Zero Trust Network Access Implementation Challenges Mockup Pdf
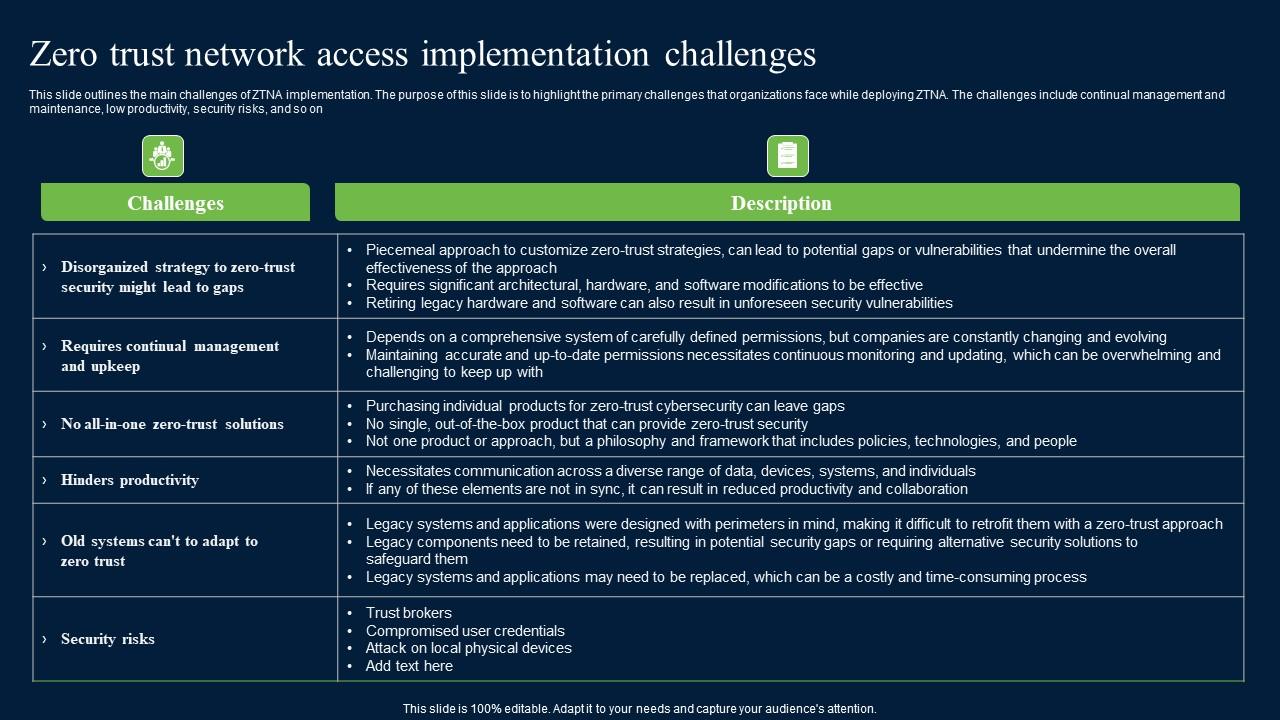
Zero Trust Network Access Implementation Challenges Mockup Pdf This slide outlines the main challenges of ztna implementation. the purpose of this slide is to highlight the primary challenges that organizations face while deploying ztna. This survey comprehensively explores the theoretical foundations, practical implementations, applications, challenges, and future trends of zero trust.

Zero Trust Network Access Implementation Challenges Rules Pdf Zero trust architecture (zta) represents a fundamental transformation from conventional perimeter based security frameworks by implementing the principles of "never trust, always verify." this study examines the deployment of zta, its challenges, applications, and its effect on network security. Experiences and perspectives of it professionals, cybersecurity experts, and other relevant stakeholders, this study seeks to provide valuable insights into the current state of zero trust. It explores how organizations can transition to zero trust architectures, the challenges associated with its implementation, and the technologies that enable its adoption, such as artificial intelligence (ai), multi factor authentication (mfa), and zero trust network access (ztna). Abstract— zero trust architecture (zta) has emerged as a critical cybersecurity framework in response to increasingly sophisticated cyber threats. this study examines the practical considerations, obstacles, advantages, and principles of zta deployment in companies.

Zero Trust Network Access 7 0 Architecture Guide Pdf Proxy Server It explores how organizations can transition to zero trust architectures, the challenges associated with its implementation, and the technologies that enable its adoption, such as artificial intelligence (ai), multi factor authentication (mfa), and zero trust network access (ztna). Abstract— zero trust architecture (zta) has emerged as a critical cybersecurity framework in response to increasingly sophisticated cyber threats. this study examines the practical considerations, obstacles, advantages, and principles of zta deployment in companies. The zero trust architecture (zta) model has emerged as a foundational cybersecurity paradigm that eliminates implicit trust and enforces continuous verification across users, devices, and networks. Traditional “castle and moat” security models, which implicitly trust users and devices inside the network boundary, are proving inadequate against internal and external threats. zero trust architecture (zta) has emerged as a strategic response to these challenges. The central assumption of zero trust network access is that users in the system begin their access journey with the lowest possible level of authorization and ensure that everything is verified at every step. Cloud computing has become essential in this digital world as it provides opportunities and challenges for organizations. this research explores the implementation and effectiveness of zero trust architecture (zta) in addressing security challenges within cloud networks.

Challenges Of Vpn Based Remote Access Zero Trust Network Security Ideas Pdf The zero trust architecture (zta) model has emerged as a foundational cybersecurity paradigm that eliminates implicit trust and enforces continuous verification across users, devices, and networks. Traditional “castle and moat” security models, which implicitly trust users and devices inside the network boundary, are proving inadequate against internal and external threats. zero trust architecture (zta) has emerged as a strategic response to these challenges. The central assumption of zero trust network access is that users in the system begin their access journey with the lowest possible level of authorization and ensure that everything is verified at every step. Cloud computing has become essential in this digital world as it provides opportunities and challenges for organizations. this research explores the implementation and effectiveness of zero trust architecture (zta) in addressing security challenges within cloud networks.

A51 Zero Trust Network Access Implementation Challenges The central assumption of zero trust network access is that users in the system begin their access journey with the lowest possible level of authorization and ensure that everything is verified at every step. Cloud computing has become essential in this digital world as it provides opportunities and challenges for organizations. this research explores the implementation and effectiveness of zero trust architecture (zta) in addressing security challenges within cloud networks.
Comments are closed.