Zero Trust Section Connextek
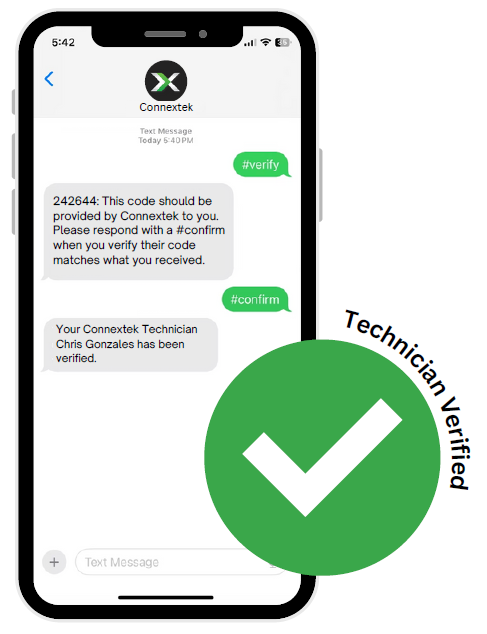
Zero Trust Section Connextek Connextek has adopted a zero trust policy (ztp). ztp is a cybersecurity approach based on the principle that no entity—whether inside or outside the organization—should be trusted by default. Get a comprehensive guide to key zero trust concepts, the most influential frameworks, top zero trust benefits, and best practices for selecting a zero trust vendor.

Zero Trust Networking Cohesive Networks Zero trust architecture (zta) is a security model that assumes no user, device, or network is trusted by default, whether inside or outside the organization's network. every access request must be authenticated, authorized, and continuously validated, applying the principle of least privilege. Zero trust network access (ztna) is the main technology that enables organizations to implement zero trust security. similar to a software defined perimeter (sdp), ztna conceals most infrastructure and services, setting up one to one encrypted connections between devices and the resources they need. Zero trust is a robust security model that works on the principle of “never trust, always verify” to ensure secure connections. understanding what is zero trust and implementing it can help organizations safeguard their crucial applications, devices, data, and resources. Connextek a adopté une politique de zero trust (ztp). une ztp est une approche de cybersécurité qui part du principe qu’aucune entité, qu’elle soit à l’intérieur ou à l’extérieur de l’organisation, ne peut être considérée comme digne de confiance par défaut.

Zero Trust Security Solution Iconz Webvisions Zero trust is a robust security model that works on the principle of “never trust, always verify” to ensure secure connections. understanding what is zero trust and implementing it can help organizations safeguard their crucial applications, devices, data, and resources. Connextek a adopté une politique de zero trust (ztp). une ztp est une approche de cybersécurité qui part du principe qu’aucune entité, qu’elle soit à l’intérieur ou à l’extérieur de l’organisation, ne peut être considérée comme digne de confiance par défaut. This guide seeks to contribute to the conversation by outlining a framework of capabilities that are necessary for the implementation of zero trust in any network, then provide specific design and configuration examples for achieving a strong zero trust posture. This article breaks down zero trust architecture, covering its core components and offering a zero trust vs. vpn comparison. it will also provide implementation strategies for zero trust and best practices. The concept of zero trust architecture (zta) is that implicit trust should never be granted to accounts and devices based on the fact that a device, network, or application is located inside the network perimeter. Our guidance helps you assess your readiness for zero trust, and helps you build a plan to get to zero trust. our guidance is based on our experience helping customers secure their organizations, and by implementing our own zero trust model for ourselves.
Comments are closed.