Zero Trust Moving Beyond The Perimeter Part 2 Duo

Zero Trust Going Beyond The Perimeter In part 2, we walk you through how to implement a beyondcorp based zero trust security model at your organization with detailed steps, caveats and questions to ask. Zero trust: going beyond the perimeter breaks down the zero trust approach to security and examines each pillar of zero trust (workforce workloads workplace) the risks they address options for implementation and proposed maturity levels.
Zero Trust Moving Beyond The Perimeter Part 2 Duo Interested in zero trust security, but uncertain how to make it work for your organization? download our ebook to find out how you can implement a similar security model with the help of duo. In this guide, you’ll get an overview of the beyondcorp theory and how to implement it. an overview of the security theory of google’s beyondcorp and the need for a new zero trust security model to protect enterprise assets. People have certainly been promoting the perimeter’s demise for years now: the jericho forum was created to tackle “de perimeterization” as early as 2003. the idea really picke view more join for free to read . Download this guide to learn the fundamentals of a zero trust approach to enterprise security including the three pillars, risks addressed by each pillar, implementation and proposed maturity models.
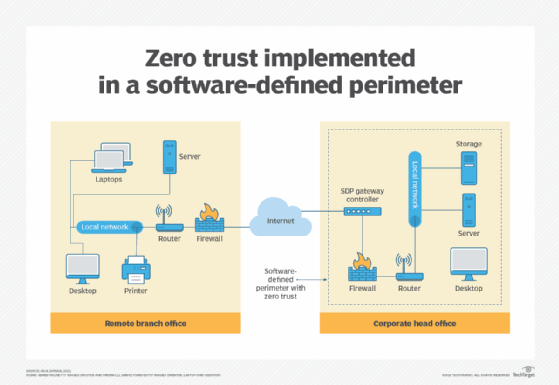
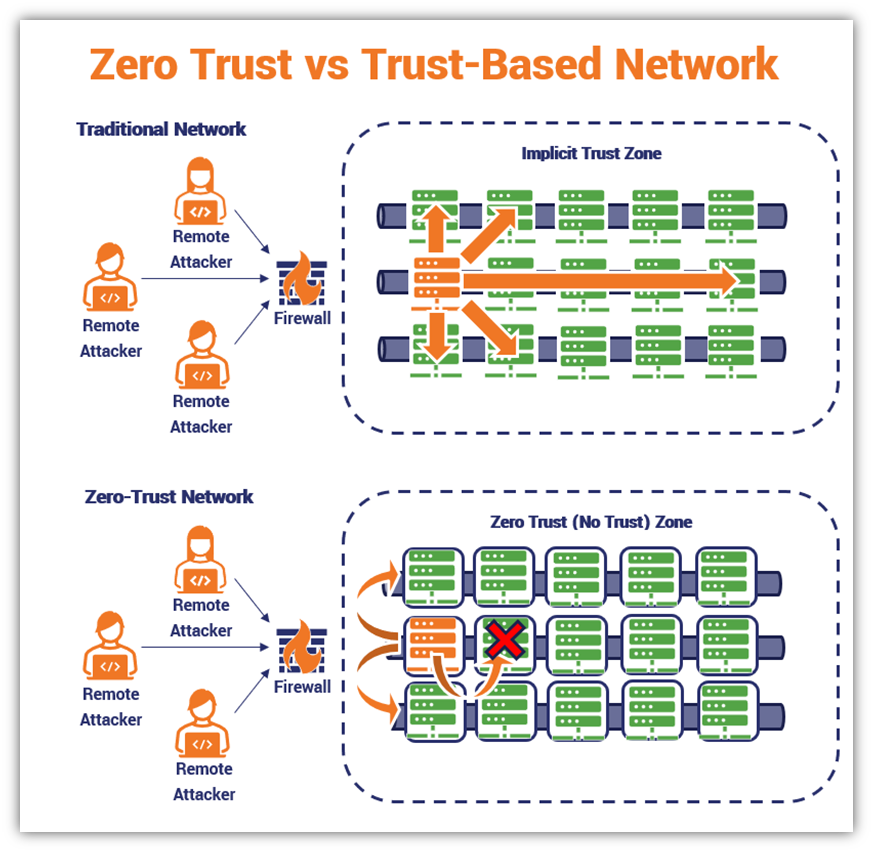
Zero Trust Moving Beyond The Perimeter Part 2 Duo People have certainly been promoting the perimeter’s demise for years now: the jericho forum was created to tackle “de perimeterization” as early as 2003. the idea really picke view more join for free to read . Download this guide to learn the fundamentals of a zero trust approach to enterprise security including the three pillars, risks addressed by each pillar, implementation and proposed maturity models. When moving to zero trust, the decision must be made on a number of factors, including identity and behavior, and it must be verified regularly based on device behavior and any changing factors. Duo provides flexible, frictionless access to hybrid and multi cloud environments, allowing you to apply a zero trust security approach for remote access to cloud infrastructure and corporate applications. By shifting access controls from the network perimeter to individual users, beyondcorp enables secure work from virtually any location without the need for a traditional vpn. In 2020, cisco set out to move from a traditional network based perimeter and vpn model to a zero trust framework. dubbed ‘borderless’ internally, the core goal was to give users a secure, uniform experience accessing applications, wherever the user or application is located.
Comments are closed.