Zero Trust Security Is A Cybersecurity Framework For Security Measures
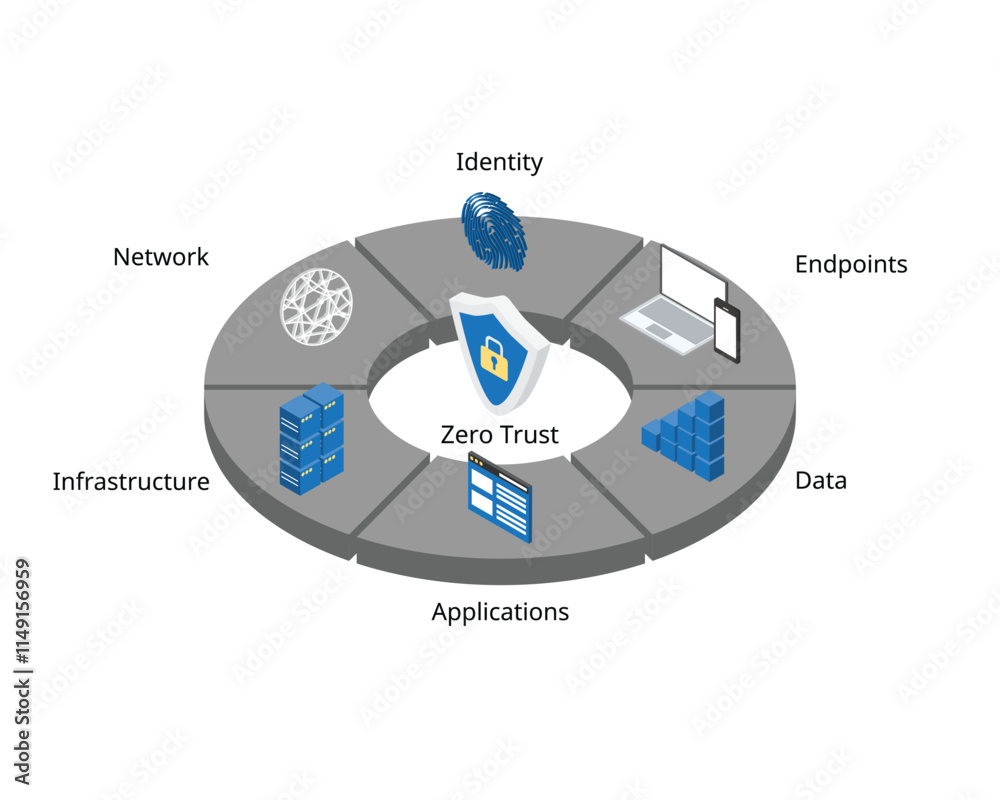
Zero Trust Security Is A Cybersecurity Framework For Security Measures Zero trust is a cybersecurity strategy that shifts from a location centric to a more data centric approach for better security controls between users, systems, data and assets that may change over time (cisa, 2021). Zero trust security is an it security model that requires strict identity verification for every person and device trying to access resources on a private network, regardless of whether they are sitting within or outside of the network perimeter.
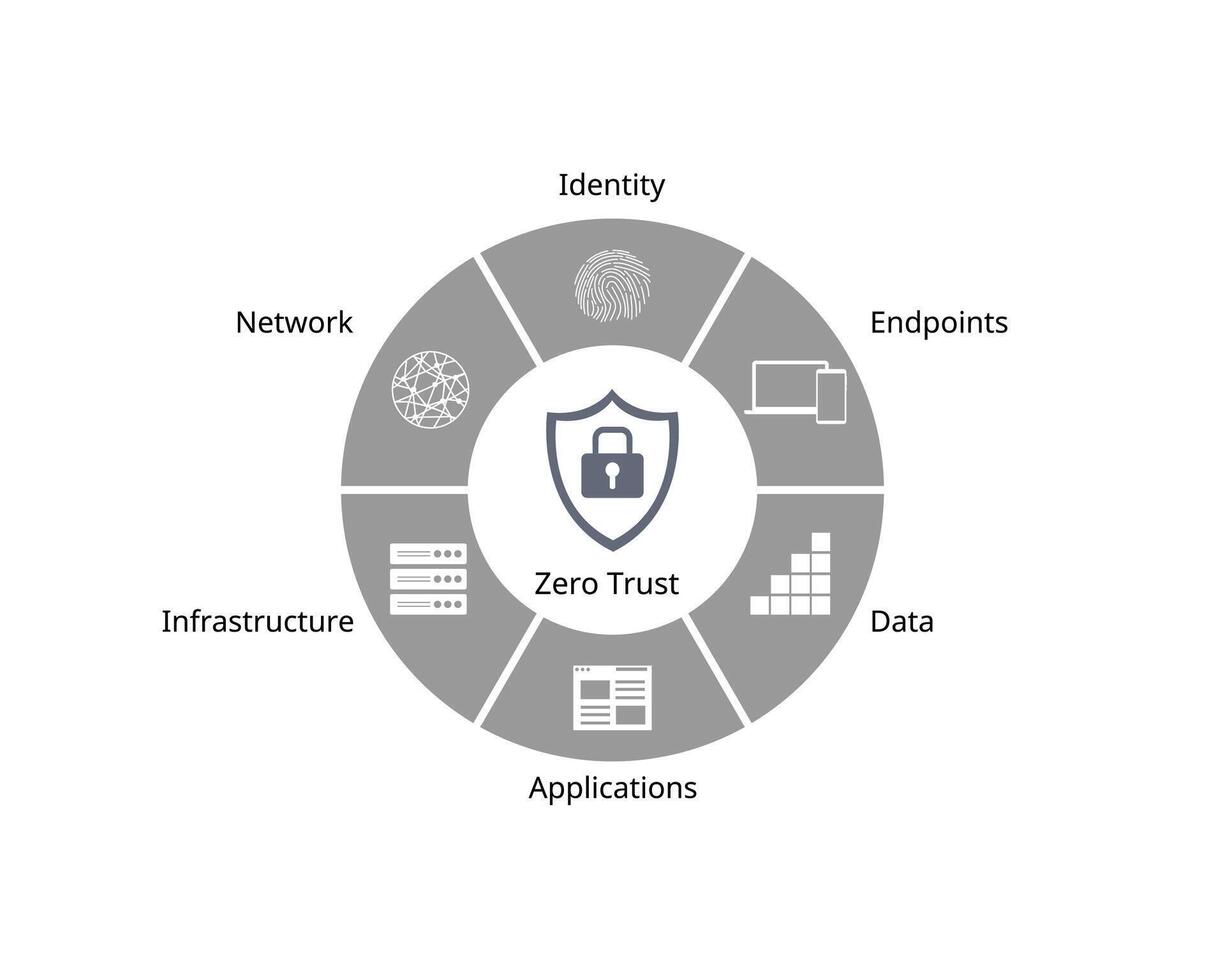
Zero Trust Security Is A Cybersecurity Framework For Security Measures Zero trust is a security framework that mandates stringent identity verification for every user and device attempting to access resources, regardless of whether they are inside or outside the organization’s network. This guidance contains an abstract definition of zero trust architecture (zta) and gives general deployment models and use cases where zero trust could improve an enterprise’s overall information technology security posture. Zero trust architecture (zta) is a security framework that authenticates every access request and proactively anticipates cyberattacks. businesses adopt this framework to ensure only authorized users and devices can enter their networks, access business resources, and view sensitive data. What is zero trust? zero trust is a security strategy for modern multicloud networks. instead of focusing on the network perimeter, a zero trust security model enforces security policies for each individual connection between users, devices, applications and data.
Zero Trust Security Framework Myths Busted What Vendors Won T Tell You Zero trust architecture (zta) is a security framework that authenticates every access request and proactively anticipates cyberattacks. businesses adopt this framework to ensure only authorized users and devices can enter their networks, access business resources, and view sensitive data. What is zero trust? zero trust is a security strategy for modern multicloud networks. instead of focusing on the network perimeter, a zero trust security model enforces security policies for each individual connection between users, devices, applications and data. Zero trust is a robust security model that works on the principle of “never trust, always verify” to ensure secure connections. understanding what is zero trust and implementing it can help organizations safeguard their crucial applications, devices, data, and resources. By enforcing least privileged access and evaluating context like identity, behavior, and device posture, zero trust secures users, workloads, iot ot devices, and b2b partners as they connect to applications and data—whether on premises, in the cloud, or at the edge. Zero trust (zt) is the term for an evolving set of cybersecurity paradigms that move defenses from static, network based perimeters to focus on users, assets, and resources. a zero trust architecture (zta) uses zero trust principles to plan industrial and enterprise infrastructure and workflows. Zero trust security, also known as a zero trust architecture or perimeterless security, assumes no one and no device or application is universally trusted, whether inside or outside the network.
Comments are closed.