Zero Trust Framework Principles And Applications Redfox Security

Zero Trust Maximum Security How To Protect Your Business In 2025 In this blog, we will delve into the concept of zero trust and explore the five core principles of this security model. Contribute to redfox security key principles of a zero trust cybersecurity framework development by creating an account on github.

Zero Trust Framework Principles And Applications Redfox Security This guide will walk you through the steps required to secure applications and apis following the principles of a zero trust security framework. our approach is aligned with these three zero trust principles:. Businesses and cybersecurity practitioners can readily utilize our operationalized framework to assess their zero trust initiative, which facilitates their planning for more scientific steps to achieve zero trust maturity. Get a comprehensive guide to key zero trust concepts, the most influential frameworks, top zero trust benefits, and best practices for selecting a zero trust vendor. This guide provides a comprehensive overview of zero trust principles, architectural models, practical implementation steps, and the tools needed to build a more secure and resilient organization.
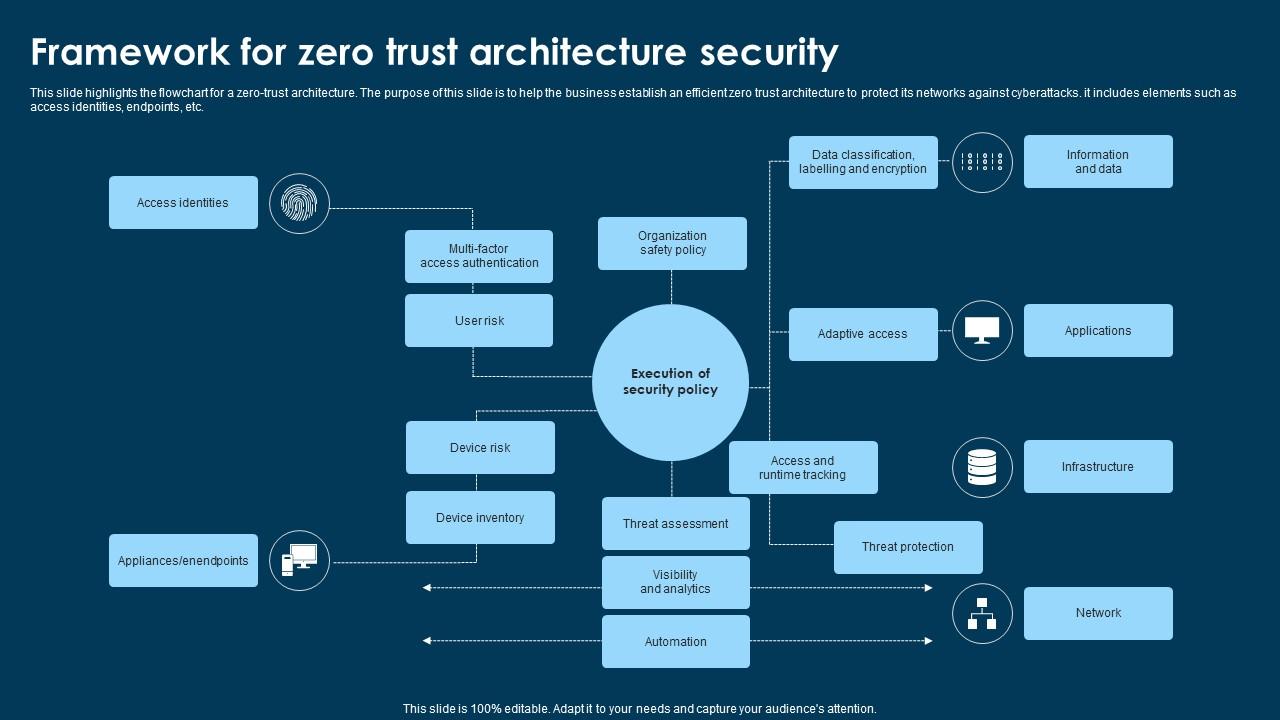
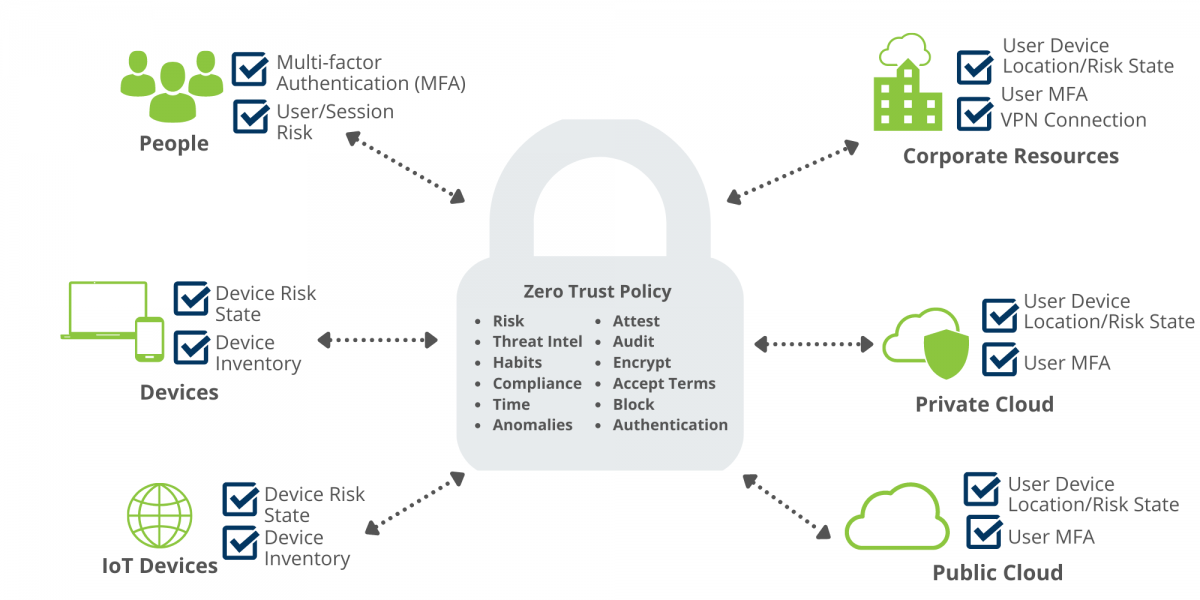
Framework For Zero Trust Architecture Security Ppt Example Get a comprehensive guide to key zero trust concepts, the most influential frameworks, top zero trust benefits, and best practices for selecting a zero trust vendor. This guide provides a comprehensive overview of zero trust principles, architectural models, practical implementation steps, and the tools needed to build a more secure and resilient organization. This paper conducted a survey on the theory and application of zero trust security, organizing and summarizing the fundamental theories and architectural frameworks, as well as the application of zero trust in cloud computing and the iot. This article talks about how to set up zero trust architectures and how well they work by looking at the ideas behind limiting access and constantly checking trust for both internal and. Zero trust is a robust security model that works on the principle of “never trust, always verify” to ensure secure connections. understanding what is zero trust and implementing it can help organizations safeguard their crucial applications, devices, data, and resources. What is zero trust? zero trust is a security strategy for modern multicloud networks. instead of focusing on the network perimeter, a zero trust security model enforces security policies for each individual connection between users, devices, applications and data.
Zero Trust Framework Nattytech This paper conducted a survey on the theory and application of zero trust security, organizing and summarizing the fundamental theories and architectural frameworks, as well as the application of zero trust in cloud computing and the iot. This article talks about how to set up zero trust architectures and how well they work by looking at the ideas behind limiting access and constantly checking trust for both internal and. Zero trust is a robust security model that works on the principle of “never trust, always verify” to ensure secure connections. understanding what is zero trust and implementing it can help organizations safeguard their crucial applications, devices, data, and resources. What is zero trust? zero trust is a security strategy for modern multicloud networks. instead of focusing on the network perimeter, a zero trust security model enforces security policies for each individual connection between users, devices, applications and data.
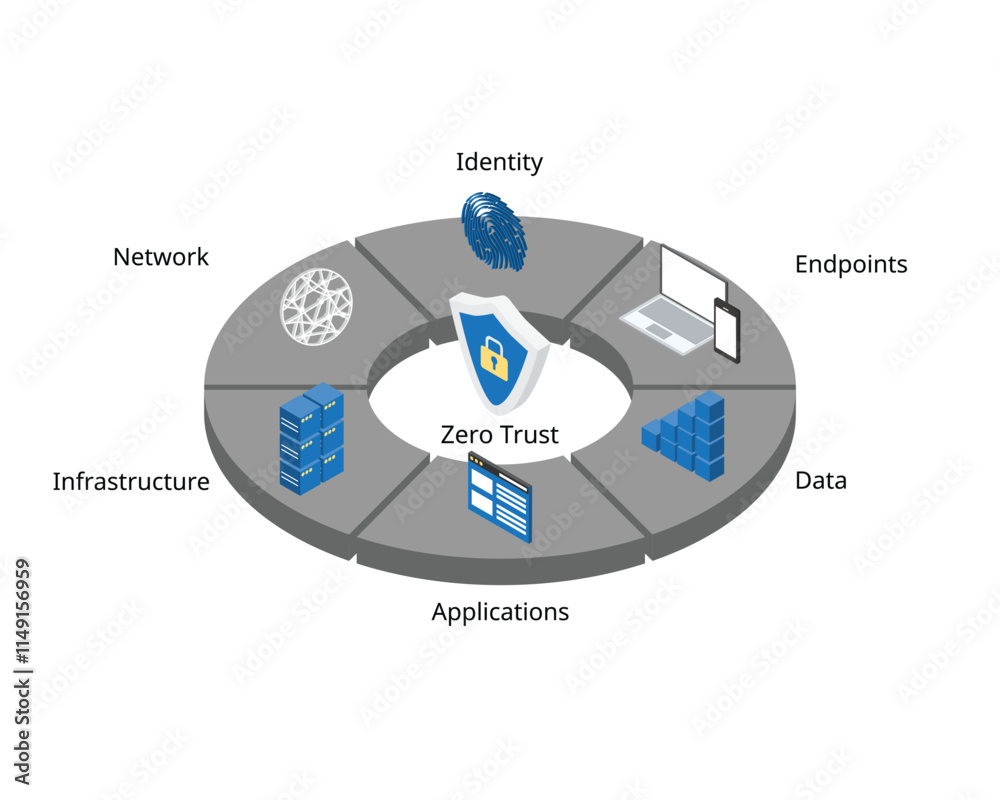
Zero Trust Security Is A Cybersecurity Framework For Security Measures Zero trust is a robust security model that works on the principle of “never trust, always verify” to ensure secure connections. understanding what is zero trust and implementing it can help organizations safeguard their crucial applications, devices, data, and resources. What is zero trust? zero trust is a security strategy for modern multicloud networks. instead of focusing on the network perimeter, a zero trust security model enforces security policies for each individual connection between users, devices, applications and data.
Initiating Your Zero Trust Security Framework Bg Technologies Blog
Comments are closed.