Zero Trust More Confidence
Enable Zero Trust Bigid Booz allen is leading zero trust implementation at scale for the u.s. government. defense and intelligence organizations, federal agencies, and critical infrastructure businesses can implement zero trust cybersecurity with greater confidence and speed using our proven approach. Explore the zero trust assessment to automate security checks, implement industry standards, and strengthen your organization’s zero trust architecture.
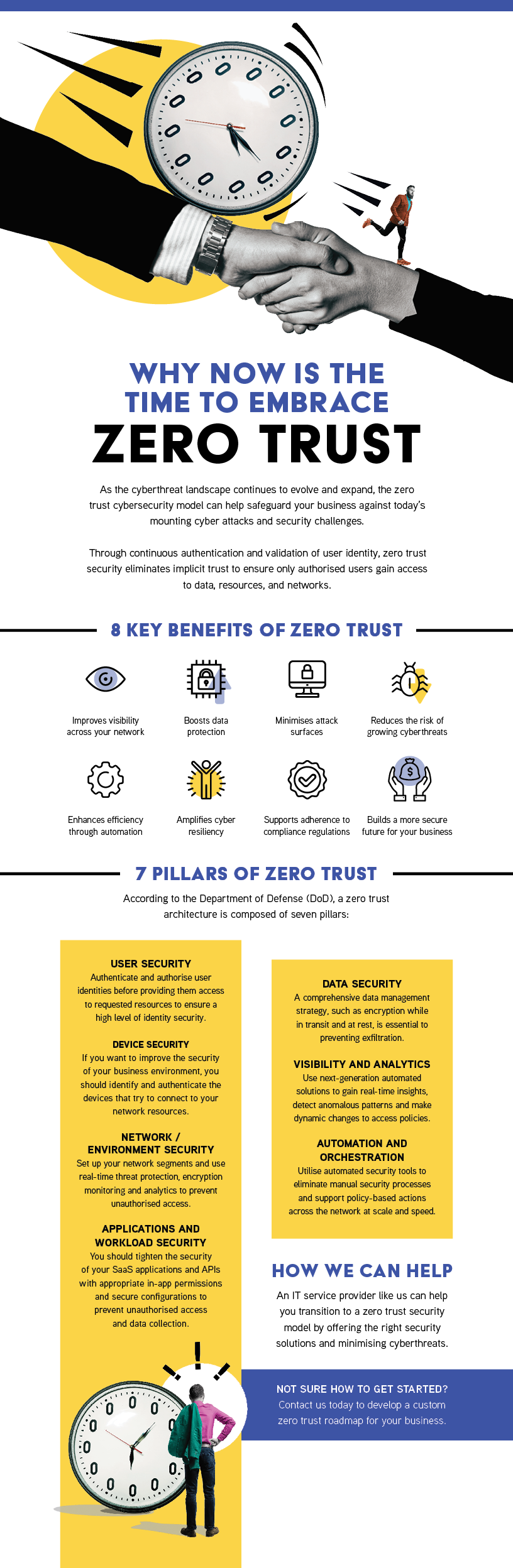
Territory Technology Solutions Zero Trust Zero trust implementation represents a paradigm shift from an outdated, static perimeter based defense (the castle and moat approach) to a more secure, agile, identity centric architecture. it operates on a simple, stringent rule: “never trust, always verify.”. Learn more about what is zero trust security and how it verifies every user, device and request. explore core principles, architecture components and how zero trust protects modern it environments. This way, zero trust strengthens security by ensuring no user, device, or workload is trusted automatically in cloud environments. it continuously validates every access request, monitors user behavior, and segments workloads so a breach in one area does not spread. Zero trust is a security strategy for modern multicloud networks. instead of focusing on the network perimeter, a zero trust security model enforces security policies for each individual connection between users, devices, applications and data.

Zero Trust Doesn T Mean Zero Trust But Confidence In The Trust This way, zero trust strengthens security by ensuring no user, device, or workload is trusted automatically in cloud environments. it continuously validates every access request, monitors user behavior, and segments workloads so a breach in one area does not spread. Zero trust is a security strategy for modern multicloud networks. instead of focusing on the network perimeter, a zero trust security model enforces security policies for each individual connection between users, devices, applications and data. Plan your zero trust deployment with the workshop tool and measure your posture with the automated assessment — now featuring a new ai pillar. Zero trust is a security model based on maintaining strict access controls and not trusting anyone by default. learn more about zero trust. Zero trust adoption increases security resilience for organizations in every industry. as zero trust maturity rises, it is easier to achieve security outcomes such as securing user access to applications with multi factor authentication (mfa) and security service edge (sse). Driving zero trust (zt) progress is an important part of cisa's mission of operational collaboration and information sharing. adopting zt principles addresses many of the challenges of the dynamic threat landscape. specifically, zt improves visibility, enabling organizations to detect and understand threats more effectively.
Comments are closed.