Zero Trust Network

Zero Trust Network Access Logical Components Of Zero Trust Architecture Learn what zero trust security is, how it works, and why it is important for modern it environments. cloudflare explains the main principles, benefits, and use cases of zero trust network access (ztna) and other zero trust technologies. Zero trust networking is a security model that verifies and monitors every network access attempt, rather than trusting everything inside a corporate network. learn how to create a zero trust network, its terms, and its advantages over traditional perimeter based security.

Zero Trust Architecture And Zero Trust Network Architecture Learn about the design and implementation strategy of it systems that does not trust users and devices by default, even if they are connected to a privileged network. find out the history, principles, and examples of zero trust architecture and data security. Zero trust access (zta) in network security is a model that requires strict identity verification and continuous monitoring for every user and device attempting to access resources, regardless of their location within or outside the network. Learn how zero trust security works on the principle of strict identity verification and authorization for every access request, regardless of location. explore the history, evolution, and benefits of zero trust network access (ztna) and other zero trust measures. Zero trust is a security strategy for modern multicloud networks. instead of focusing on the network perimeter, a zero trust security model enforces security policies for each individual connection between users, devices, applications and data.
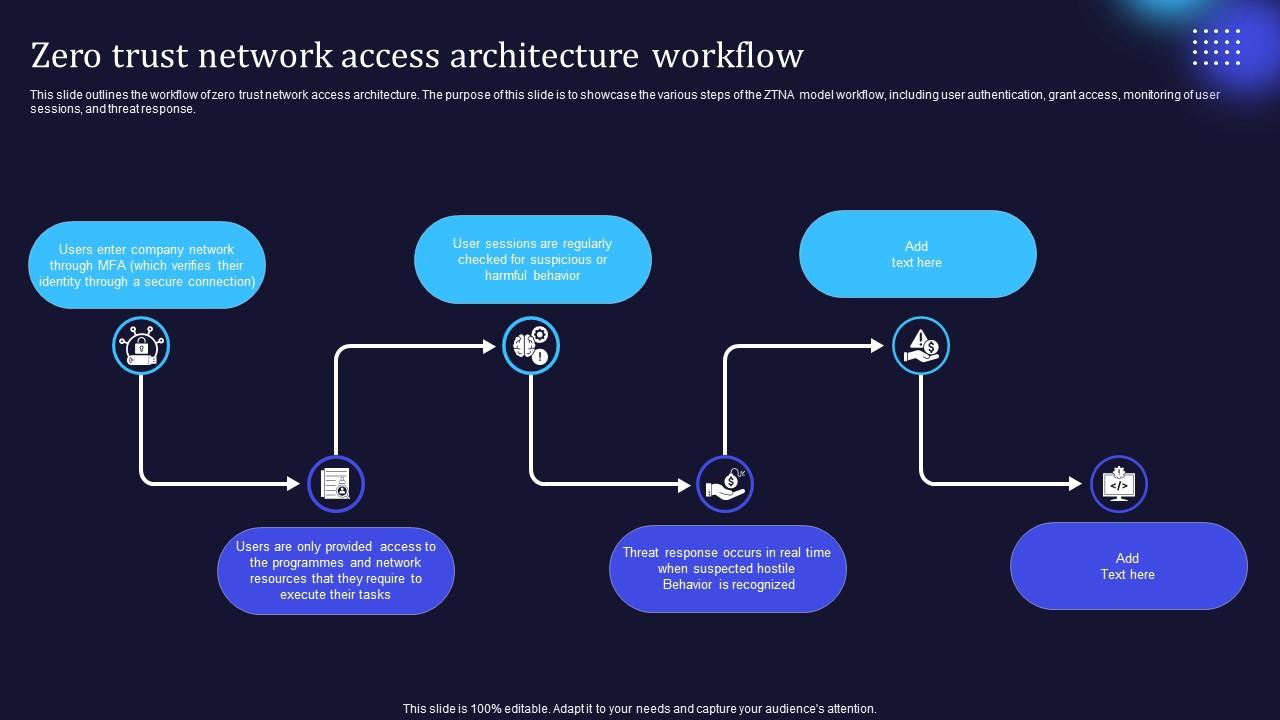
Zero Trust Model Zero Trust Network Access Architecture Workflow Learn how zero trust security works on the principle of strict identity verification and authorization for every access request, regardless of location. explore the history, evolution, and benefits of zero trust network access (ztna) and other zero trust measures. Zero trust is a security strategy for modern multicloud networks. instead of focusing on the network perimeter, a zero trust security model enforces security policies for each individual connection between users, devices, applications and data. Zero trust architecture addresses security for all physical and virtual infrastructure, including routers, switches, servers, cloud services, and iot devices. it ensures that every component is continuously verified and protected, regardless of whether it resides on premises or in the cloud. Initially proposed by john cortez in 2010 and subsequently promoted by google, the zero trust model has become a key approach to addressing the ever growing security threats in complex network environments. Zero trust is a cybersecurity strategy that removes implicit trust, treating all traffic as potentially risky – even if it’s already inside the network. rather than assuming internal traffic is trustworthy, zero trust assumes breach. This guidance contains an abstract definition of zero trust architecture (zta) and gives general deployment models and use cases where zero trust could improve an enterprise’s overall information technology security posture.
Comments are closed.