Zero Trust Model Roadmap To Implement Zero Trust Network Access Model

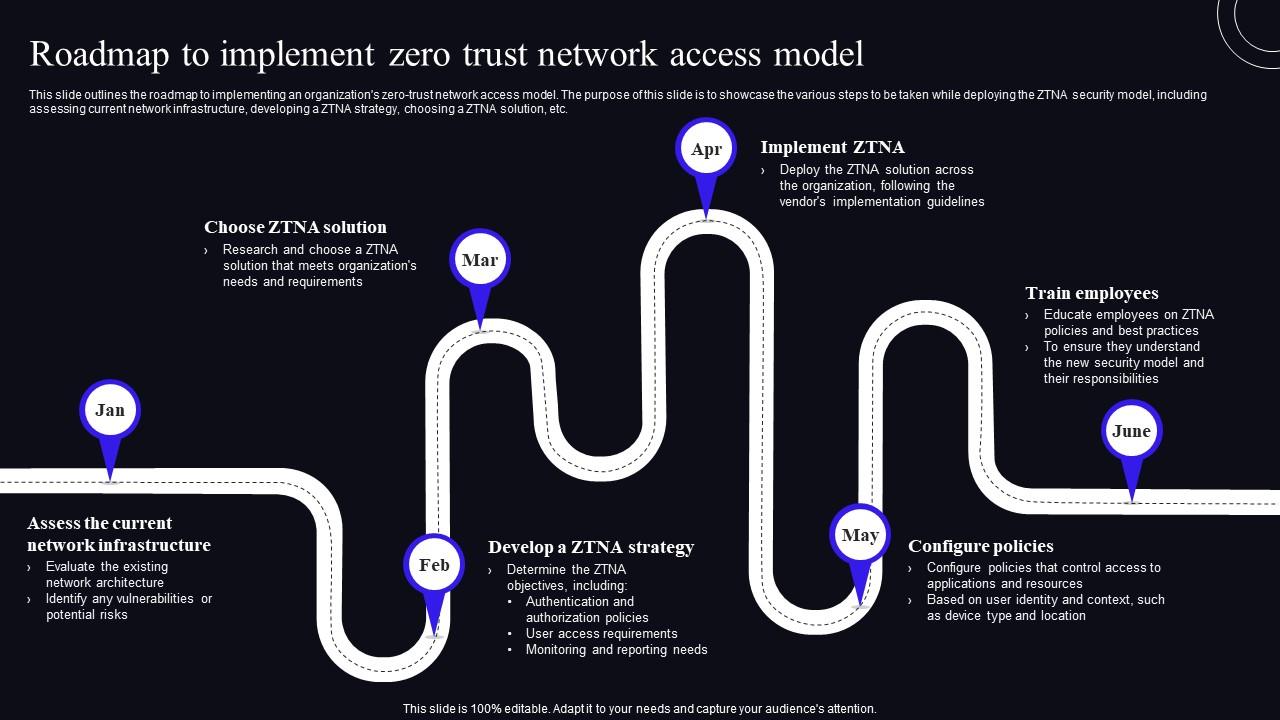
Zero Trust Model Roadmap To Implement Zero Trust Network Access Model Implementing a zero trust architecture can be done in steps without disrupting employee productivity and connectivity. this roadmap was built by security experts to provide a vendor agnostic zero trust architecture and example implementation timeline. Zero trust is easy to understand, but hard to implement, as it requires architectural changes, not just technical controls. let’s understand step by how to implement zero trust in practice.

Zero Trust Network Access Roadmap To Implement Zero Trust Network To help, we’ve built a vendor neutral roadmap for the entire zero trust journey, covering these five projects and others like them. some will take far longer than a few days, but the roadmap can provide greater clarity into what zero trust adoption means. This guide seeks to contribute to the conversation by outlining a framework of capabilities that are necessary for the implementation of zero trust in any network, then provide specific design and configuration examples for achieving a strong zero trust posture. Offers a step by step guide to adopting zero trust principles across enterprise environments. focuses on identity verification, micro segmentation, and continuous monitoring to mitigate modern threats. Learn about the challenges of implementing zero trust in your organization, best practices that can help and a zero trust implementation checklist.

Roadmap To Implement Zero Trust Network Access Model Zero Trust Network Offers a step by step guide to adopting zero trust principles across enterprise environments. focuses on identity verification, micro segmentation, and continuous monitoring to mitigate modern threats. Learn about the challenges of implementing zero trust in your organization, best practices that can help and a zero trust implementation checklist. Simplify zero trust implementation with this detailed guide. learn the policies, compliance, and monitoring strategies to implement zero trust security. The maturity model aims to assist agencies in the development of zero trust strategies and implementation plans and to present ways in which various cisa services can support zero trust solutions across agencies. How i built a comprehensive ztna micro segmentation system using java, python, and react — with step by step setup that takes you from zero to hero in minutes. Find deployment guides, assessment tools, and adoption frameworks to implement zero trust principles that protect and enable secure operations across identity, endpoints, applications, data, infrastructure, and networks in your organization.

Roadmap To Implement Zero Trust Network Access Model Zero Trust Network Simplify zero trust implementation with this detailed guide. learn the policies, compliance, and monitoring strategies to implement zero trust security. The maturity model aims to assist agencies in the development of zero trust strategies and implementation plans and to present ways in which various cisa services can support zero trust solutions across agencies. How i built a comprehensive ztna micro segmentation system using java, python, and react — with step by step setup that takes you from zero to hero in minutes. Find deployment guides, assessment tools, and adoption frameworks to implement zero trust principles that protect and enable secure operations across identity, endpoints, applications, data, infrastructure, and networks in your organization.
Roadmap To Implement Zero Trust Network Access Model Zero Trust How i built a comprehensive ztna micro segmentation system using java, python, and react — with step by step setup that takes you from zero to hero in minutes. Find deployment guides, assessment tools, and adoption frameworks to implement zero trust principles that protect and enable secure operations across identity, endpoints, applications, data, infrastructure, and networks in your organization.

Roadmap To Implement Zero Trust Network Access Model Zero Trust
Comments are closed.