Zero Trust Network Access Buyers Guide Pdf

Zero Trust Network Access Buyers Guide Pdf Zero trust network access buyers guide free download as pdf file (.pdf), text file (.txt) or read online for free. In response to these challenges and evolving security needs, organizations are shifting to zero trust network access (ztna) technologies that offer a more tailored and secure approach to connecting remote users and devices.

Zero Trust Network Access 7 0 Architecture Guide Pdf Proxy Server Ztna solution when accessing internal applications from the office. this scenario exemplifies the pain point of choosing a zero trust solution that can’t keep up w th performance demands, leading to delays and hampered productivity. it’s critical to choose a solution that not only enforces security policies. Zero trust network access (ztna) is software defined functionality that enables secure access to networks and applications. the concept evolved from traditional security measures but flips the concept of trust on its head. What zero trust network access is and why it's an important part of modern network security. download now the buyer’s guide. Establish a high level zero trust strategy first and ensure that your identity and access management technologies and processes are well understood and mature before selecting and implementing a ztna solution.

Zero Trust Architecture Buyers Guide V11 20210810 Pdf Computer What zero trust network access is and why it's an important part of modern network security. download now the buyer’s guide. Establish a high level zero trust strategy first and ensure that your identity and access management technologies and processes are well understood and mature before selecting and implementing a ztna solution. Remote access vpns for application access. this market guide, which includes a list of representative vendors and their products, will help security and risk management leaders evaluate ztna. Our ztna buyers' guide covers key features, deployment models, top vendors, and criteria to help you choose the right zero trust network access solution. Welcome to the zero trust buyer’s guide! the zero trust market stands out due to its transformative approach to security. it replaces the traditional “trust but verify” model with the more rigorous “never trust, always verify” framework. Ztna is a category of products that operationalize the zero trust principle, granting access to specific resources only after authenticating the user’s identity and ensuring they have explicit permission to access that resource.

Zero Trust Network Access Buyer Guide Recommendations Key Features More Remote access vpns for application access. this market guide, which includes a list of representative vendors and their products, will help security and risk management leaders evaluate ztna. Our ztna buyers' guide covers key features, deployment models, top vendors, and criteria to help you choose the right zero trust network access solution. Welcome to the zero trust buyer’s guide! the zero trust market stands out due to its transformative approach to security. it replaces the traditional “trust but verify” model with the more rigorous “never trust, always verify” framework. Ztna is a category of products that operationalize the zero trust principle, granting access to specific resources only after authenticating the user’s identity and ensuring they have explicit permission to access that resource.

Technologies Used In Zero Trust Network Access Zero Trust Network Security Welcome to the zero trust buyer’s guide! the zero trust market stands out due to its transformative approach to security. it replaces the traditional “trust but verify” model with the more rigorous “never trust, always verify” framework. Ztna is a category of products that operationalize the zero trust principle, granting access to specific resources only after authenticating the user’s identity and ensuring they have explicit permission to access that resource.
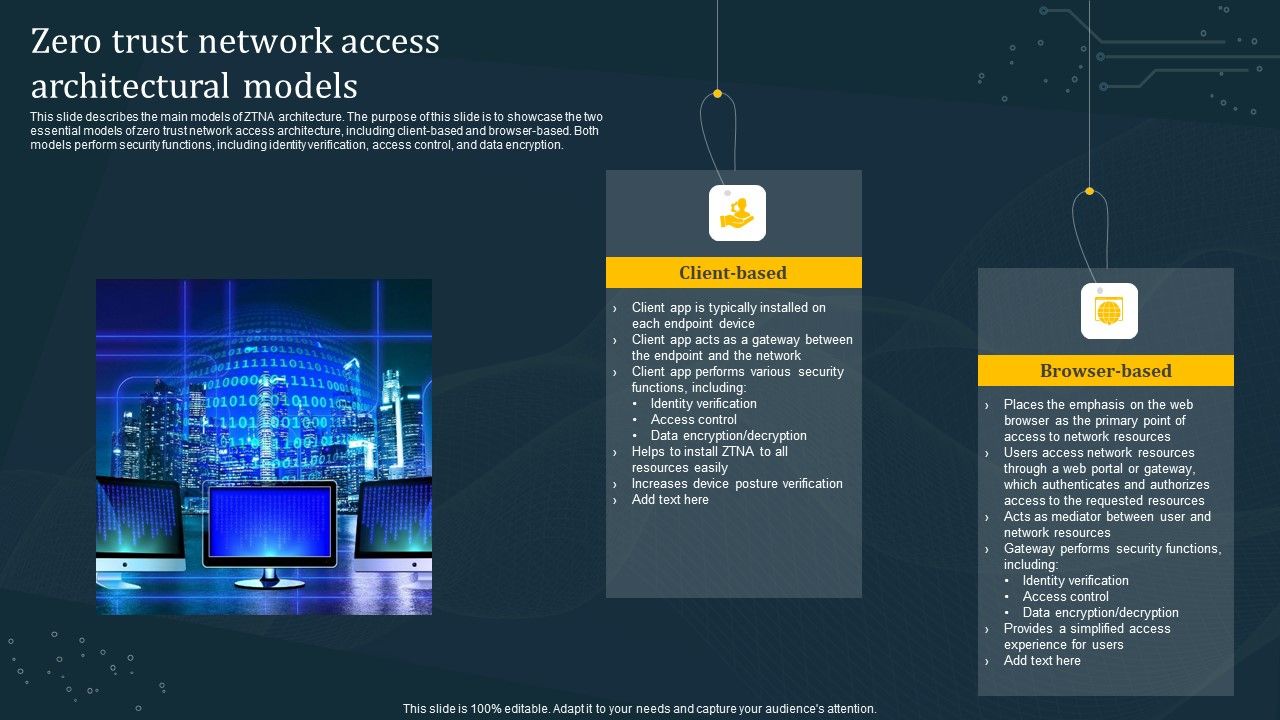
Zero Trust Network Access Architectural Models Diagrams Pdf
Comments are closed.