Zero Trust Model Of Cybersecurity Tech Azur

Zero Trust Model Of Cybersecurity Tech Azur An introduction to zero trust model in cybersecurity, the core principles, challenges and impact in healthcare and financial industries. Learn how to apply the guiding principles of zero trust to azure infrastructure and services.

The Power Of Zero Trust Opti9 Tech In this step by step guide, we will explore the principles of zero trust in microsoft azure and provide detailed instructions on how to implement this robust security framework within your azure environment. Businesses and cybersecurity practitioners can readily utilize our operationalized framework to assess their zero trust initiative, which facilitates their planning for more scientific steps to achieve zero trust maturity. An overview of the set of articles that describe how to apply zero trust principles to microsoft azure services. This article provides strategy and instructions for integrating zero trust infrastructure solutions with microsoft defender for cloud.

What Is Zero Trust Architecture Zero Trust Security Model An overview of the set of articles that describe how to apply zero trust principles to microsoft azure services. This article provides strategy and instructions for integrating zero trust infrastructure solutions with microsoft defender for cloud. Instead, zero trust architecture (zta) has become the gold standard for securing modern cloud environments — especially on platforms like microsoft azure. this article explores the principles of zero trust, why it matters, and how to implement it effectively in an azure environment. By using the three azure network security solutions – waf, ddos and firewall, organizations can implement and maintain a robust zero trust model within their azure setup. In this blog, we will describe some azure network security services that help organizations to address zero trust, focusing on the third principle—assume breach. network firewalls are typically deployed at the edge networks, filtering traffic between trusted and untrusted zones. These posters and technical diagrams give you information about deployment and implementation steps to apply the principles of zero trust to microsoft cloud services, including microsoft 365 and microsoft azure.

Why Threatlocker S Zero Trust Model Is Outpacing Cybercrime Instead, zero trust architecture (zta) has become the gold standard for securing modern cloud environments — especially on platforms like microsoft azure. this article explores the principles of zero trust, why it matters, and how to implement it effectively in an azure environment. By using the three azure network security solutions – waf, ddos and firewall, organizations can implement and maintain a robust zero trust model within their azure setup. In this blog, we will describe some azure network security services that help organizations to address zero trust, focusing on the third principle—assume breach. network firewalls are typically deployed at the edge networks, filtering traffic between trusted and untrusted zones. These posters and technical diagrams give you information about deployment and implementation steps to apply the principles of zero trust to microsoft cloud services, including microsoft 365 and microsoft azure.
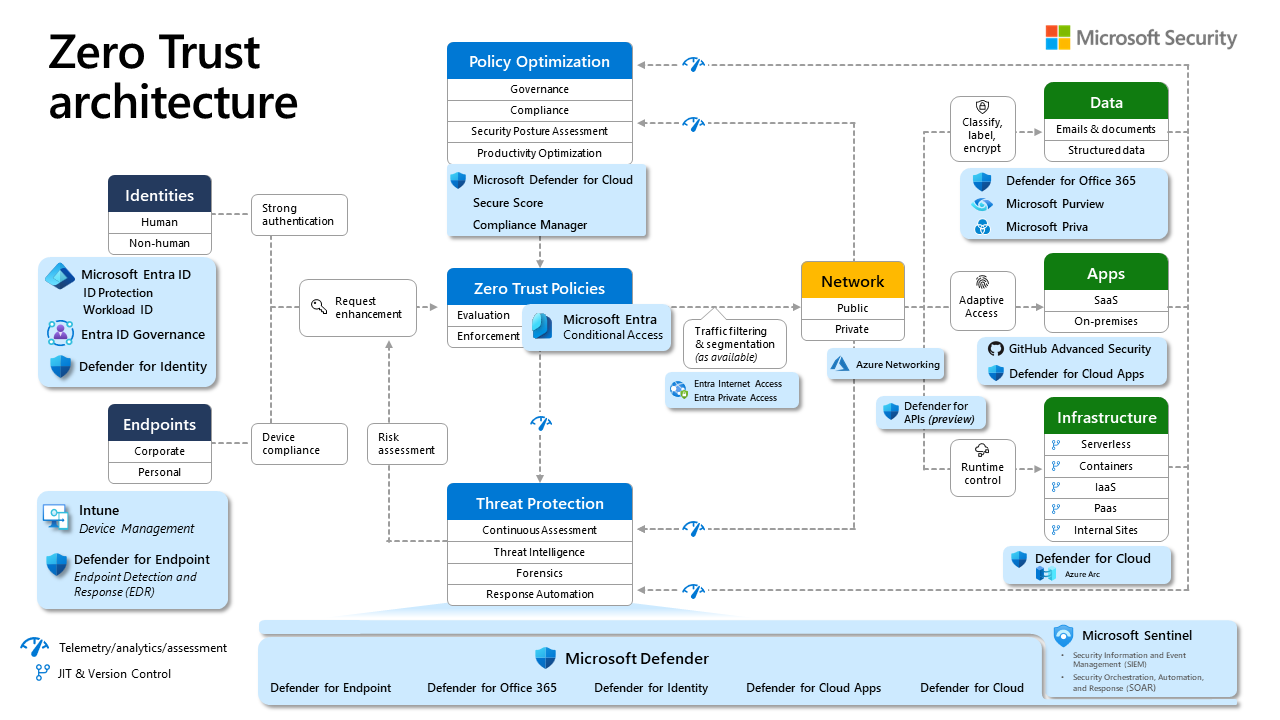
Zero Trust Diagram Know It Like Pro In this blog, we will describe some azure network security services that help organizations to address zero trust, focusing on the third principle—assume breach. network firewalls are typically deployed at the edge networks, filtering traffic between trusted and untrusted zones. These posters and technical diagrams give you information about deployment and implementation steps to apply the principles of zero trust to microsoft cloud services, including microsoft 365 and microsoft azure.
Comments are closed.