Zero Trust Security Visually Explained

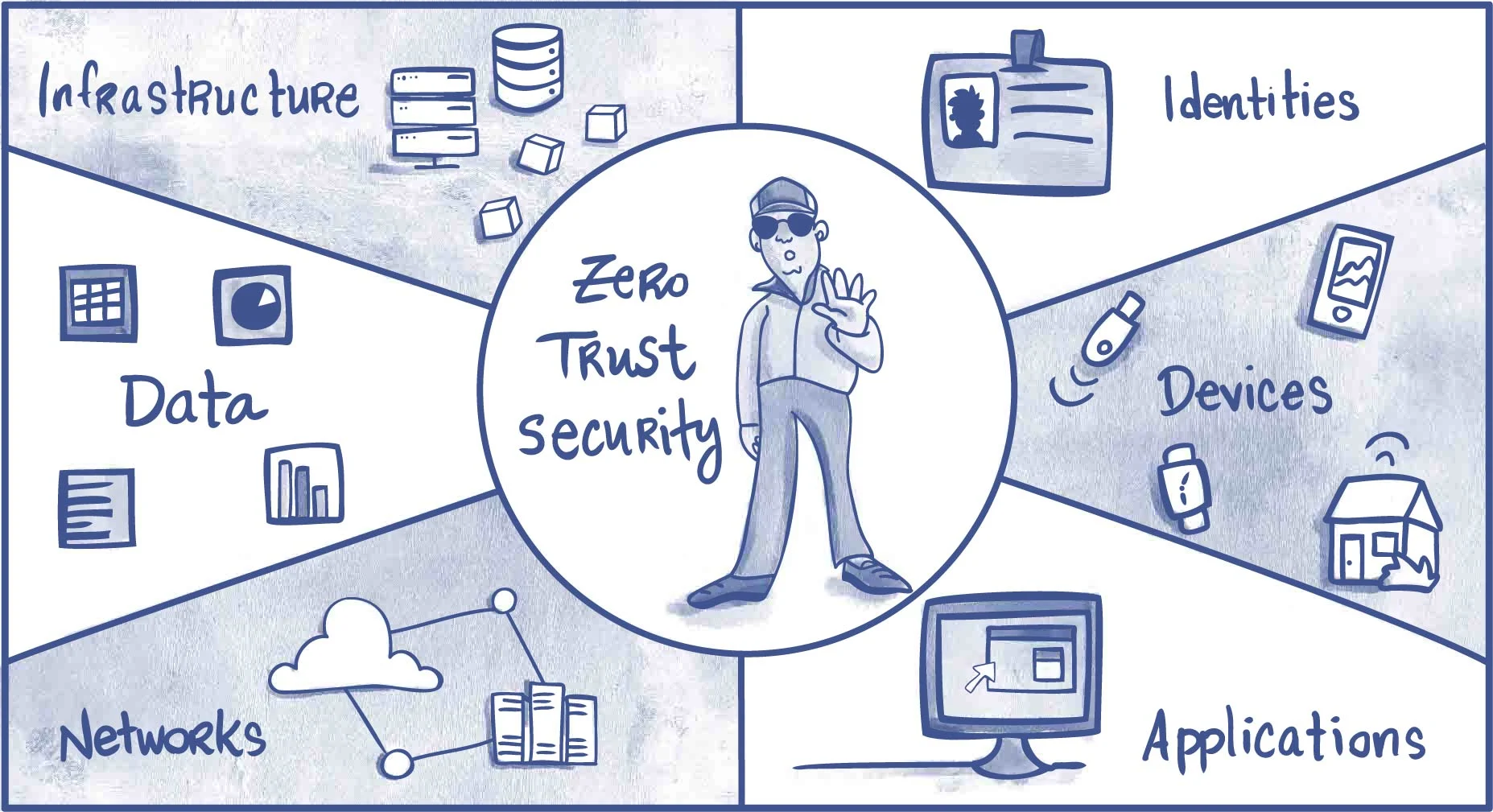
Zero Trust Security Explained Versetal Unlike traditional security models that rely on a defined network perimeter, zero trust operates on the principle that no user or system should be automatically trusted. instead, continuous authentication, authorization, and validation of security configurations are required before access is granted to applications and data. Zero trust is transforming the security posture of today’s enterprises and mobile networks. explore the basic principles, benefits and latest use cases.
Zero Trust Security Model Explained Principles Architectu Blog Find deployment guides, assessment tools, and adoption frameworks to implement zero trust principles that protect and enable secure operations across identity, endpoints, applications, data, infrastructure, and networks in your organization. Learn what zero trust security architecture is, why it matters now, and how to implement it with practical steps, diagrams, and real world guidance. Learn what zero trust is, how the security model works, its core pillars, the nist framework, and how to implement a zero trust architecture step by step. What is zero trust? the basics explained as government services move online and across systems, zero trust becomes essential to ensuring every interaction is secure and verifiable.
Zero Trust Security Model Explained Gaming Songs Python Programming Learn what zero trust is, how the security model works, its core pillars, the nist framework, and how to implement a zero trust architecture step by step. What is zero trust? the basics explained as government services move online and across systems, zero trust becomes essential to ensuring every interaction is secure and verifiable. A structured explanation of zero trust security: principles, identity first access, continuous verification, and why 'never trust, always verify' is often misunderstood. Complete guide to zero trust security architecture. learn the principles of "never trust, always verify," how to implement zero trust, and real world architecture patterns for enterprises. Explore the microsoft zero trust workshop guide to secure identities, devices, apps, data, infrastructure, networks, and ai with zero trust principles. The core principles of zero trust can be seen through the lens of the eight zero trust principles developed by the uk government’s national cyber security centre (ncsc).
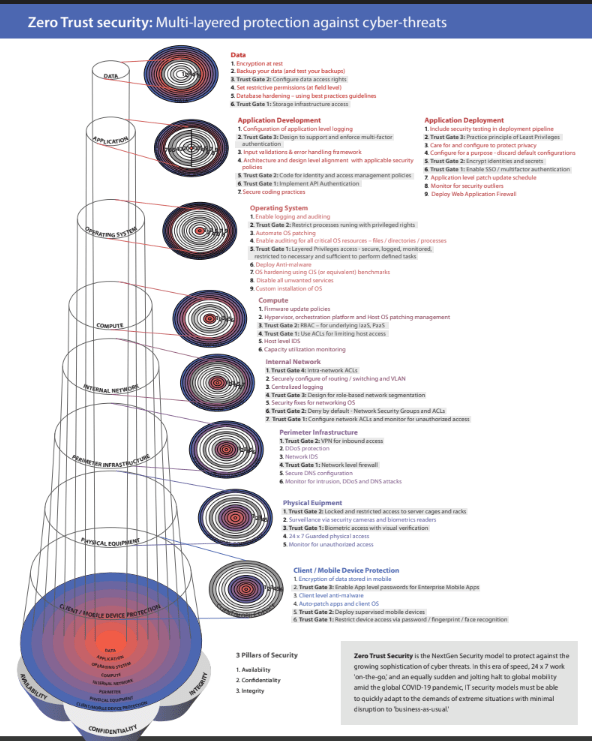
Zero Trust Security Mos A structured explanation of zero trust security: principles, identity first access, continuous verification, and why 'never trust, always verify' is often misunderstood. Complete guide to zero trust security architecture. learn the principles of "never trust, always verify," how to implement zero trust, and real world architecture patterns for enterprises. Explore the microsoft zero trust workshop guide to secure identities, devices, apps, data, infrastructure, networks, and ai with zero trust principles. The core principles of zero trust can be seen through the lens of the eight zero trust principles developed by the uk government’s national cyber security centre (ncsc).

Zero Trust Security Model Explore the microsoft zero trust workshop guide to secure identities, devices, apps, data, infrastructure, networks, and ai with zero trust principles. The core principles of zero trust can be seen through the lens of the eight zero trust principles developed by the uk government’s national cyber security centre (ncsc).
Zero Trust Explained How To Implement Zero Trust Architecture Reduce
Comments are closed.