Zero Trust Network Access Architectural Models Diagrams Pdf
Zero Trust Network Access Architectural Models Diagrams Pdf Zero trust network access (ztna) is an access control method that uses client device identification, authentication, and zero trust tags to provide role based application access. it gives administrators the flexibility to manage network access for on net local users and off net remote users. Zero trust architecture (zta) is an enterprise’s cybersecurity plan that uses zero trust concepts and encompasses component relationships, workflow planning, and access policies.
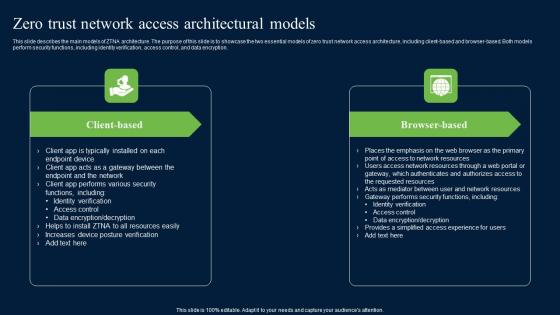
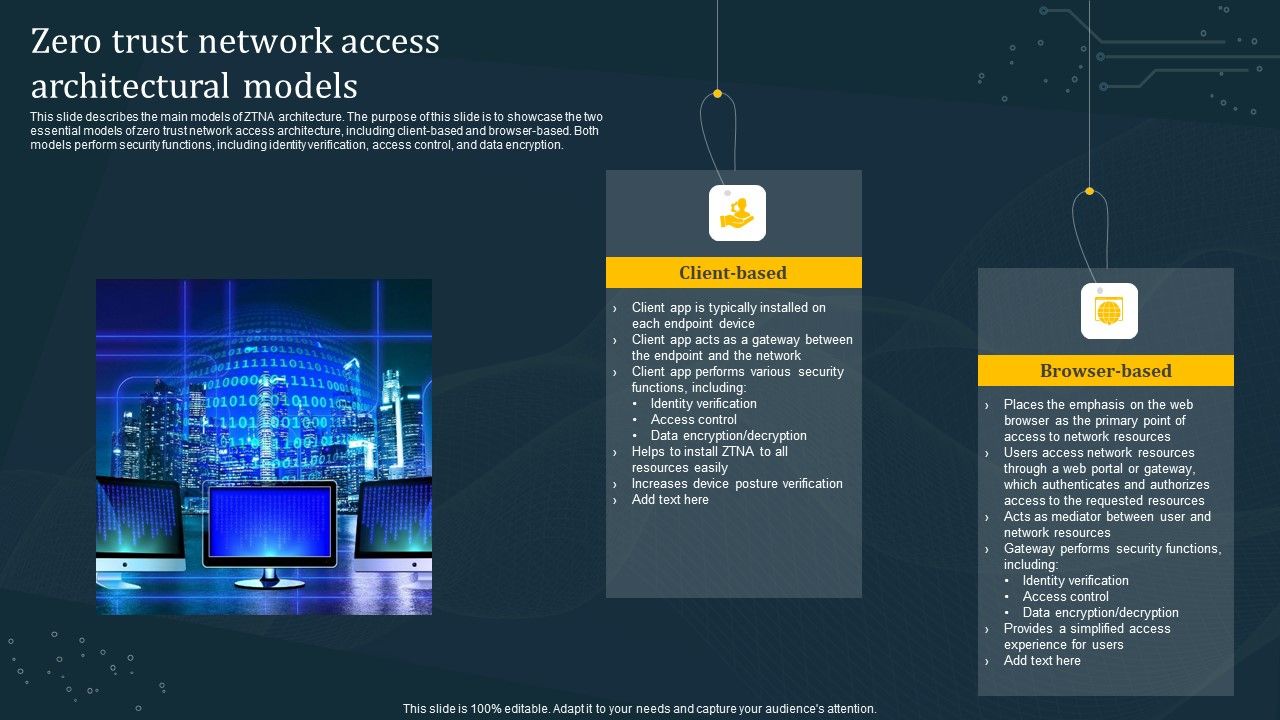
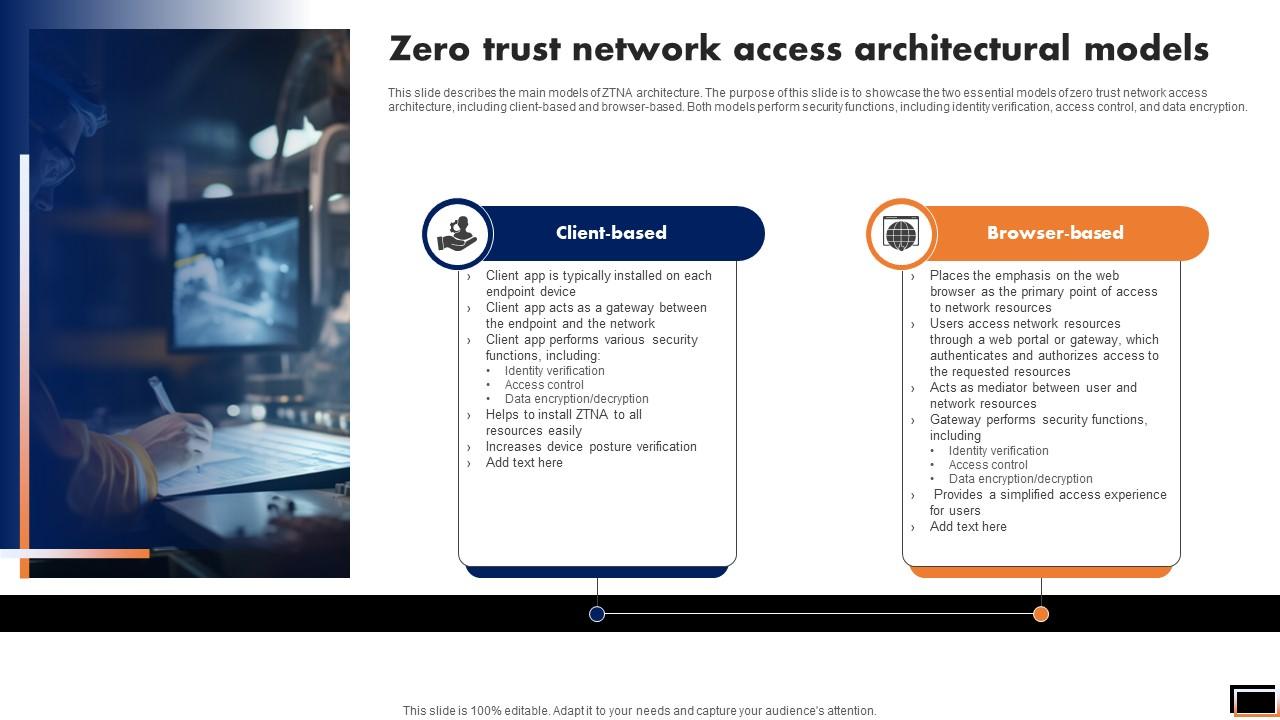
Zero Trust Network Access Architectural Models Ideas Pdf This research proposes a comprehensive access control model aligned with the fundamental zta security principles, namely least privilege, conditional access, and continuous monitoring. Nist special publication 800 207 has laid out a comprehensive set of zero trust principles and referenced zero trust architectures (zta) for turning those concepts into reality. This slide describes the main models of ztna architecture. the purpose of this slide is to showcase the two essential models of zero trust network access architecture, including client based and browser based. Zero trust network access (ztna) marks a significant shift in network security by adopting a “never trust, always verify” approach. this work provides an in depth analysis of ztna, offering a compre hensive framework for understanding its principles, architectures, and applications.

Zero Trust Network Access Vs Zero Trust Architecture Diagrams Pdf This slide describes the main models of ztna architecture. the purpose of this slide is to showcase the two essential models of zero trust network access architecture, including client based and browser based. Zero trust network access (ztna) marks a significant shift in network security by adopting a “never trust, always verify” approach. this work provides an in depth analysis of ztna, offering a compre hensive framework for understanding its principles, architectures, and applications. Print or customize technical illustrations in the zero trust library for your deployment. From this ra, reference designs (rd) can be created that capture a zt logical architecture for specific environments and functional needs. This document demonstrates ztra as a foundational zero trust network access framework and provides best practices to strengthen it with security offerings from intel xeon scalable processors. This infographic explores the steps to implement a zta, drawing insights from sans institute’s zero trust strategy guide * and the national cybersecurity center of excellence (nccoe) at the national institute of standards and technology (nist).

A48 Zero Trust Network Access Architectural Models Print or customize technical illustrations in the zero trust library for your deployment. From this ra, reference designs (rd) can be created that capture a zt logical architecture for specific environments and functional needs. This document demonstrates ztra as a foundational zero trust network access framework and provides best practices to strengthen it with security offerings from intel xeon scalable processors. This infographic explores the steps to implement a zta, drawing insights from sans institute’s zero trust strategy guide * and the national cybersecurity center of excellence (nccoe) at the national institute of standards and technology (nist).
Zero Trust Network Access Architectural Models Software Defined Perimeter S This document demonstrates ztra as a foundational zero trust network access framework and provides best practices to strengthen it with security offerings from intel xeon scalable processors. This infographic explores the steps to implement a zta, drawing insights from sans institute’s zero trust strategy guide * and the national cybersecurity center of excellence (nccoe) at the national institute of standards and technology (nist).
Comments are closed.