Zero Trust Network Access On Ramp Option 1 User And Device Identity

Zero Trust Network Access On Ramp Option 1 User And Device Identity This rapid modernization plan (ramp) checklist helps you establish a security perimeter for cloud applications and mobile devices that uses identity as the control plane and explicitly validates trust for user accounts and devices before allowing access, for both public and private networks. This zero trust guide for user and device security is presented as one part in a series that also covers zero trust capabilities for network, cloud, applications, and data.

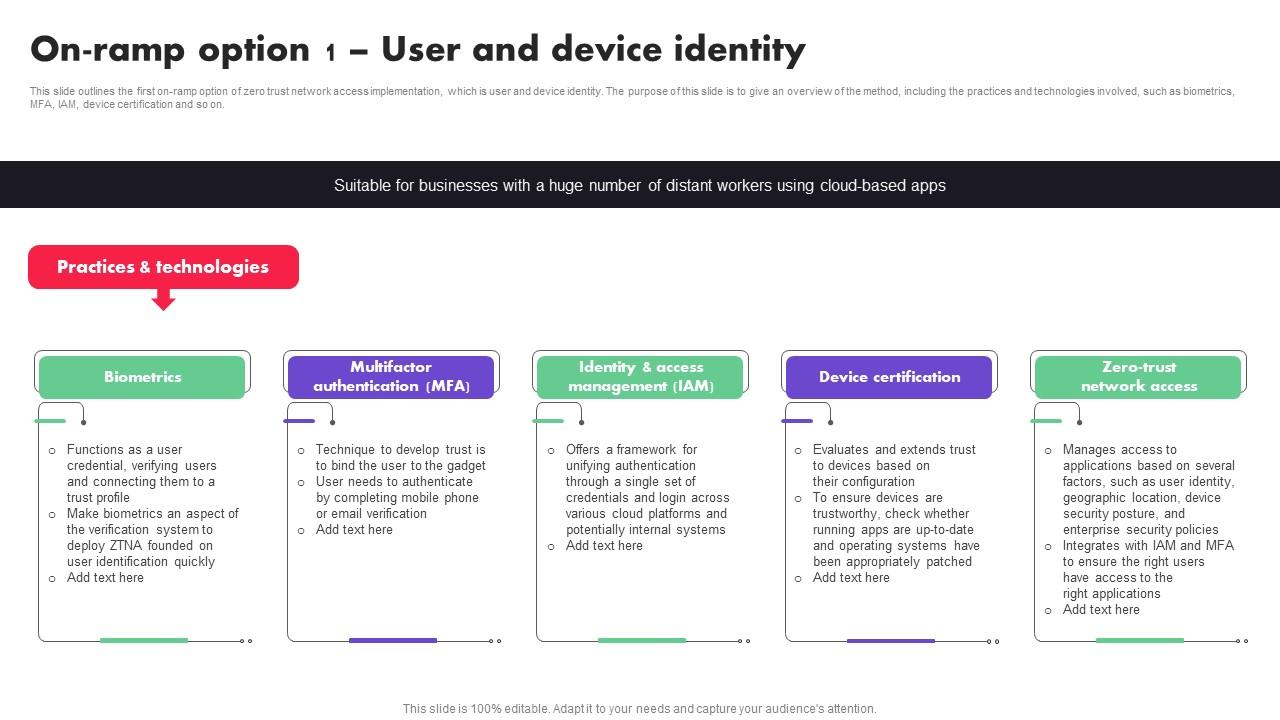
On Ramp Option 1 User And Device Identity Zero Trust Network Security This slide outlines the first on ramp option of zero trust network access implementation, which is user and device identity. the purpose of this slide is to give an overview of the method, including the practices and technologies involved, such as biometrics, mfa, iam, device certification and so on. This rapid modernization plan (ramp) checklist helps you establish a security perimeter for cloud applications and mobile devices that uses identity as the control plane and explicitly validates trust for user accounts and devices before allowing access, for both public and private networks. Background •prior to secure firewall 7.4, organizations wanting to grant users access to private applications and implement zero trust were required to install additional software installed (like anyconnect secure client) on client devices. This slide outlines the first on ramp option of zero trust network access implementation, which is user and device identity. the purpose of this slide is to give an overview of the method, including the practices and technologies involved, such as biometrics, mfa, iam, device certification and so on.

Zero Trust Model On Ramp Option 1 User And Device Identity Background •prior to secure firewall 7.4, organizations wanting to grant users access to private applications and implement zero trust were required to install additional software installed (like anyconnect secure client) on client devices. This slide outlines the first on ramp option of zero trust network access implementation, which is user and device identity. the purpose of this slide is to give an overview of the method, including the practices and technologies involved, such as biometrics, mfa, iam, device certification and so on. Below are practical examples for each zero trust rapid modernization plan (ramp) initiative tailored for a critical infrastructure power station. Zero trust is different it checks every person and device every time they try to access something, just like having security guards at every door. this approach prevents attackers who get inside your network from moving around and stealing data. In our zero trust guides, we define the approach to implement an end to end zero trust methodology across identities, endpoints and devices, data, apps, infrastructure, and network. This use case explains how to set up a cloudflare access application to define secure access for employees, giving them fully functional access when they are on a secured device over a secured connection, but still allow them some limited access from a non secure device.
On Ramp Option 1 User And Device Identity Zero Trust Architecture Zta Below are practical examples for each zero trust rapid modernization plan (ramp) initiative tailored for a critical infrastructure power station. Zero trust is different it checks every person and device every time they try to access something, just like having security guards at every door. this approach prevents attackers who get inside your network from moving around and stealing data. In our zero trust guides, we define the approach to implement an end to end zero trust methodology across identities, endpoints and devices, data, apps, infrastructure, and network. This use case explains how to set up a cloudflare access application to define secure access for employees, giving them fully functional access when they are on a secured device over a secured connection, but still allow them some limited access from a non secure device.
Comments are closed.