Zero Trust Security Essential Cybersecurity Model

What Is Zero Trust Introduction Benefits Core Principles This guide provides a comprehensive overview of zero trust principles, architectural models, practical implementation steps, and the tools needed to build a more secure and resilient organization. In this article, we will discuss all you need to know about the zero trust security model. we will discuss the history, values and principles, technology and strategy, and why zero trust is so important right now.
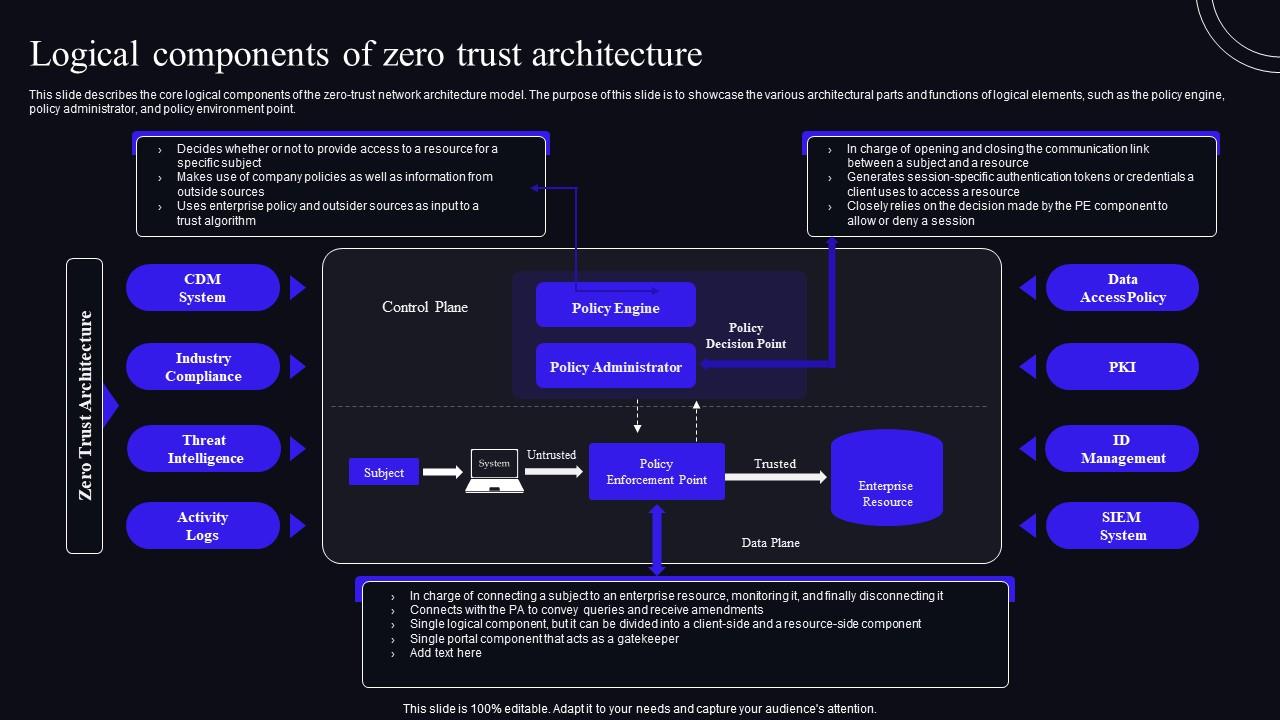
Logical Components Of Zero Trust Architecture Zero Trust Security Model A: zero trust is essential if your organization needs to address cyber threats like ransomware, supply chain attacks, and insider threats, especially if they must protect an infrastructure deployment that includes complex environments, unmanaged devices, legacy systems, and saas application. We look at zero trust as a comprehensive and transformative model that replaces implicit trust with explicit and continuous monitoring and verification based on the risk factors and the threat landscape, regardless of user location or used device. Zero trust is a security model, a set of system design principles, and a coordinated cybersecurity and system management strategy based on an acknowledgement that threats exist both. Zero trust means never trust by default always verify user, device, and access. it limits lateral movement and minimizes the attack surface. core principles include least privilege, continuous monitoring, and microsegmentation. ideal for securing remote work, cloud apps, and third party access.

What Is Zero Trust Architecture Zero Trust Security Model Zero trust is a security model, a set of system design principles, and a coordinated cybersecurity and system management strategy based on an acknowledgement that threats exist both. Zero trust means never trust by default always verify user, device, and access. it limits lateral movement and minimizes the attack surface. core principles include least privilege, continuous monitoring, and microsegmentation. ideal for securing remote work, cloud apps, and third party access. Organizations must shift to a more robust and dynamic cybersecurity framework: the zero trust approach (zta). rooted in the principle of “never trust, always verify,” zta ensures that access is granted based on strict authentication and continuous monitoring rather than assumed trust. What zero trust means for cybersecurity zt principles assume the entire network is compromised. that point of view provides a collection of concepts and ideas designed to minimize uncertainty by enforcing precise, least privilege per request access decisions within information systems and services. Zero trust is a robust security model that works on the principle of “never trust, always verify” to ensure secure connections. understanding what is zero trust and implementing it can help organizations safeguard their crucial applications, devices, data, and resources. Zero trust architecture (zta) emerges as a pivotal paradigm shift, fundamentally redefining organizational cybersecurity by eliminating implicit trust and enforcing continuous verification of.
Comments are closed.