Zero Trust Network Security Principles And Challenge

Zero Trust Network Security Principles And Challenge Get a comprehensive guide to key zero trust concepts, the most influential frameworks, top zero trust benefits, and best practices for selecting a zero trust vendor. This paper systematically compares the current mainstream cybersecurity models, thoroughly explores the advantages and limitations of the zero trust model, and provides an in depth review of its components and key technologies.

Zero Trust Network Security Principles And Challenge This guide provides a comprehensive overview of zero trust principles, architectural models, practical implementation steps, and the tools needed to build a more secure and resilient organization. Zero trust (zt) is the term for an evolving set of cybersecurity paradigms that move defenses from static, network based perimeters to focus on users, assets, and resources. a zero trust architecture (zta) uses zero trust principles to plan industrial and enterprise infrastructure and workflows. zero trust assumes there is no implicit trust granted to assets or user accounts based solely on. Explore the core principles of zero trust network security, its challenges, real world implementations, and emerging trends. Learn how to implement zero trust architecture with best practices, overcome challenges, and ensure compliance for robust cybersecurity.
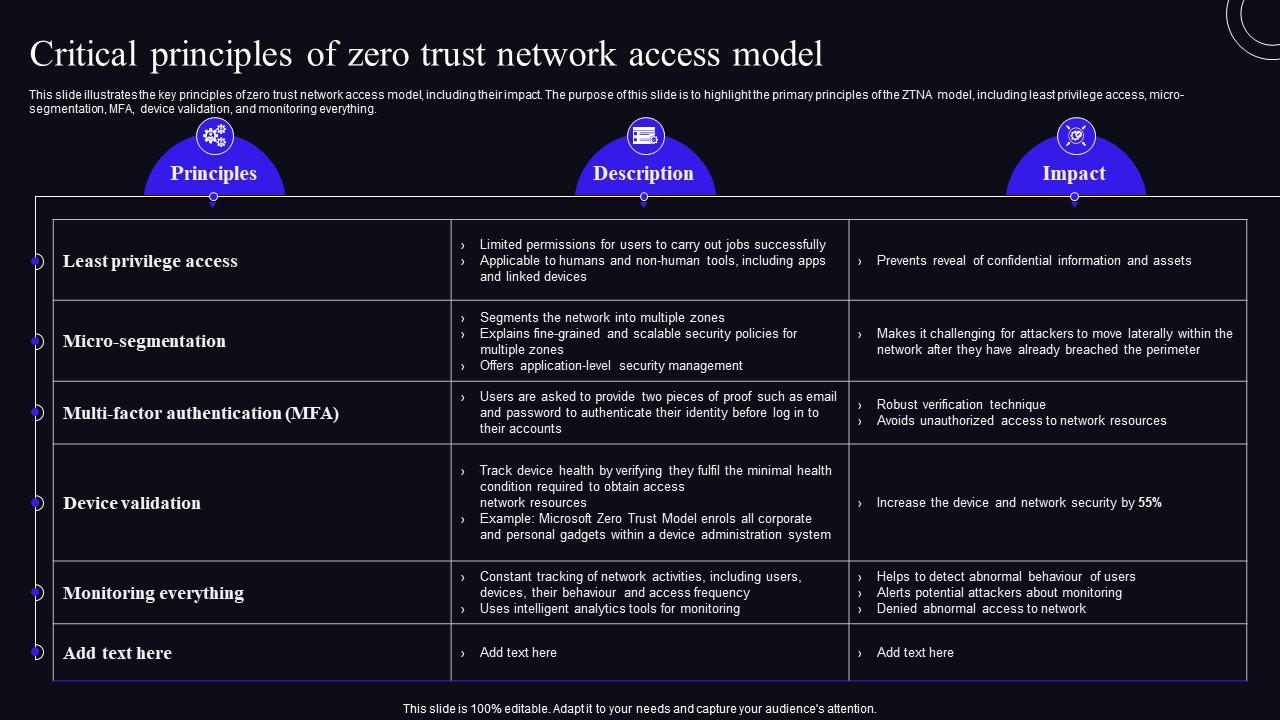
Critical Principles Of Zero Trust Network Access Model Zero Trust Explore the core principles of zero trust network security, its challenges, real world implementations, and emerging trends. Learn how to implement zero trust architecture with best practices, overcome challenges, and ensure compliance for robust cybersecurity. It explores how organizations can transition to zero trust architectures, the challenges associated with its implementation, and the technologies that enable its adoption, such as artificial intelligence (ai), multi factor authentication (mfa), and zero trust network access (ztna). Zero trust is a novel paradigm for cybersecurity based on the core concept of “never trust, always verify”. it attempts to protect against security risks related to internal threats by eliminating the demarcations between the internal and external network of traditional network perimeters. This paper evaluates zero trust strategy in contemporary enterprise networks through analysis of its critical elements such as identity and access management (iam) and micro segmentation and continuous monitoring and discusses implementation challenges and best practices. Explore zero trust security: key principles, benefits, challenges, and 6 implementation strategies for enhanced protection.

Premium Photo Zero Trust Network Architecture Security Principles It explores how organizations can transition to zero trust architectures, the challenges associated with its implementation, and the technologies that enable its adoption, such as artificial intelligence (ai), multi factor authentication (mfa), and zero trust network access (ztna). Zero trust is a novel paradigm for cybersecurity based on the core concept of “never trust, always verify”. it attempts to protect against security risks related to internal threats by eliminating the demarcations between the internal and external network of traditional network perimeters. This paper evaluates zero trust strategy in contemporary enterprise networks through analysis of its critical elements such as identity and access management (iam) and micro segmentation and continuous monitoring and discusses implementation challenges and best practices. Explore zero trust security: key principles, benefits, challenges, and 6 implementation strategies for enhanced protection.
Comments are closed.