Zero Trust Framework Unveiling Trustless Security In Cybersecurity

Zero Trust Cybersecurity Framework Enhanced Federal Security Guide Businesses and cybersecurity practitioners can readily utilize our operationalized framework to assess their zero trust initiative, which facilitates their planning for more scientific steps to achieve zero trust maturity. This awareness level course introduces the basic tenets of the federal zero trust (zt) security concepts, provides a high level overview of federal zt strategy, and highlights how a properly executed zt approach can improve security.
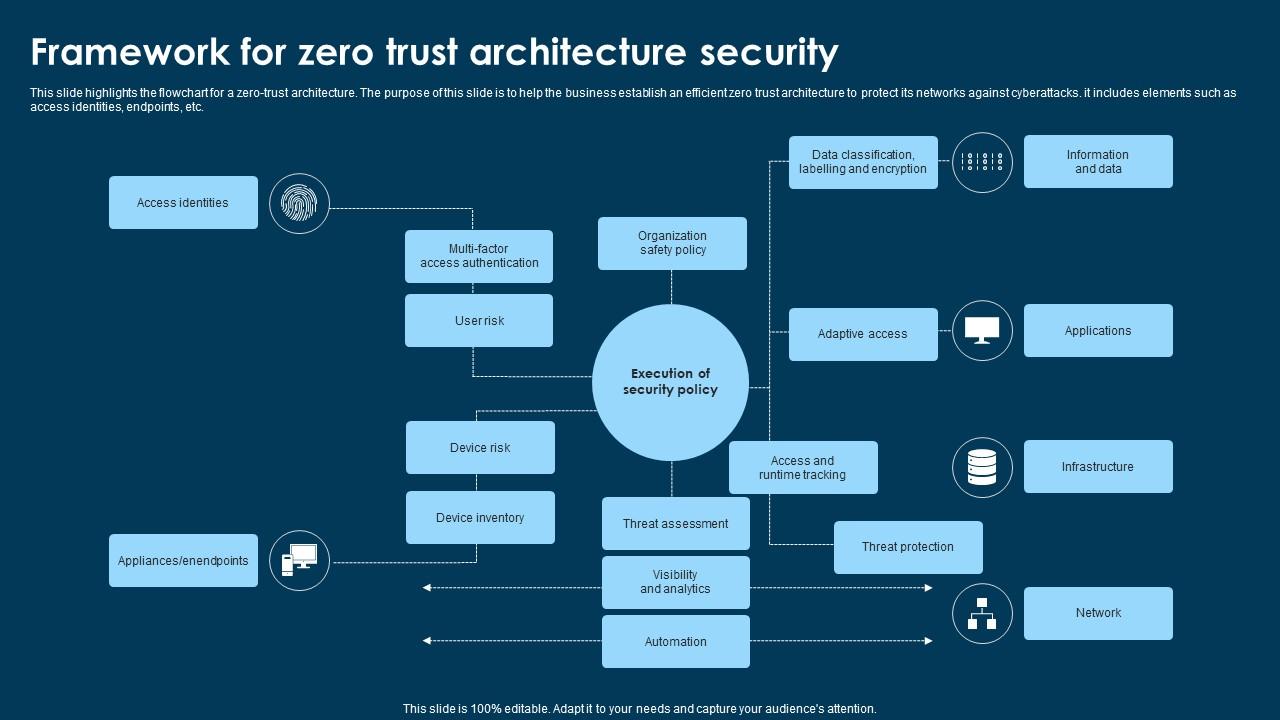
Framework For Zero Trust Architecture Security Ppt Example Zero trust is a robust security model that works on the principle of “never trust, always verify” to ensure secure connections. understanding what is zero trust and implementing it can help organizations safeguard their crucial applications, devices, data, and resources. This paper explores the zero trust architecture (zta) as a contemporary cybersecurity framework that addresses the challenges posed by increasingly interconnected systems. This guide provides a comprehensive overview of zero trust principles, architectural models, practical implementation steps, and the tools needed to build a more secure and resilient organization. Zero trust is not a product or tool, but an essential security strategy that seeks to continuously verify every transaction, asserts least privilege access, and assumes that every transaction could be a possible attack.
Zero Trust Framework Nattytech This guide provides a comprehensive overview of zero trust principles, architectural models, practical implementation steps, and the tools needed to build a more secure and resilient organization. Zero trust is not a product or tool, but an essential security strategy that seeks to continuously verify every transaction, asserts least privilege access, and assumes that every transaction could be a possible attack. By addressing managerial challenges and providing a structured approach, this study contributes to a smoother transition from traditional cybersecurity models to zt frameworks. Zero trust is a security framework that mandates stringent identity verification for every user and device attempting to access resources, regardless of whether they are inside or outside the organization’s network. Zero trust architecture is no longer optional—it’s the future of cybersecurity. with threats growing more advanced and infrastructures more complex, organizations must adopt “never trust, always verify” to protect users, devices, data, and applications. Abstract: zero trust architecture (zta) is a modern cybersecurity framework that eliminates implicit trust within networks, enforcing strict verification for every access request.

Enhancing Cybersecurity Exploring The Zero Trust Security Framework By addressing managerial challenges and providing a structured approach, this study contributes to a smoother transition from traditional cybersecurity models to zt frameworks. Zero trust is a security framework that mandates stringent identity verification for every user and device attempting to access resources, regardless of whether they are inside or outside the organization’s network. Zero trust architecture is no longer optional—it’s the future of cybersecurity. with threats growing more advanced and infrastructures more complex, organizations must adopt “never trust, always verify” to protect users, devices, data, and applications. Abstract: zero trust architecture (zta) is a modern cybersecurity framework that eliminates implicit trust within networks, enforcing strict verification for every access request.

How Zero Trust Security Framework Is Reshaping Enterprise Cybersecurity Zero trust architecture is no longer optional—it’s the future of cybersecurity. with threats growing more advanced and infrastructures more complex, organizations must adopt “never trust, always verify” to protect users, devices, data, and applications. Abstract: zero trust architecture (zta) is a modern cybersecurity framework that eliminates implicit trust within networks, enforcing strict verification for every access request.

Why Zero Trust Is The Future Of Cybersecurity M A Polce
Comments are closed.