Zero Trust Network Access Implementation Challenges Rules Pdf

Zero Trust Network Access Implementation Challenges Rules Pdf It explores how organizations can transition to zero trust architectures, the challenges associated with its implementation, and the technologies that enable its adoption, such as artificial intelligence (ai), multi factor authentication (mfa), and zero trust network access (ztna). This paper delves into the theoretical underpinnings, practical applications, and future opportunities of zero trust security.
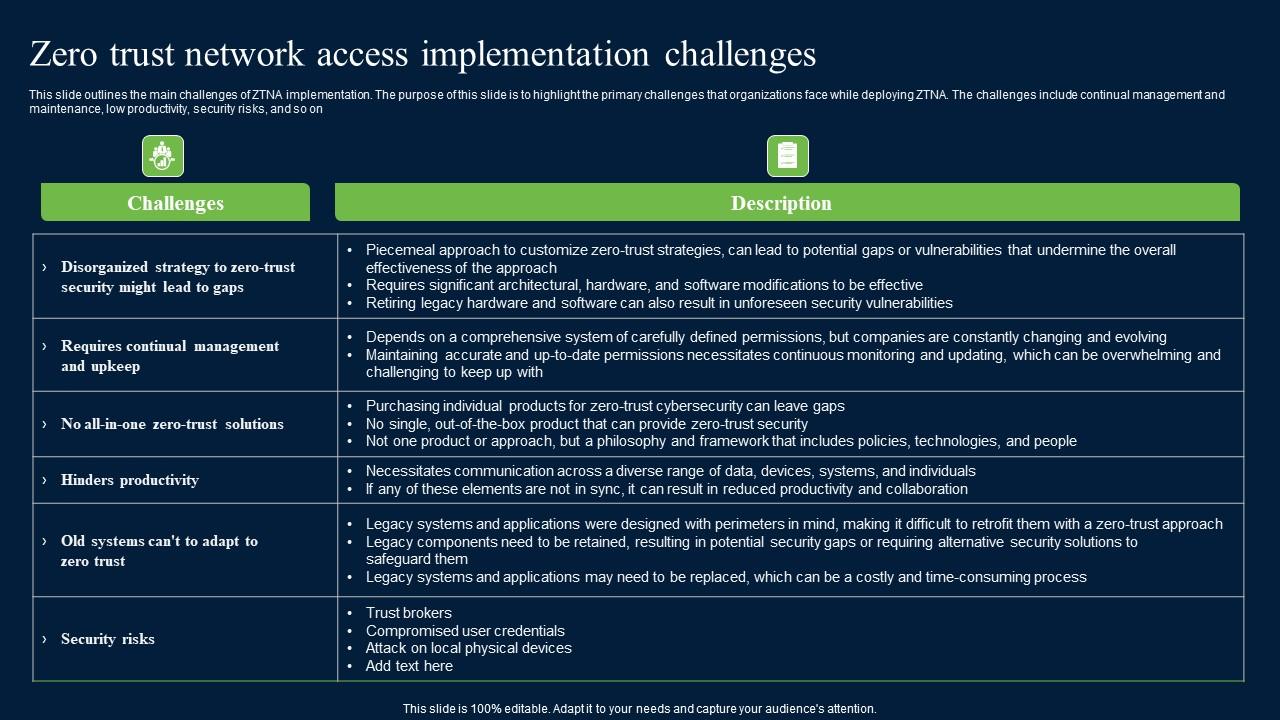
Zero Trust Network Access Implementation Challenges Mockup Pdf Zero trust architecture (zta) represents a fundamental transformation from conventional perimeter based security frameworks by implementing the principles of "never trust, always verify." this study examines the deployment of zta, its challenges, applications, and its effect on network security. Traditional “castle and moat” security models, which implicitly trust users and devices inside the network boundary, are proving inadequate against internal and external threats. zero trust architecture (zta) has emerged as a strategic response to these challenges. Abstract— zero trust architecture (zta) has emerged as a critical cybersecurity framework in response to increasingly sophisticated cyber threats. this study examines the practical considerations, obstacles, advantages, and principles of zta deployment in companies. This paper evaluates zero trust strategy in contemporary enterprise networks through analysis of its critical elements such as identity and access management (iam) and micro segmentation and continuous monitoring and discusses implementation challenges and best practices.

Zero Trust Network Access 7 0 Architecture Guide Pdf Proxy Server Abstract— zero trust architecture (zta) has emerged as a critical cybersecurity framework in response to increasingly sophisticated cyber threats. this study examines the practical considerations, obstacles, advantages, and principles of zta deployment in companies. This paper evaluates zero trust strategy in contemporary enterprise networks through analysis of its critical elements such as identity and access management (iam) and micro segmentation and continuous monitoring and discusses implementation challenges and best practices. In this paper, we first explore the foundational principles of zta, including continuous authentication, least privilege access, and reducing attack surfaces using micro segmentation. Thus, this paper explores challenges and solutions for zta policy design in the context of distributed networks, which is referred to as zero trust distributed networks (ztdn). In this paper, we first explore the foundational principles of zta, including continuous authentication, least privilege access, and reducing attack surfaces using micro segmentation. The article defines zero trust architecture, lists the characteristics of the common network security architecture, and provides an overview of its implementation.
Zero Trust Network Access Implementation Challenges Ppt File Rules Ppt In this paper, we first explore the foundational principles of zta, including continuous authentication, least privilege access, and reducing attack surfaces using micro segmentation. Thus, this paper explores challenges and solutions for zta policy design in the context of distributed networks, which is referred to as zero trust distributed networks (ztdn). In this paper, we first explore the foundational principles of zta, including continuous authentication, least privilege access, and reducing attack surfaces using micro segmentation. The article defines zero trust architecture, lists the characteristics of the common network security architecture, and provides an overview of its implementation.
Comments are closed.