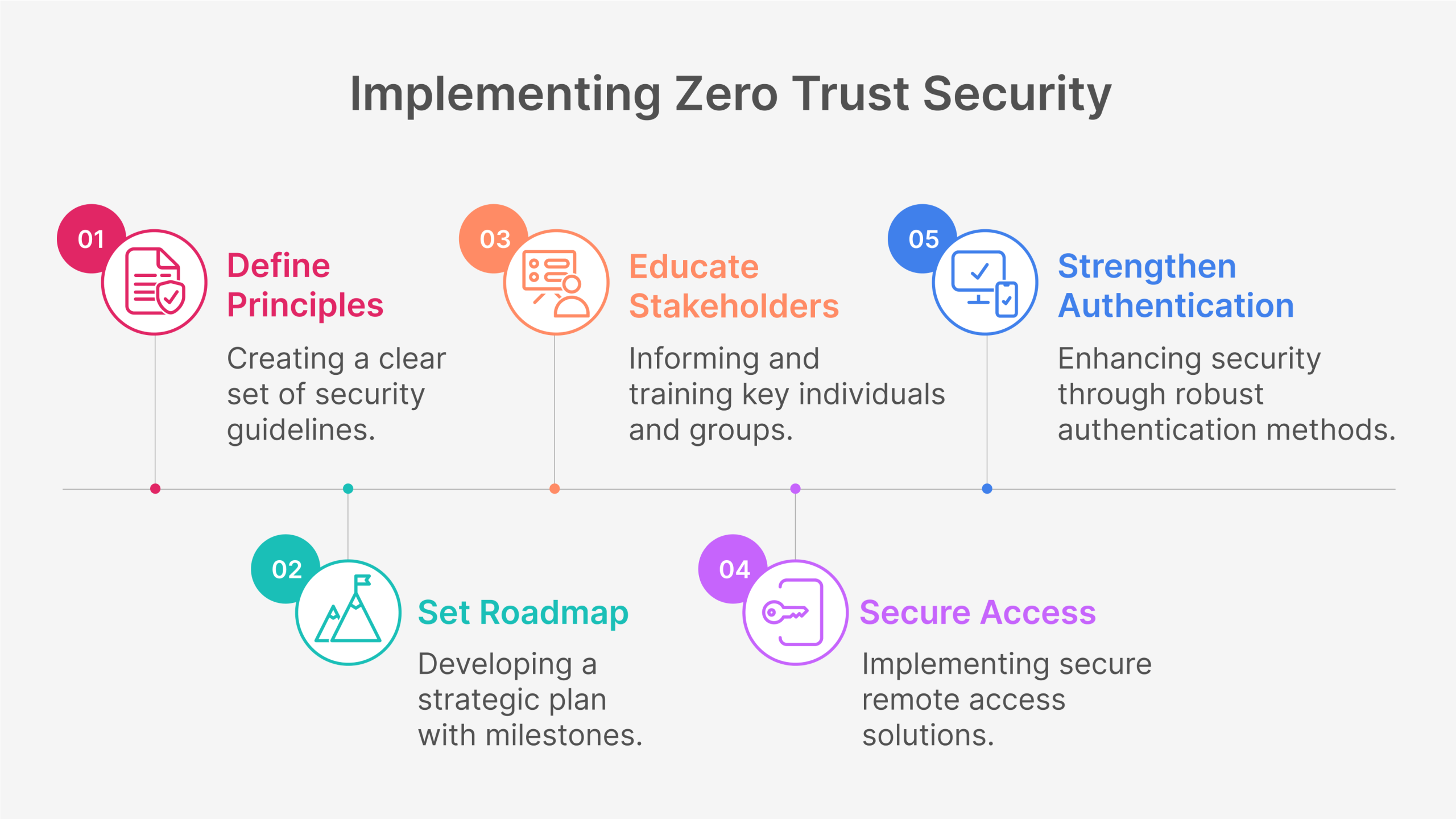
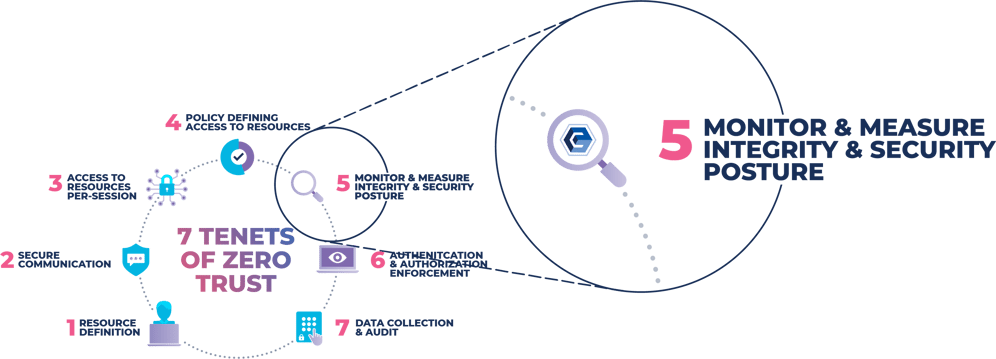
Rh Isac Zero Trust Architecture Zta How To Get Started Rh Isac Delivered hybrid cloud modernization and zero trust deployment to combat ransomware and ensure consistent security policies. we are experts in cloud solutions, specializing in multi cloud environments like aws, azure, and gcp. To help you better understand the components, complexities, and challenges that come with such an undertaking, security chiefs share their experiences on the road to zero trust. Discover how to turn zero trust from a buzzword into a practical, business driven security architecture. learn key steps, challenges, and how to align with real world risks. In this post, we'll outline a framework for a true zero trust model that adheres to industry best practices while specifically avoiding the potential for an over engineered network overhaul, wasted it budget, and potentially costly organizational disruption. After 26 years building and breaking enterprise security, here is the zero trust implementation roadmap that actually works. covers identity first architecture, the 7 pillars, and an 18 month execution plan. Zero trust architecture (zta) is rapidly becoming one of the most prominent buzzwords in cybersecurity. as businesses accelerate cloud adoption, enable remote work, and face increasingly sophisticated cyberattacks, traditional perimeter based defences are no longer enough.

Your Zero Trust Strategy Shouldn T Have An Asterisk Behind It Syncdog Discover how to turn zero trust from a buzzword into a practical, business driven security architecture. learn key steps, challenges, and how to align with real world risks. In this post, we'll outline a framework for a true zero trust model that adheres to industry best practices while specifically avoiding the potential for an over engineered network overhaul, wasted it budget, and potentially costly organizational disruption. After 26 years building and breaking enterprise security, here is the zero trust implementation roadmap that actually works. covers identity first architecture, the 7 pillars, and an 18 month execution plan. Zero trust architecture (zta) is rapidly becoming one of the most prominent buzzwords in cybersecurity. as businesses accelerate cloud adoption, enable remote work, and face increasingly sophisticated cyberattacks, traditional perimeter based defences are no longer enough.
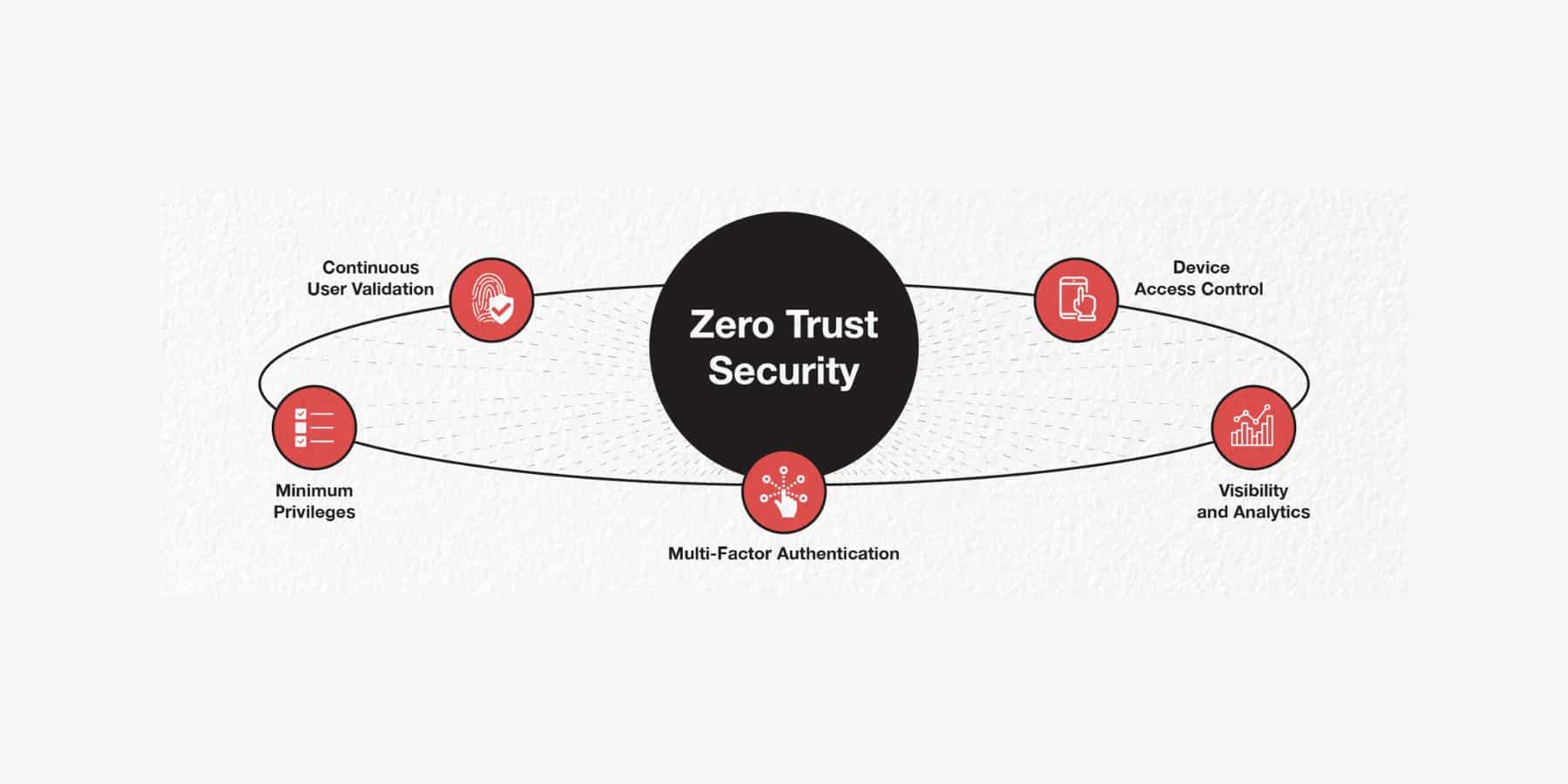
Zero Trust After 26 years building and breaking enterprise security, here is the zero trust implementation roadmap that actually works. covers identity first architecture, the 7 pillars, and an 18 month execution plan. Zero trust architecture (zta) is rapidly becoming one of the most prominent buzzwords in cybersecurity. as businesses accelerate cloud adoption, enable remote work, and face increasingly sophisticated cyberattacks, traditional perimeter based defences are no longer enough.
Comments are closed.