Zero Trust Model Incognito Lab

Zero Trust Model Incognito Lab Zero trust is no longer nice to have. companies are abandoning the castle and moat approach and adopting systems that never trust by default — they always verify identity, state of device, and risk prior to granting access to a resource of any kind. วันนี้เลยมานำแนะนำอีก model ให้ผู้อ่านทุกคนได้รู้จักคือ zero trust model ที่มี concept ง่าย ๆ คือให้คิดอยู่เสมอว่า ทุก ๆ จุดมีความเป็นไปได้.
Zero Trust Model Incognito Lab Interactive zero trust deployment workshop for planning and tracking security initiatives across identity, devices, network, infrastructure, data, and ai pillars. Zero trust architecture in system design explores a security model focused on the principle of 'never trust, always verify.' this approach assumes that threats could exist both inside and outside the network, so it requires rigorous verification for every user and device trying to access resources. Under a zero trust model, organizations categorize their data so they can apply targeted access control and data security policies to safeguard information. data in transit, in use and at rest is protected by encryption and dynamic authorization. Learn how the zero trust security model protects cloud environments, remote users, and sensitive data with verification and least privilege access.
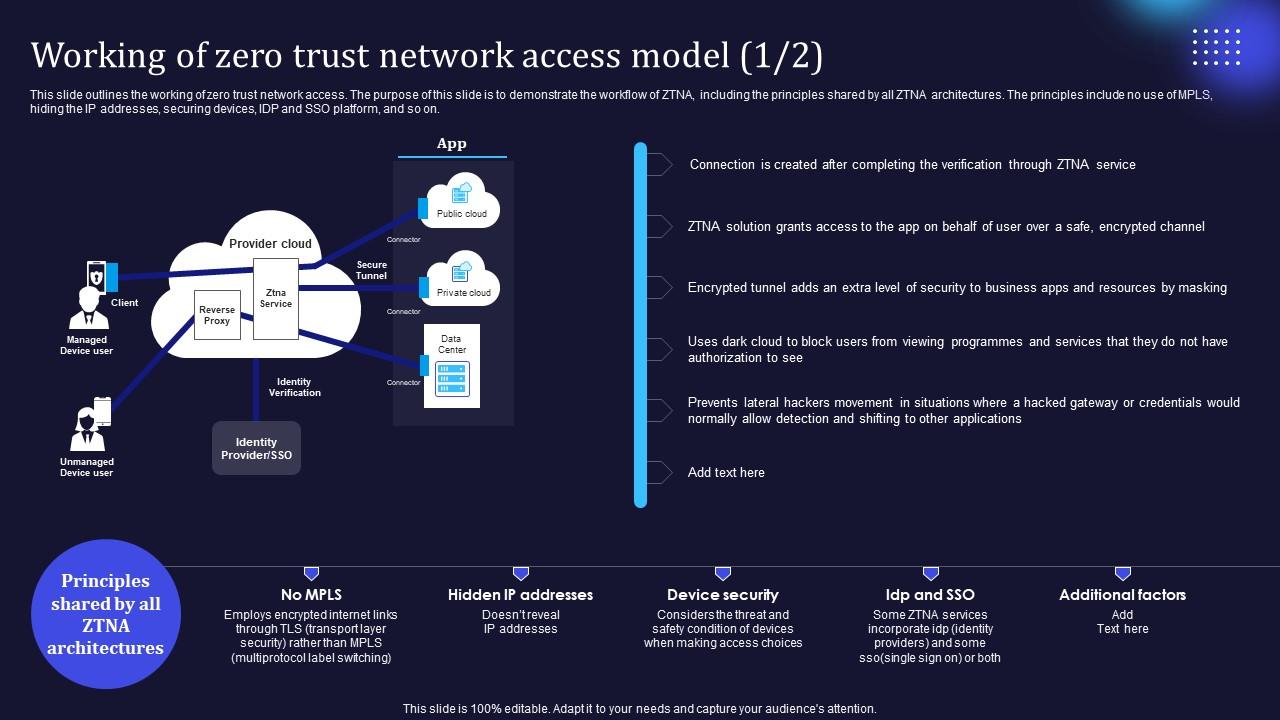
Zero Trust Model Working Of Zero Trust Network Access Model Under a zero trust model, organizations categorize their data so they can apply targeted access control and data security policies to safeguard information. data in transit, in use and at rest is protected by encryption and dynamic authorization. Learn how the zero trust security model protects cloud environments, remote users, and sensitive data with verification and least privilege access. Implement a simulated zero trust environment using pfsense, docker, and vpn tools to model identity aware access and traffic segmentation. this hands on lab will help you implement a small scale zero trust architecture (zta) using open source tools. The zero trust model is a security framework that operates on the principle of "never trust, always verify." it requires all users and devices, whether inside or outside the network perimeter, to be authenticated and authorized before granting access to resources. this approach minimizes the attack surface and prevents unauthorized lateral movement within an organization's systems. We propose a detailed and systematic taxonomy categorizing zta applications, implementation requirements, enabling technologies, and associated challenges. this taxonomy serves as a valuable reference for researchers and practitioners aiming to adopt or study zta in diverse contexts. What is zero trust? the zero trust security model uses identity and context information to continually verify trust before granting least privilege access for users, devices, apps, networks, and clouds.

Zero Trust Model Service Initiated Zero Trust Network Topology Model Implement a simulated zero trust environment using pfsense, docker, and vpn tools to model identity aware access and traffic segmentation. this hands on lab will help you implement a small scale zero trust architecture (zta) using open source tools. The zero trust model is a security framework that operates on the principle of "never trust, always verify." it requires all users and devices, whether inside or outside the network perimeter, to be authenticated and authorized before granting access to resources. this approach minimizes the attack surface and prevents unauthorized lateral movement within an organization's systems. We propose a detailed and systematic taxonomy categorizing zta applications, implementation requirements, enabling technologies, and associated challenges. this taxonomy serves as a valuable reference for researchers and practitioners aiming to adopt or study zta in diverse contexts. What is zero trust? the zero trust security model uses identity and context information to continually verify trust before granting least privilege access for users, devices, apps, networks, and clouds.

Zero Trust Model Steps To Implement Zero Trust Network Access Model We propose a detailed and systematic taxonomy categorizing zta applications, implementation requirements, enabling technologies, and associated challenges. this taxonomy serves as a valuable reference for researchers and practitioners aiming to adopt or study zta in diverse contexts. What is zero trust? the zero trust security model uses identity and context information to continually verify trust before granting least privilege access for users, devices, apps, networks, and clouds.
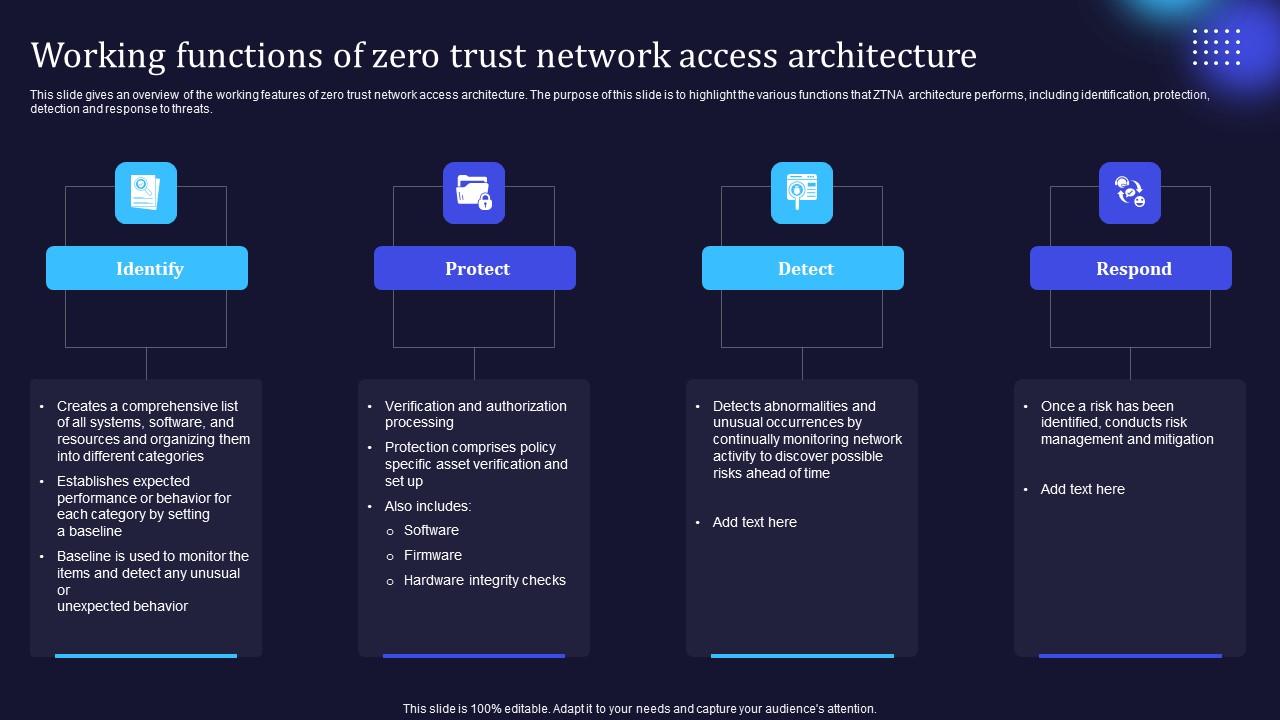
Zero Trust Model Working Functions Of Zero Trust Network Access
Comments are closed.