Zero Trust Model Logical Components Of Zero Trust Architecture
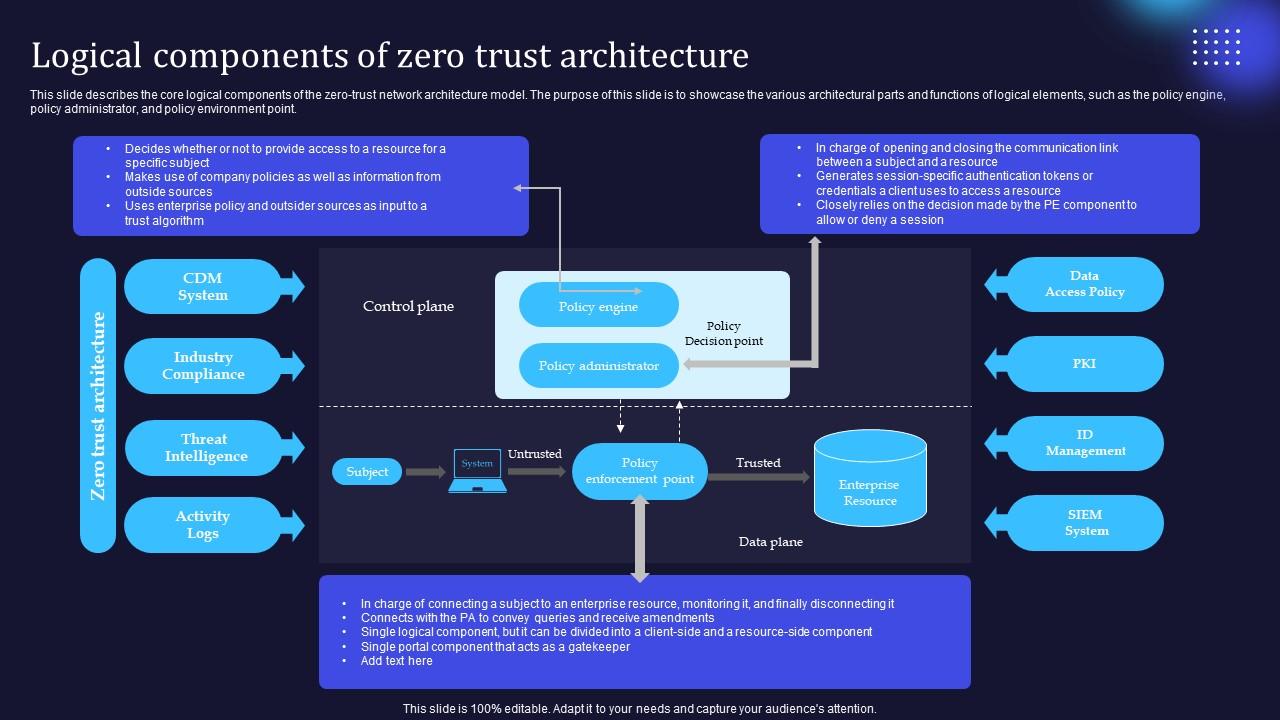
Zero Trust Model Logical Components Of Zero Trust Architecture Nist zero trust architecture (sp 800 207): this foundational standard defines the logical components of zta. it describes three key elements: a policy engine that makes access decisions, a policy administrator that executes them, and a policy enforcement point that enables the connection. Get a comprehensive guide to key zero trust concepts, the most influential frameworks, top zero trust benefits, and best practices for selecting a zero trust vendor.
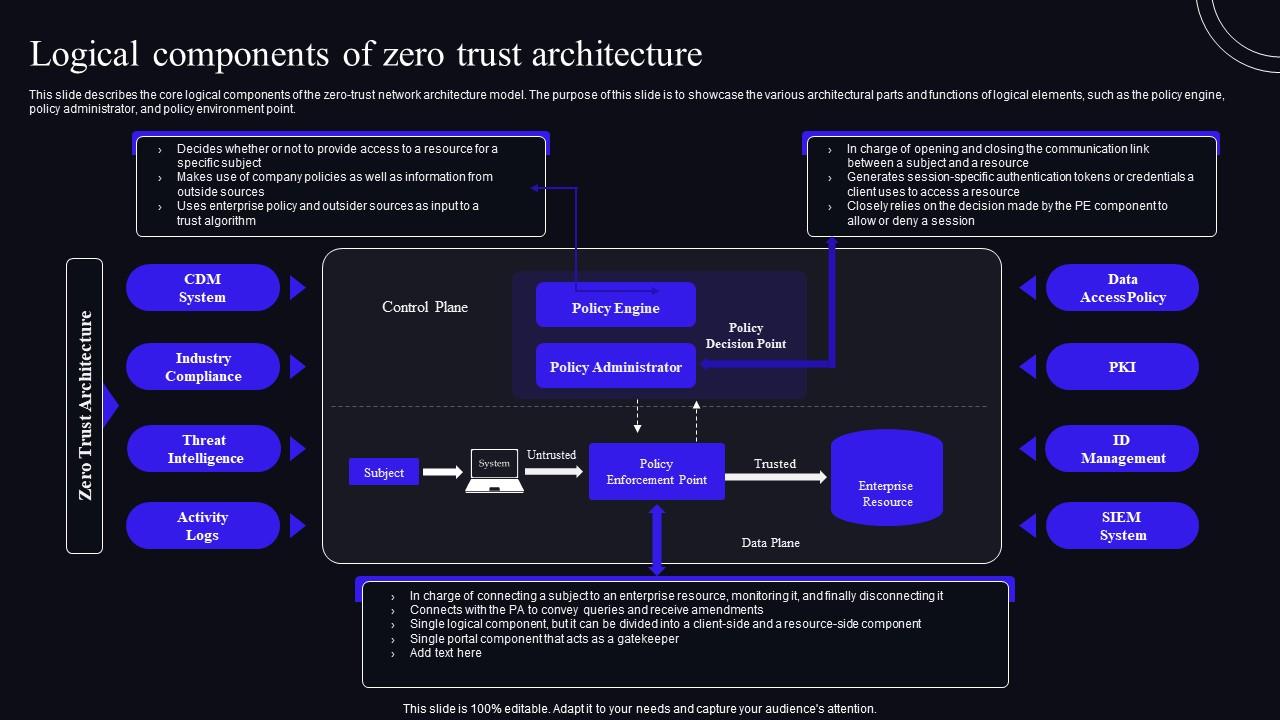
Logical Components Of Zero Trust Architecture Zero Trust Security Model This collaboration resulted in the publication of nist sp 800 207, zero trust architecture. this publication reviews zta fundamentals, logical components, case studies, challenges, and how it can be deployed to aid with cyber security. In this article, we’ll break down nist 800 207 to show what a zero trust architecture really is, how it works, and why it’s not a product but a security philosophy. This document contains an abstract definition of zero trust architecture (zta) and gives general deployment models and use cases where zero trust could improve an enterprise’s overall information technology security posture. This cheat sheet will help you implement zero trust architecture (zta) in your organization. zero trust means "never trust, always verify" you don't trust anyone or anything by default, even if they're inside your network.

Zero Trust Network Access Logical Components Of Zero Trust Architecture This document contains an abstract definition of zero trust architecture (zta) and gives general deployment models and use cases where zero trust could improve an enterprise’s overall information technology security posture. This cheat sheet will help you implement zero trust architecture (zta) in your organization. zero trust means "never trust, always verify" you don't trust anyone or anything by default, even if they're inside your network. To implement a zero trust architecture (zta) strategy effectively, your organization must understand the key components that make up a zta. these components work together to continuously improve upon a comprehensive security model that aligns with zero trust principles. Explore key logical models and workflow patterns in zero trust architecture (zta) as defined by nist 800 207, tailored for cczt exam preparation. Zero trust architecture outlines how these principles are applied across an enterprise's systems, networks, and workflows to ensure that no entity (user, device, or application) gains access without thorough validation. Key components of zta, including context aware and continuous authentication, device authentication, and robust encryption mechanisms, are meticulously analyzed to elucidate their roles in.
Comments are closed.