Zero Trust Security A New Model For Cybersecurity
Embracing A Zero Trust Security Model Logrhythm National institute of standards and technology (2020) defines zero trust as a security model and a coordinated cybersecurity and system management strategy acknowledging that threats exist both inside and outside network boundaries. This guide provides a comprehensive overview of zero trust principles, architectural models, practical implementation steps, and the tools needed to build a more secure and resilient organization.

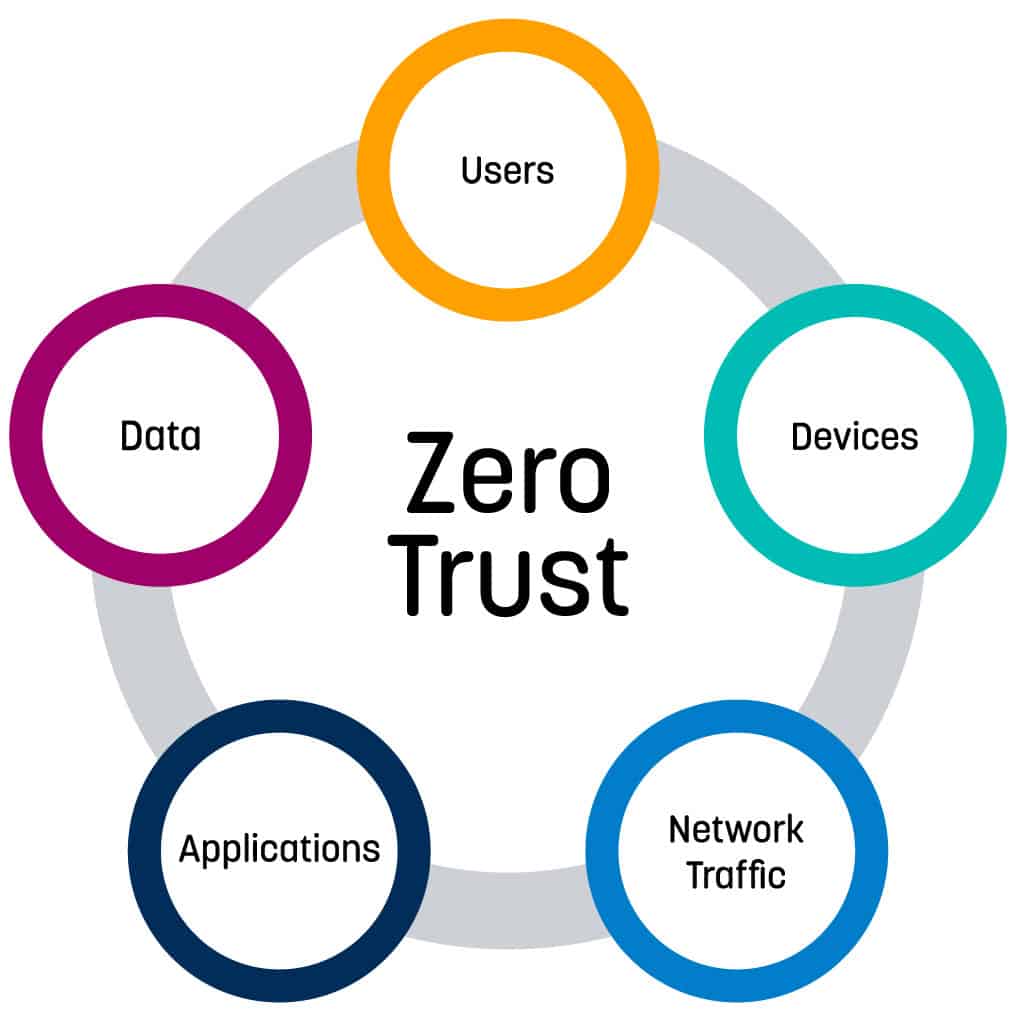
Zero Trust Security Model In Government Zero trust is a strategic approach to cybersecurity that assumes all network traffic, both external and internal, may be hostile. this model enforces strict identity verification, limited. This guidance contains an abstract definition of zero trust architecture (zta) and gives general deployment models and use cases where zero trust could improve an enterprise’s overall information technology security posture. Zero trust is a security framework that mandates stringent identity verification for every user and device attempting to access resources, regardless of whether they are inside or outside the organization’s network. Explore the transformative impact of the zero trust security model on cybersecurity. learn how it enhances access controls and real time monitoring for robust protection.
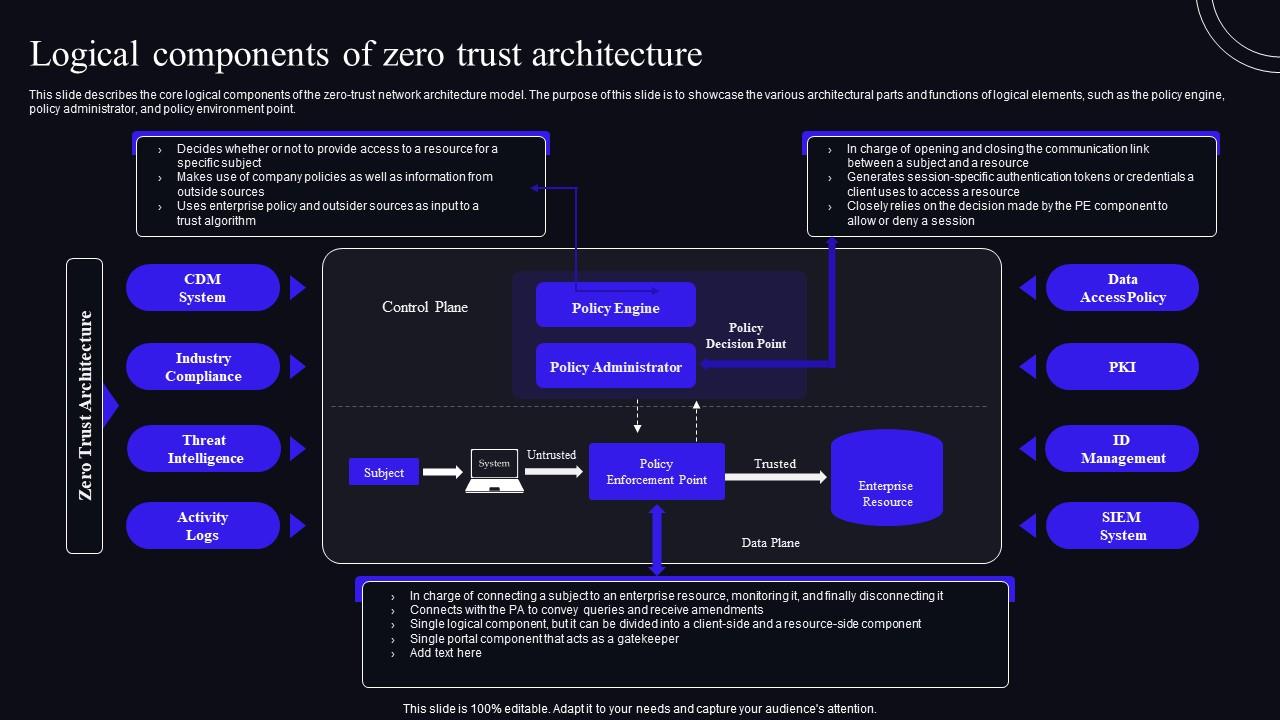
Logical Components Of Zero Trust Architecture Zero Trust Security Model Zero trust is a security framework that mandates stringent identity verification for every user and device attempting to access resources, regardless of whether they are inside or outside the organization’s network. Explore the transformative impact of the zero trust security model on cybersecurity. learn how it enhances access controls and real time monitoring for robust protection. As cyber threats grow more sophisticated and perimeter defenses falter, the zero trust security model embracing the mantra “never trust, always verify” has shifted from theory to essential practice. Organizations must shift to a more robust and dynamic cybersecurity framework: the zero trust approach (zta). rooted in the principle of “never trust, always verify,” zta ensures that access is granted based on strict authentication and continuous monitoring rather than assumed trust. Learn how zero trust works, why it matters, and how to build a modern security model aligned with nist 800 207 (strengthened by eti). To cope better with cyber threats such as the colonial pipeline ransomware attack that affected the largest refined oil pipeline in the united states of america (us), industry players are increasingly turning to the zero trust security model.
Comments are closed.