Zero Trust Security Part 2
Zero Trust Security Mos Zero trust provides a collection of concepts and ideas designed to minimize uncertainty in enforcing accurate, least privilege per request access decisions in information systems and services in the face of a network viewed as compromised. Learn practical application of zero trust security principles like least privilege, continuous verification and segmentation and how they can protect resources in government and commercial organizations.

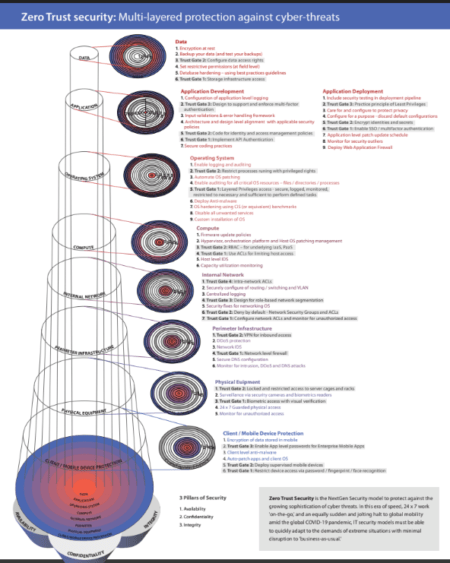
What Is Zero Trust Security Zero Trust Security For Businesses Techwey Zero trust (zt) is the term for an evolving set of cybersecurity paradigms that move defenses from static, network based perimeters to focus on users, assets, and resources. a zero trust architecture (zta) uses zero trust principles to plan industrial and enterprise infrastructure and workflows. zero trust assumes there is no implicit trust granted to assets or user accounts based solely on. Zero trust means "never trust, always verify" you don't trust anyone or anything by default, even if they're inside your network. traditional security works like a castle with walls. once you're inside, you can access everything. Protect against modern threats with a zero trust security strategy powered by ai. discover zero trust security and strategy today with microsoft security. In this article, we’ll explore in detail what zero trust is, its historical context, the key principles that guide it, and how it can be implemented to improve the security of networks and information systems.

Implementing Zero Trust Security A Guide For Modern Businesses Protect against modern threats with a zero trust security strategy powered by ai. discover zero trust security and strategy today with microsoft security. In this article, we’ll explore in detail what zero trust is, its historical context, the key principles that guide it, and how it can be implemented to improve the security of networks and information systems. Zero trust is a security model based on maintaining strict access controls and not trusting anyone by default. learn more about zero trust. Learn how zero trust security reduces attack surface, enforces continuous verification, and integrates iam with attack surface intelligence. The five pillars of zero trust, based on the cybersecurity and infrastructure security agency’s recently published zero trust maturity model version 2, are identity, devices, networks, applications and workloads, and data. Zero trust architecture addresses security for all physical and virtual infrastructure, including routers, switches, servers, cloud services, and iot devices. it ensures that every component is continuously verified and protected, regardless of whether it resides on premises or in the cloud.

Zero Trust Cyber Security Zero Trust Security Solutions Pptx Zero trust is a security model based on maintaining strict access controls and not trusting anyone by default. learn more about zero trust. Learn how zero trust security reduces attack surface, enforces continuous verification, and integrates iam with attack surface intelligence. The five pillars of zero trust, based on the cybersecurity and infrastructure security agency’s recently published zero trust maturity model version 2, are identity, devices, networks, applications and workloads, and data. Zero trust architecture addresses security for all physical and virtual infrastructure, including routers, switches, servers, cloud services, and iot devices. it ensures that every component is continuously verified and protected, regardless of whether it resides on premises or in the cloud.

Zero Trust Security In 2025 Why Trust No One Is Now A Business The five pillars of zero trust, based on the cybersecurity and infrastructure security agency’s recently published zero trust maturity model version 2, are identity, devices, networks, applications and workloads, and data. Zero trust architecture addresses security for all physical and virtual infrastructure, including routers, switches, servers, cloud services, and iot devices. it ensures that every component is continuously verified and protected, regardless of whether it resides on premises or in the cloud.

Zero Trust Qmulos
Comments are closed.