Zero Trust Model Modern Security Architecture Microsoft Security

Zero Trust Architecture Modern Security Model Protect against modern threats with a zero trust security strategy powered by ai. discover zero trust security and strategy today with microsoft security. Microsoft recommends a comprehensive set of identity and device access policies for zero trust in this guide — zero trust identity and device access configurations.
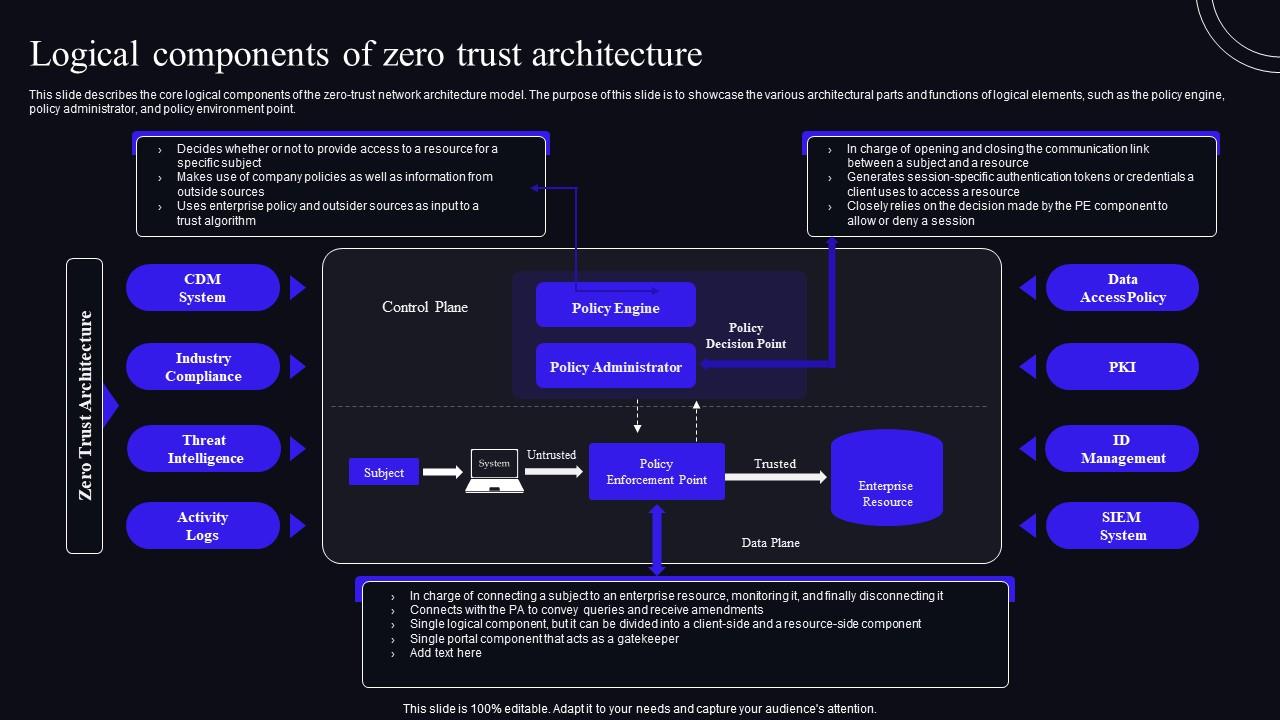
Logical Components Of Zero Trust Architecture Zero Trust Security Model Microsoft’s suite of security tools provides an effective framework to implement zero trust within your organization. in today’s post we review a logical, step by step guide to building a robust zero trust architecture using microsoft’s solutions. A deep dive into microsoft's zero trust security model, breaking down their implementation into actionable phases for any organization looking to modernize its security architecture. Traditional perimeter based defenses, which assume trust once inside the network, have given way to more dynamic models. zero trust architecture (zta) stands at the forefront of this shift, operating on the principle of "never trust, always verify.". Building a zero trust architecture using microsoft’s toolset involves implementing a robust, identity driven security strategy that ensures every access request, whether inside or outside.
What Is Zero Trust Architecture Zero Trust Security Model Traditional perimeter based defenses, which assume trust once inside the network, have given way to more dynamic models. zero trust architecture (zta) stands at the forefront of this shift, operating on the principle of "never trust, always verify.". Building a zero trust architecture using microsoft’s toolset involves implementing a robust, identity driven security strategy that ensures every access request, whether inside or outside. Discover how to implement zero trust architecture using microsoft 365 in this practical, enterprise focused guide. enhance security, reduce risks, and protect data with step by step strategies tailored for modern it environments. This document explains the zero trust security model, its core principles, and how organizations are implementing this approach to address modern security challenges. Zero trust is a modern security approach that assumes attackers may already be in your network and thus “never trust, always verify” every access request. rather than relying on traditional network perimeters, zero trust continually checks identities, devices, and context before granting access. In this article, we explore how to design and implement a robust zero trust security architecture using microsoft defender, microsoft entra id, and microsoft purview.
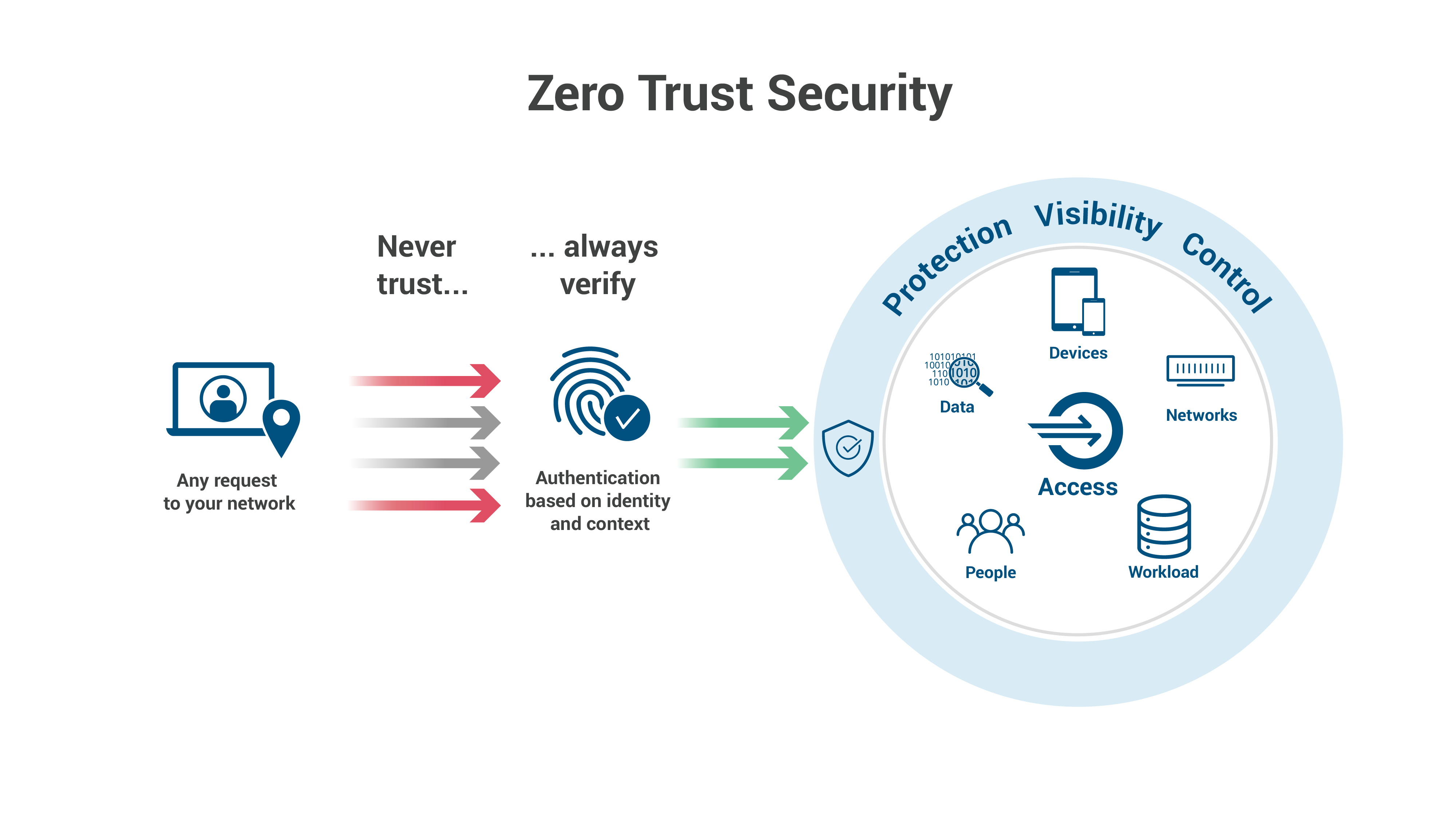
What Is Zero Trust Architecture Zero Trust Security Model Discover how to implement zero trust architecture using microsoft 365 in this practical, enterprise focused guide. enhance security, reduce risks, and protect data with step by step strategies tailored for modern it environments. This document explains the zero trust security model, its core principles, and how organizations are implementing this approach to address modern security challenges. Zero trust is a modern security approach that assumes attackers may already be in your network and thus “never trust, always verify” every access request. rather than relying on traditional network perimeters, zero trust continually checks identities, devices, and context before granting access. In this article, we explore how to design and implement a robust zero trust security architecture using microsoft defender, microsoft entra id, and microsoft purview.
Comments are closed.