Zero Trust Network Access Architectural Models Ideas Pdf
Zero Trust Network Access Architectural Models Ideas Pdf This article provides a comprehensive analysis of zero trust architecture, its core principles, and its implementation strategies. The objective of this publication is to provide guidance for realizing an architecture that can enforce granular application level policies while meeting the runtime requirements of zta for multi cloud and hybrid environments.
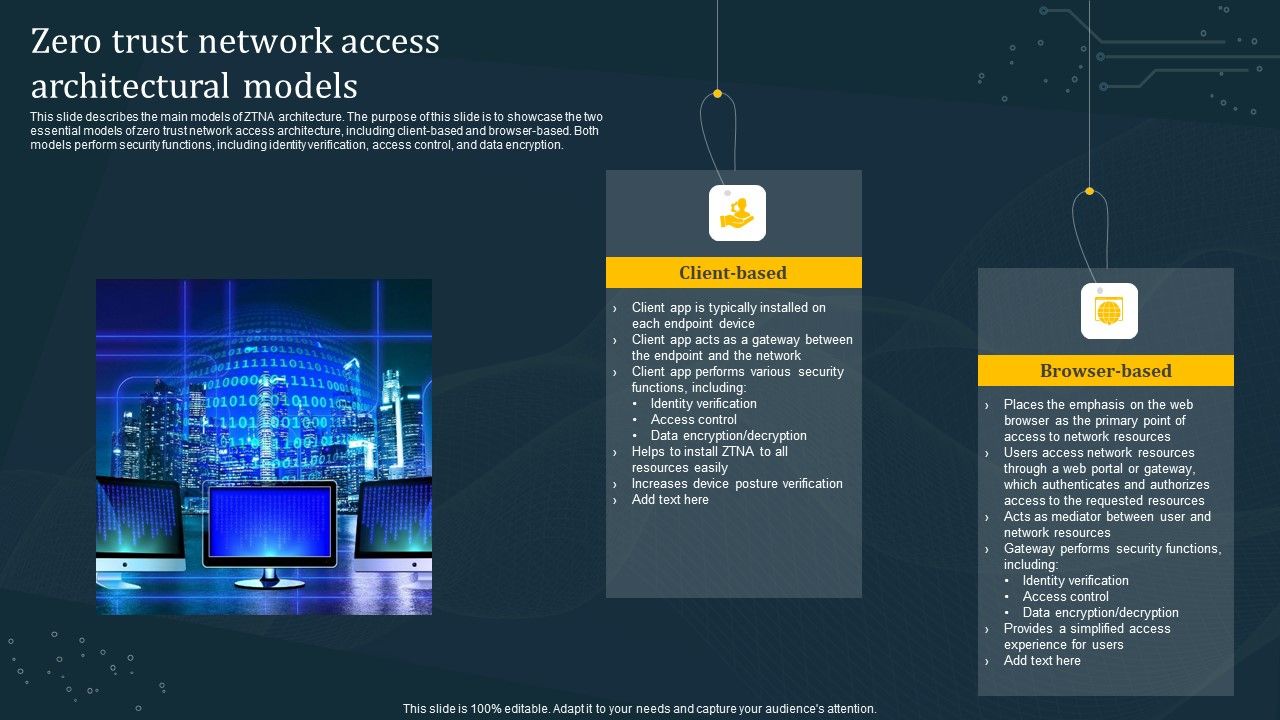
Zero Trust Network Access Architectural Models Diagrams Pdf Zero trust architecture (zta) emerges as a pivotal paradigm shift, fundamentally redefining organizational cybersecurity by eliminating implicit trust and enforcing continuous verification of every access request. This paper explores the concept of zero trust architecture (zta), which fundamentally shifts the paradigm from a trust based model to one that assumes no implicit trust, regardless of the network location [1,2]. Therefore, in this paper, we have proposed a novel architecture for cloud security with the incorporation of existing ztna (zero trust network access) of the zts model where csb plays a significant role in continuously verifying the requestor cloud entity throughout the life span of the session. This whitepaper provides a comprehensive guide to understanding and implementing zero trust architecture, exploring its principles, benefits, challenges, and future directions in enhancing cyber defense strategies.

Zero Trust Network Access 7 0 Architecture Guide Pdf Proxy Server Therefore, in this paper, we have proposed a novel architecture for cloud security with the incorporation of existing ztna (zero trust network access) of the zts model where csb plays a significant role in continuously verifying the requestor cloud entity throughout the life span of the session. This whitepaper provides a comprehensive guide to understanding and implementing zero trust architecture, exploring its principles, benefits, challenges, and future directions in enhancing cyber defense strategies. Zero trust network access (ztna) marks a significant shift in network security by adopting a “never trust, always verify” approach. this work provides an in depth analysis of ztna, offering a compre hensive framework for understanding its principles, architectures, and applications. As highlighted later in table 2, automated resilience strategies not only reduce downtime but also enhance operational trust, demonstrating why network redundancy and recovery form the backbone of financial continuity planning under zero trust. At its core, ztna operates on the principle of “never trust, always verify.” this means that no user or device, whether inside or outside the network perimeter, is automatically trusted. instead, every access request is thoroughly vetted before granting permission. The survey begins by examining the role of authentication and access control within zero trust architectures, and subsequently investigates innovative authentication, as well as access control solutions across different scenarios.
Comments are closed.