Zero Trust Network Access Architectural Models Ppt File Inspiration Ppt

Zero Trust Network Access Architectural Models Ppt File Inspiration Ppt Zero trust is a security model based on the principle of maintaining strict access controls and not trusting anyone by default, even those already inside the network perimeter. Our zero trust security model powerpoint presentation explores why businesses adopt ztna and demonstrates how it can enhance security and operational efficiency. additionally, the zero trust model ppt delves into the architecture of ztna, encompassing user and architectural workflows.
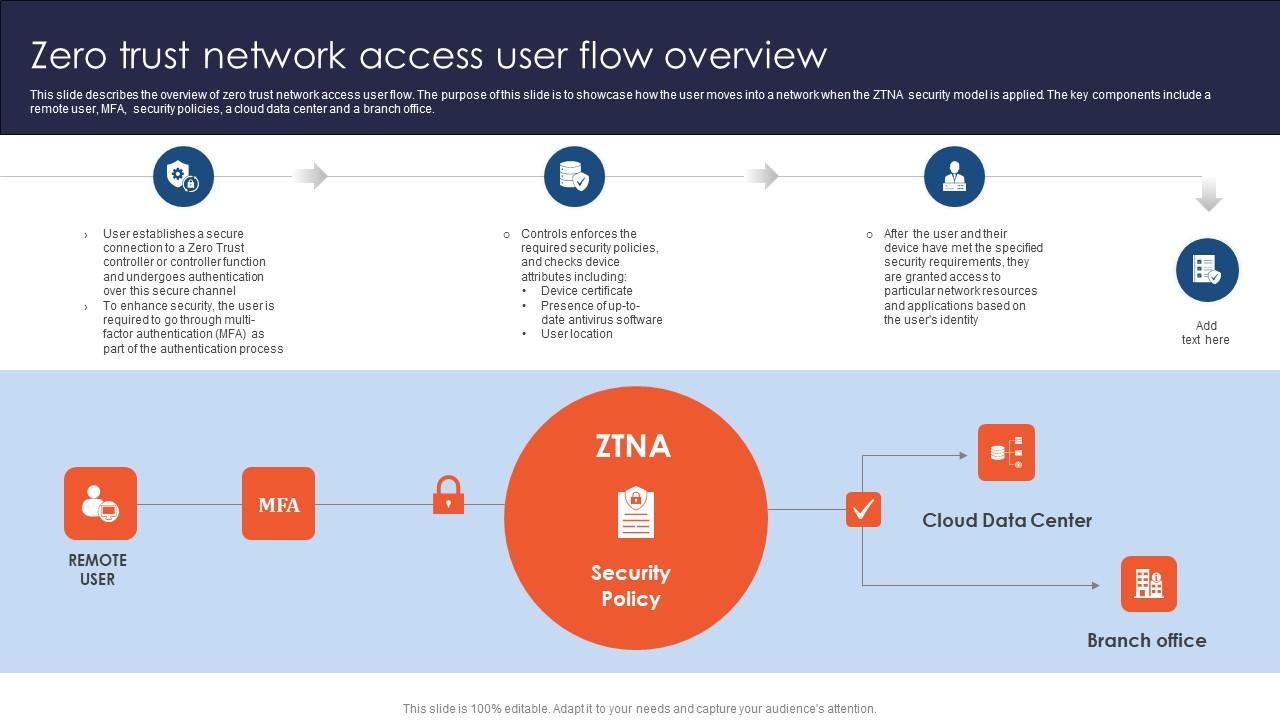
Zero Trust Network Access User Flow Overview Ppt File Deck Slidegeeks has constructed zero trust network access working functions of zero trust network access architecture after conducting extensive research and examination. these presentation templates are constantly being generated and modified based on user preferences and critiques from editors. Zero trust architecture detailed presentation free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online. Download our zero trust architecture template for powerpoint and google slides to describe how this cybersecurity model helps improve security posture and protect from costly breaches. • a zero trust network security model is based on the philosophy that no person or device inside or outside of an organization should be granted access to connect to it systems or services until authenticated and continuously verified.
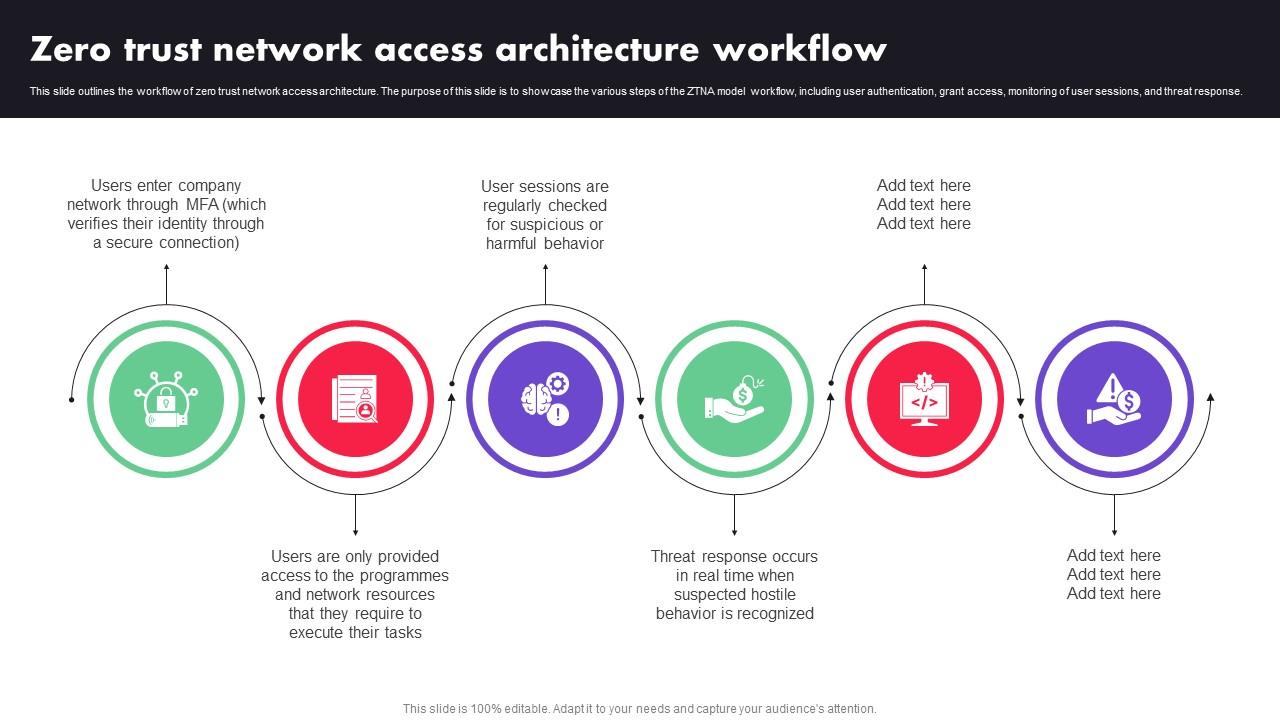
Zero Trust Network Access Architecture Workflow Ppt File Picture Ppt Download our zero trust architecture template for powerpoint and google slides to describe how this cybersecurity model helps improve security posture and protect from costly breaches. • a zero trust network security model is based on the philosophy that no person or device inside or outside of an organization should be granted access to connect to it systems or services until authenticated and continuously verified. This document discusses zero trust security and how to implement a zero trust network architecture. it begins with an overview of zero trust and why it is important given limitations of traditional perimeter based networks. This slide gives an overview of the working features of zero trust network access architecture. the purpose of this slide is to highlight the various functions that ztna architecture performs, including identification, protection, detection and response to threats. Introducing zero trust network access architectural models ppt file inspiration to increase your presentation threshold. encompassed with two stages, this template is a great option to educate and entice your audience. Welcome to our selection of the zero trust network access traditional security models vs zero trust network access. these are designed to help you showcase your creativity and bring your sphere to life.
Comments are closed.