Zero Trust Security Model Pdf

Zero Trust Security Model Pdf This article talks about how to set up zero trust architectures and how well they work by looking at the ideas behind limiting access and constantly checking trust for both internal and. Cisa’s zero trust maturity model (ztmm) provides an approach to achieve continued modernization efforts related to zero trust within a rapidly evolving environment and technology landscape.

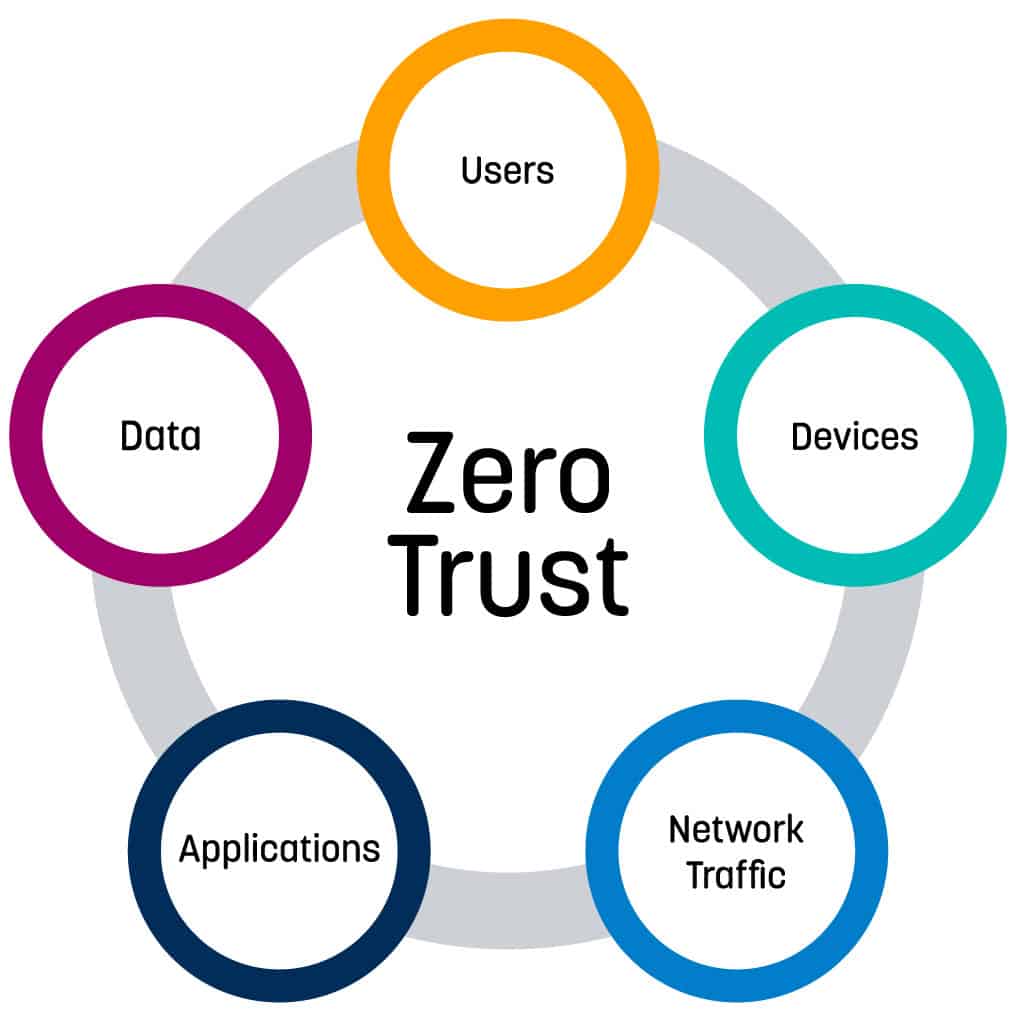
Embracing A Zero Trust Security Model Pdf Computer Security Security This document provides information on zero trust (zt) as a model to address the modern challenges of securing remote workers, protecting hybrid cloud environments, and defending against cyber security threats. This research paper offers a comprehensive overview of zero trust security models, exploring their historical context, fundamental principles, implementation strategies, and real world applications. Both microsoft 365 and azure are designed with zero trust as a core architectural principle. protections span beyond the microsoft cloud, to hybrid or even multi cloud environments. We look at zero trust as a comprehensive and transformative model that replaces implicit trust with explicit and continuous monitoring and verification based on the risk factors and the threat landscape, regardless of user location or used device.

Zero Trust Security Models Overview Pdf Both microsoft 365 and azure are designed with zero trust as a core architectural principle. protections span beyond the microsoft cloud, to hybrid or even multi cloud environments. We look at zero trust as a comprehensive and transformative model that replaces implicit trust with explicit and continuous monitoring and verification based on the risk factors and the threat landscape, regardless of user location or used device. Within this piece, we look at how to use zero trust security models and how well they work in real life situations. the goal is to show the pros and cons of implementing zero trust and how it affects safety by looking at case studies and real world tests. The following cybersecurity guidance explains the zero trust security model and its benefits, as well as challenges for implementation. it discusses the importance of building a detailed. This research paper offers a comprehensive overview of zero trust security models, exploring their historical context, fundamental principles, implementation strategies, and real world applications. In response to these challenges, the cybersecurity and infrastructure security agency (cisa) has developed a zero trust maturity model to guide organizations in adopting and implementing zero trust principles effectively.

Zero Trust Architecture Pdf Computer Security Security Within this piece, we look at how to use zero trust security models and how well they work in real life situations. the goal is to show the pros and cons of implementing zero trust and how it affects safety by looking at case studies and real world tests. The following cybersecurity guidance explains the zero trust security model and its benefits, as well as challenges for implementation. it discusses the importance of building a detailed. This research paper offers a comprehensive overview of zero trust security models, exploring their historical context, fundamental principles, implementation strategies, and real world applications. In response to these challenges, the cybersecurity and infrastructure security agency (cisa) has developed a zero trust maturity model to guide organizations in adopting and implementing zero trust principles effectively.

Zero Trust Security Model Ciso2ciso Com Cyber Security Group This research paper offers a comprehensive overview of zero trust security models, exploring their historical context, fundamental principles, implementation strategies, and real world applications. In response to these challenges, the cybersecurity and infrastructure security agency (cisa) has developed a zero trust maturity model to guide organizations in adopting and implementing zero trust principles effectively.
Embracing A Zero Trust Security Model Logrhythm
Comments are closed.