Zero Trust Security Essentials

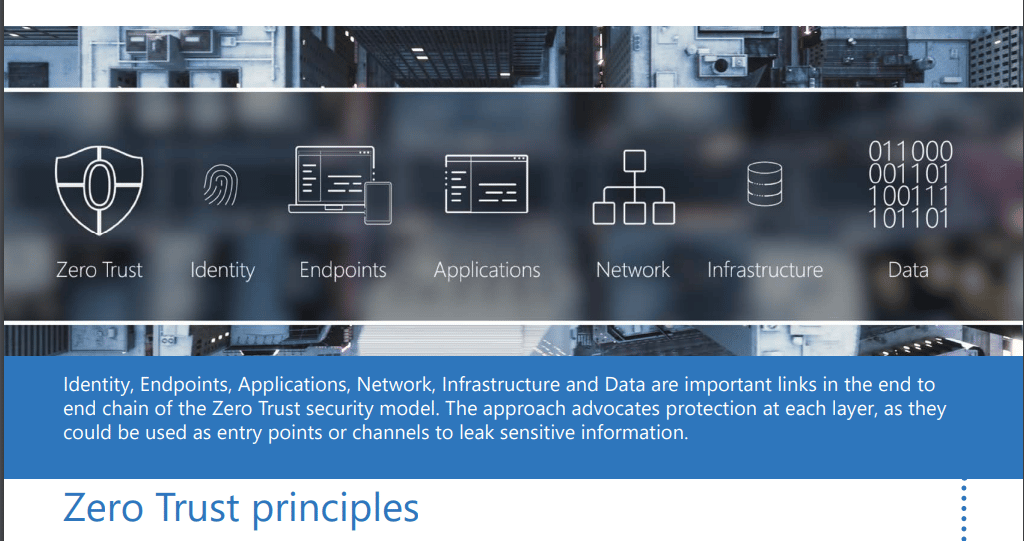
Zero Trust Security Essentials For hands on demonstrations of the tools for implementing the zero trust security model across the six layers of defense, watch our microsoft mechanics series at aka.ms zerotrustmechanics. This guide provides a comprehensive overview of zero trust principles, architectural models, practical implementation steps, and the tools needed to build a more secure and resilient organization.
Disc Infosec Blogzero Trust Essentials Ebook Disc Infosec Blog Zero trust is a security model based on maintaining strict access controls and not trusting anyone by default. learn more about zero trust. Get a comprehensive guide to key zero trust concepts, the most influential frameworks, top zero trust benefits, and best practices for selecting a zero trust vendor. Get started with essential toolset and take control of your cybersecurity landscape—efficiently and intelligently. complete and efficient cybersecurity tools for visibility and control. unified platform for all your security operations. Strengthen your security with zero trust. learn its core principles, essential technologies, and strategic implementation for robust data protection and compliance.

Zero Trust Security Key Importance Benefits In Cybersecurity Get started with essential toolset and take control of your cybersecurity landscape—efficiently and intelligently. complete and efficient cybersecurity tools for visibility and control. unified platform for all your security operations. Strengthen your security with zero trust. learn its core principles, essential technologies, and strategic implementation for robust data protection and compliance. Learn how zero trust security reduces attack surface, enforces continuous verification, and integrates iam with attack surface intelligence. Learn what zero trust security is, how the zero trust model works, and how to implement zero trust architecture to protect systems, users, and data. What are the zero trust principles? continually verify identity at every access decision; provide least privilege access for users, devices, networks, and apps; and respond quickly to threats before they spread. If you’re looking to advance your cybersecurity maturity, we can provide security solutions with zero trust capabilities to enhance your ability to harden, detect, defend and recover from malicious cyber activity.

Zero Trust Security Sify Learn how zero trust security reduces attack surface, enforces continuous verification, and integrates iam with attack surface intelligence. Learn what zero trust security is, how the zero trust model works, and how to implement zero trust architecture to protect systems, users, and data. What are the zero trust principles? continually verify identity at every access decision; provide least privilege access for users, devices, networks, and apps; and respond quickly to threats before they spread. If you’re looking to advance your cybersecurity maturity, we can provide security solutions with zero trust capabilities to enhance your ability to harden, detect, defend and recover from malicious cyber activity.

Zero Trust Essentials What are the zero trust principles? continually verify identity at every access decision; provide least privilege access for users, devices, networks, and apps; and respond quickly to threats before they spread. If you’re looking to advance your cybersecurity maturity, we can provide security solutions with zero trust capabilities to enhance your ability to harden, detect, defend and recover from malicious cyber activity.

Zero Trust Security Why It Is Important Cribb Cyber Security
Comments are closed.