Zero Trust Implementation Plan Then Execute One Step At A Time

Zero Trust Implementation Plan Then Execute One Step At A Time To build a strong zero trust security framework, organizations should first determine which of their data and systems are sensitive, and then make sure they know where the data is located. Zero trust is easy to understand, but hard to implement, as it requires architectural changes, not just technical controls. let’s understand step by how to implement zero trust in practice.

Zero Trust Implementation Plan Then Execute One Step At A Time In this guide, we’ll break down everything you need to know about zero trust implementation, from core principles and architecture to step by step deployment and best practices. This post was inspired by the zero trust journey takeaways outlined in nist special publication 1800 35, which offers an in depth technical roadmap for organizations looking to implement zero trust across complex environments. In our zero trust guides, we define the approach to implement an end to end zero trust methodology across identities, endpoints (devices), data, apps, infrastructure, and network. these activities increase your visibility, which gives you better data for making trust decisions. Learn how to implement zero trust with clear steps, core principles, and best practices. a practical guide and checklist to help you plan zero trust adoption.
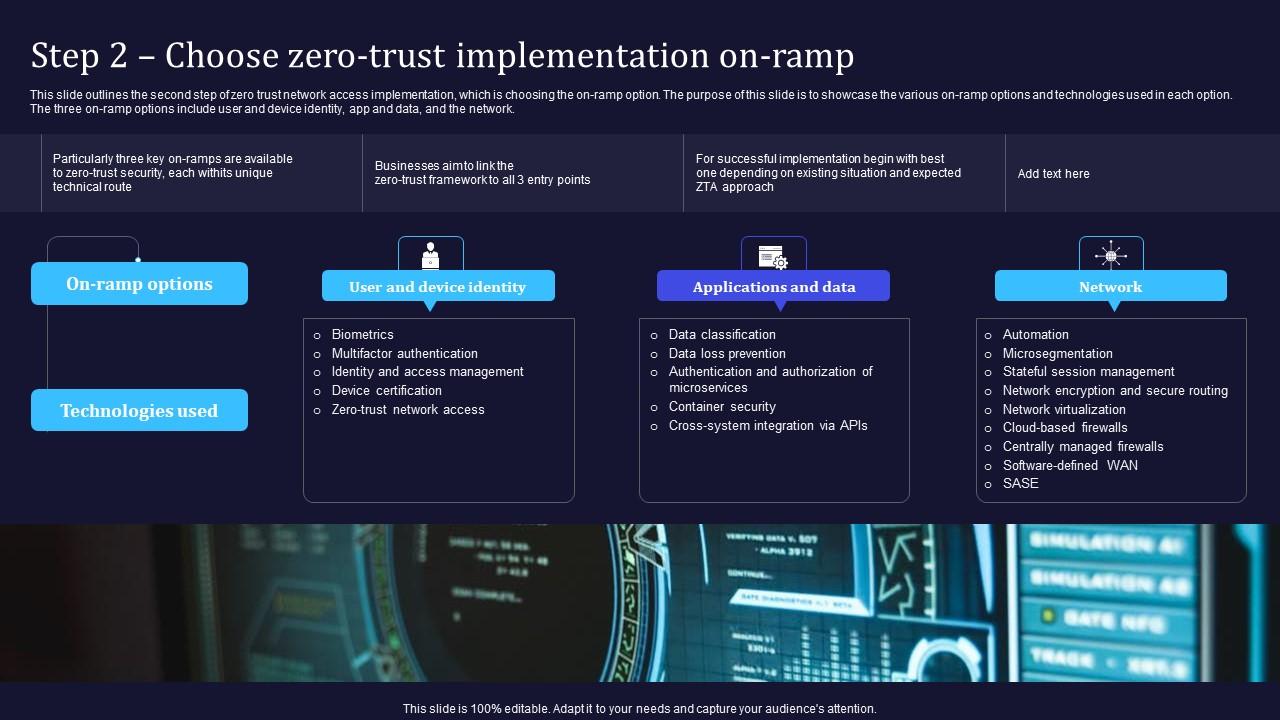
Zero Trust Model Step 2 Choose Zero Trust Implementation On Ramp In our zero trust guides, we define the approach to implement an end to end zero trust methodology across identities, endpoints (devices), data, apps, infrastructure, and network. these activities increase your visibility, which gives you better data for making trust decisions. Learn how to implement zero trust with clear steps, core principles, and best practices. a practical guide and checklist to help you plan zero trust adoption. Explore a step by step guide on implementing zero trust, covering deployment principles, challenges, and best practices for effective implementation. Our comprehensive research offers step by step guidance to implementing your roadmap to a zero trust framework tailored to your organization’s unique needs. With a clear understanding of the five pillars of zero trust and your organizational security goals in mind, you can start acting on your zero trust implementation plan. these 10 steps offer a roadmap for using zero trust principles effectively as the basis for your organization’s security posture. Implementing a zero trust security model doesn't have to be intimidating. this guide covers each step of the process and tools to help maintain compliance.
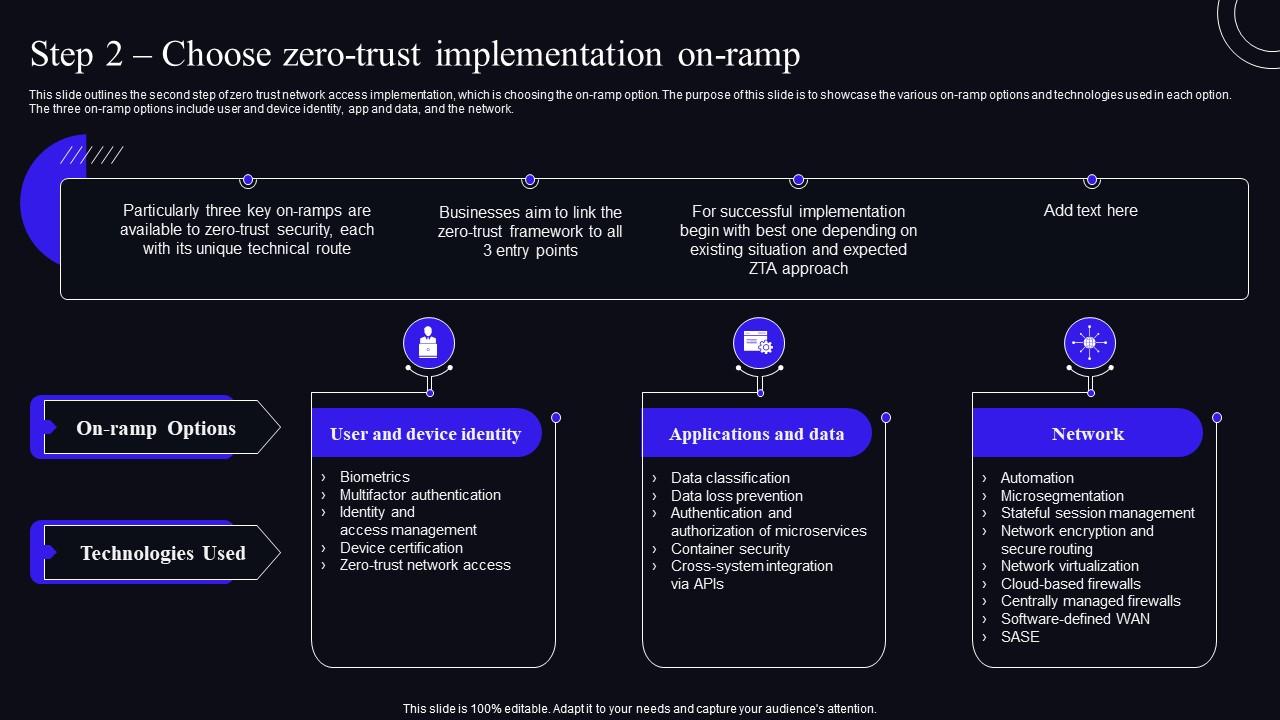
Step 2 Choose Zero Trust Implementation On Ramp Zero Trust Security Explore a step by step guide on implementing zero trust, covering deployment principles, challenges, and best practices for effective implementation. Our comprehensive research offers step by step guidance to implementing your roadmap to a zero trust framework tailored to your organization’s unique needs. With a clear understanding of the five pillars of zero trust and your organizational security goals in mind, you can start acting on your zero trust implementation plan. these 10 steps offer a roadmap for using zero trust principles effectively as the basis for your organization’s security posture. Implementing a zero trust security model doesn't have to be intimidating. this guide covers each step of the process and tools to help maintain compliance.

Few Step Framework Towards Zero Trust Implementation Vtech With a clear understanding of the five pillars of zero trust and your organizational security goals in mind, you can start acting on your zero trust implementation plan. these 10 steps offer a roadmap for using zero trust principles effectively as the basis for your organization’s security posture. Implementing a zero trust security model doesn't have to be intimidating. this guide covers each step of the process and tools to help maintain compliance.

Step 2 Choose Zero Trust Implementation On Ramp Zero Trust Network
Comments are closed.