Zero Trust Pptx

Zerotrustmodelpresentation 200107094517 Pptx 3) the core tenants of zero trust include secure all communication, grant least permission, grant access to single resources at a time, make access policies dynamic, collect and use data to improve security, monitor assets, and periodically re evaluate trust. download as a pptx, pdf or view online for free. Contribute to hasecuritysolutions presentations development by creating an account on github.
Microsoft Zero Trust Adoption Resources Pptx Pptx Zero trust architecture (zta) is a security framework designed to minimize network vulnerabilities by enforcing strict access controls based on the principle of 'never trust, always verify.'. Cloud based software deployment & mgmt. intelligence for endpoint response. Zero trust architecture (zta) powerpoint is a cybersecurity model that requires strict identity verification for every user and device accessing resources. Our zero trust security model powerpoint presentation explores why businesses adopt ztna and demonstrates how it can enhance security and operational efficiency.

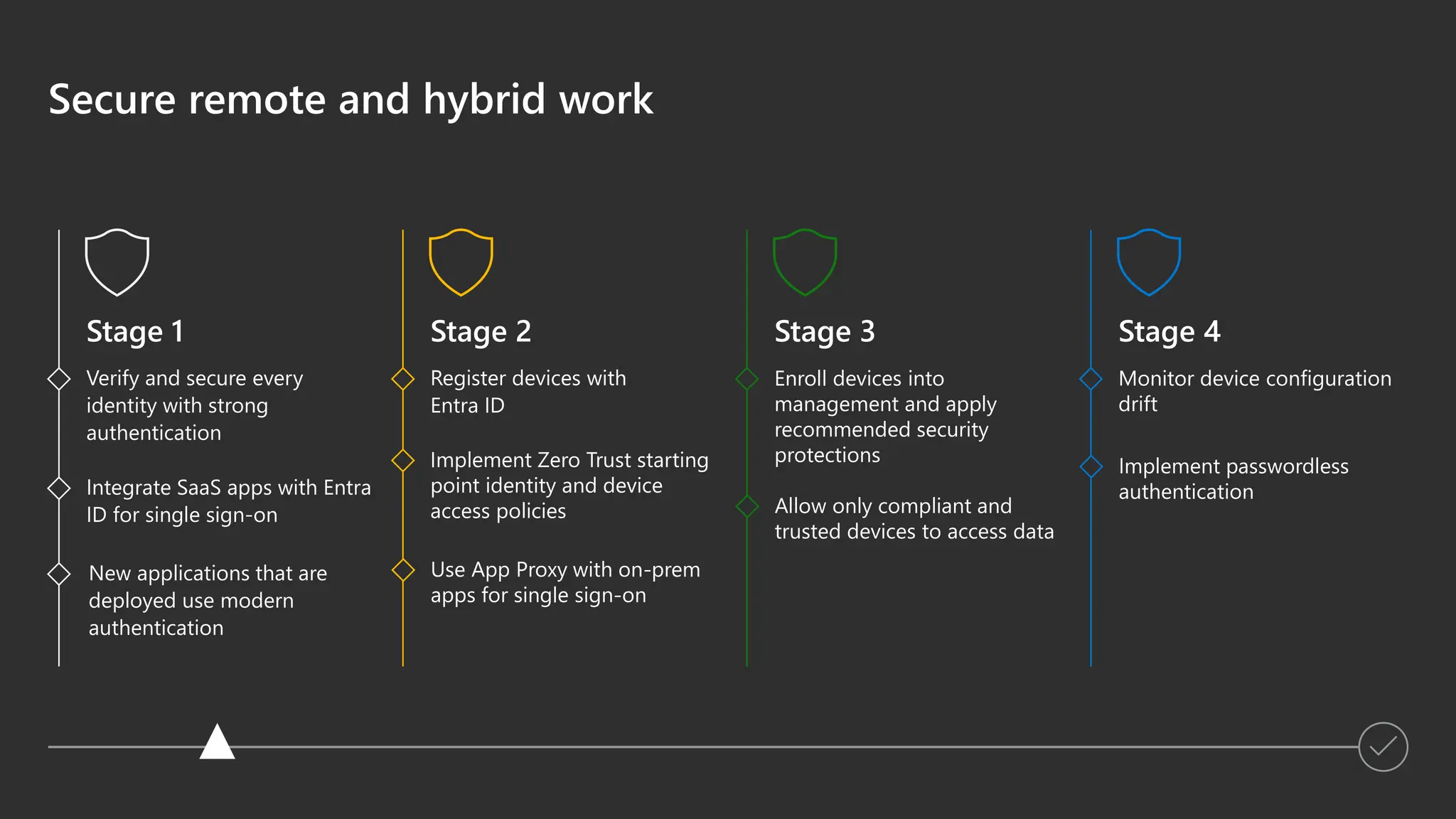
Zero Trust Architecture For It Security Pptx Zero trust architecture (zta) powerpoint is a cybersecurity model that requires strict identity verification for every user and device accessing resources. Our zero trust security model powerpoint presentation explores why businesses adopt ztna and demonstrates how it can enhance security and operational efficiency. Download this well researched powerpoint and google slides template to describe how zero trust architecture (zta) helps enterprises keep their systems and networks safe from cyber threats with the ‘never trust, always verify’ principle. Download our timeless zero trust ppt template to showcase the cybersecurity policy developed to prevent cyber attacks by considering that no user can be trusted without verification. Track recommended tasks across four stages. read the included instructions to use the tracking features. customize these for your organization. stakeholder teams for each business scenario. example stakeholder teams for each business scenario. customize the team for your organization. also download this excel workbook to track owners and tasks. A zero trust security model ensures that no one is trusted by default on a network, making it more secure and less vulnerable to attacks. in this presentation, we'll explore the principles of zero trust and its application in cloud security.
Microsoft Zero Trust Adoption Resources Pptx Pptx It And Internet Download this well researched powerpoint and google slides template to describe how zero trust architecture (zta) helps enterprises keep their systems and networks safe from cyber threats with the ‘never trust, always verify’ principle. Download our timeless zero trust ppt template to showcase the cybersecurity policy developed to prevent cyber attacks by considering that no user can be trusted without verification. Track recommended tasks across four stages. read the included instructions to use the tracking features. customize these for your organization. stakeholder teams for each business scenario. example stakeholder teams for each business scenario. customize the team for your organization. also download this excel workbook to track owners and tasks. A zero trust security model ensures that no one is trusted by default on a network, making it more secure and less vulnerable to attacks. in this presentation, we'll explore the principles of zero trust and its application in cloud security.
Comments are closed.