Zero Trust Security Architecture
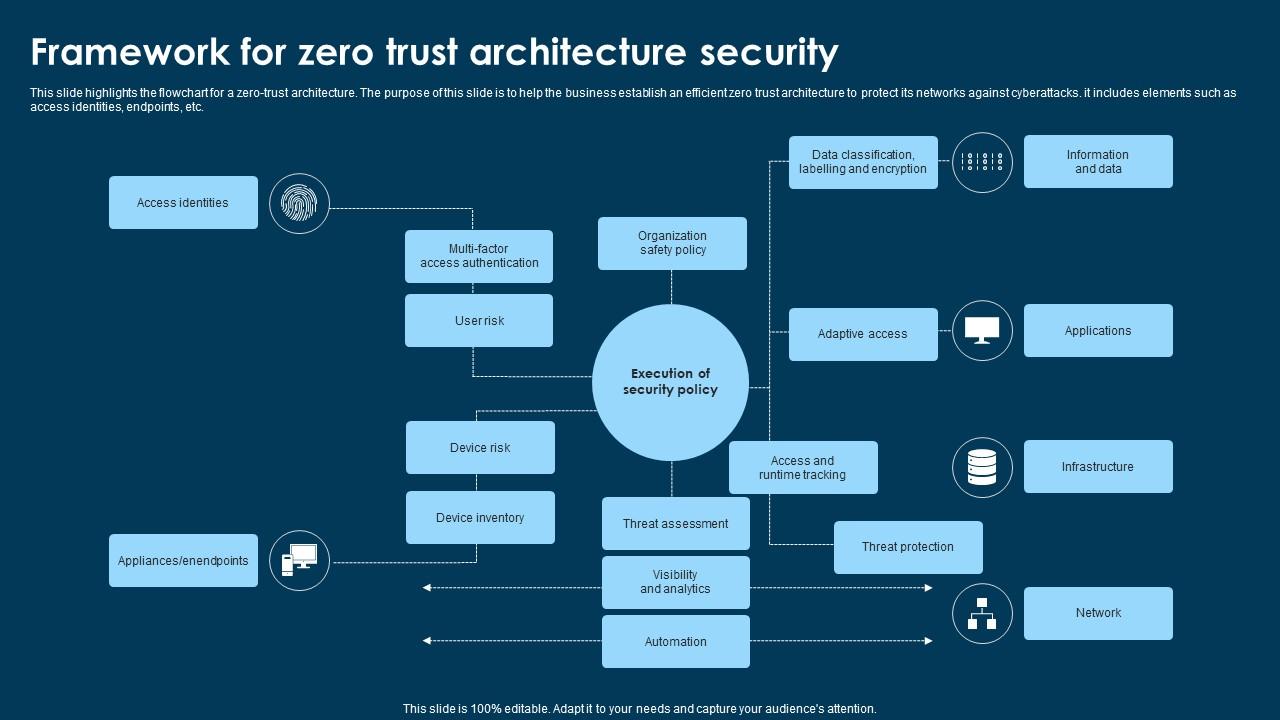
Framework For Zero Trust Architecture Security Ppt Example Zero trust architecture (zta) is a security framework that authenticates every access request and proactively anticipates cyberattacks. businesses adopt this framework to ensure only authorized users and devices can enter their networks, access business resources, and view sensitive data. This guidance contains an abstract definition of zero trust architecture (zta) and gives general deployment models and use cases where zero trust could improve an enterprise’s overall information technology security posture.
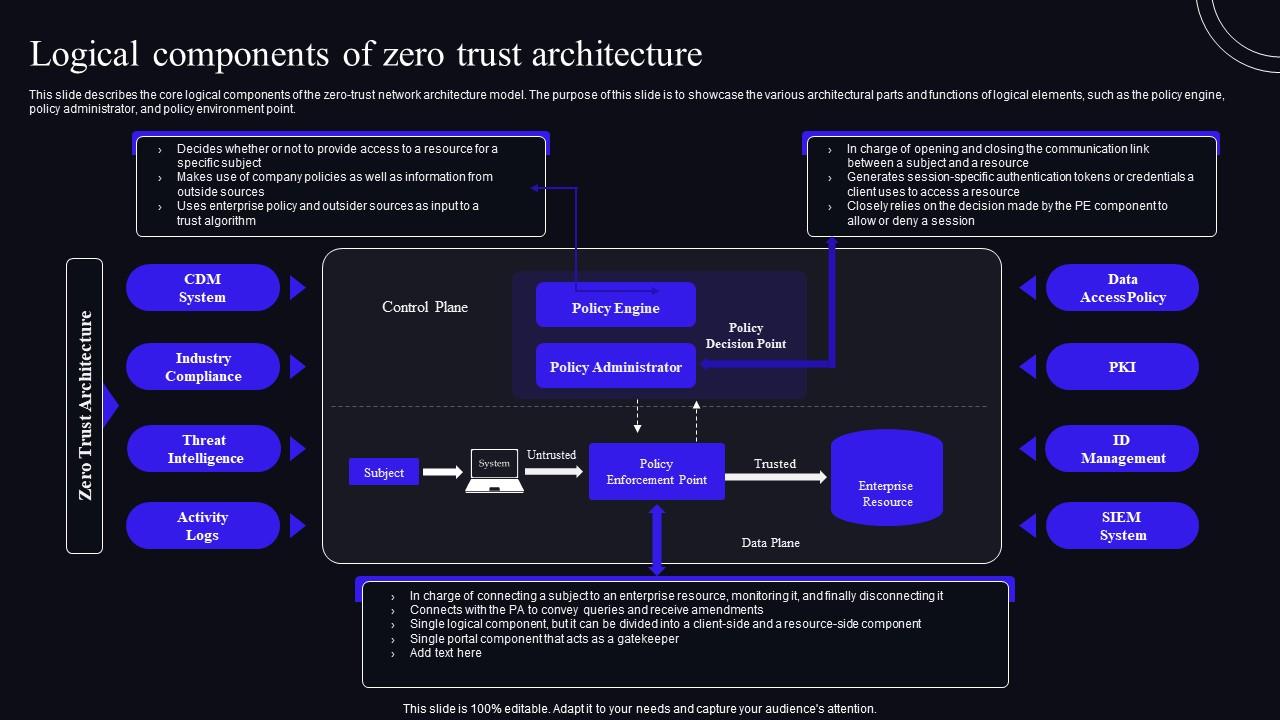
Logical Components Of Zero Trust Architecture Zero Trust Security Model Get a comprehensive guide to key zero trust concepts, the most influential frameworks, top zero trust benefits, and best practices for selecting a zero trust vendor. A zero trust architecture (zta) is an enterprise's cyber security plan that utilizes zero trust concepts and encompasses component relationships, workflow planning, and access policies. Zero trust architecture addresses security for all physical and virtual infrastructure, including routers, switches, servers, cloud services, and iot devices. it ensures that every component is continuously verified and protected, regardless of whether it resides on premises or in the cloud. Zero trust security, also known as a zero trust architecture or perimeterless security, assumes no one and no device or application is universally trusted, whether inside or outside the network.

Logical Components Of Zero Trust Architecture Zero Trust Network Security P Zero trust architecture addresses security for all physical and virtual infrastructure, including routers, switches, servers, cloud services, and iot devices. it ensures that every component is continuously verified and protected, regardless of whether it resides on premises or in the cloud. Zero trust security, also known as a zero trust architecture or perimeterless security, assumes no one and no device or application is universally trusted, whether inside or outside the network. Zero trust (zt) is the term for an evolving set of cybersecurity paradigms that move defenses from static, network based perimeters to focus on users, assets, and resources. a zero trust architecture (zta) uses zero trust principles to plan industrial and enterprise infrastructure and workflows. This guide provides a comprehensive overview of zero trust principles, architectural models, practical implementation steps, and the tools needed to build a more secure and resilient organization. Discover the fundamentals of zero trust architecture and why every it professional must understand this vital security approach to protect modern organizations from evolving cyber threats. Discover how zero trust architecture transforms enterprise security by eliminating implicit trust, ensuring continuous verification across all users and systems.
Comments are closed.