Zero Trust For All A Practical Guide Threatpost
A Practical Guide To Zero Trust Security Threatpost How to use zero trust architecture effectively in today’s modern cloud dependent infrastructures. “zero trust” is a phrase first coined by john kindervag of forrester in 2010 to describe the need to move security leaders away from a failed perimeter centric approach and guide them to a.
A Practical Guide To Zero Trust Security Threatpost How to use zero trust architecture effectively in today’s modern cloud dependent infrastructures. Explore zero trust, the top security model for digital transformation. learn its principles, benefits, and how it protects users, apps, and data in today’s enterprise. How to use zero trust architecture effectively in today's modern cloud dependent infrastructures. Realizing the zero trust motto of “never trust, always verify” is more urgent than ever to combat cybercriminals who thrive on identity theft. however, zero trust is a journey, not a destination. it’s a continuous evolution, shifting from old perimeters to identity first security.

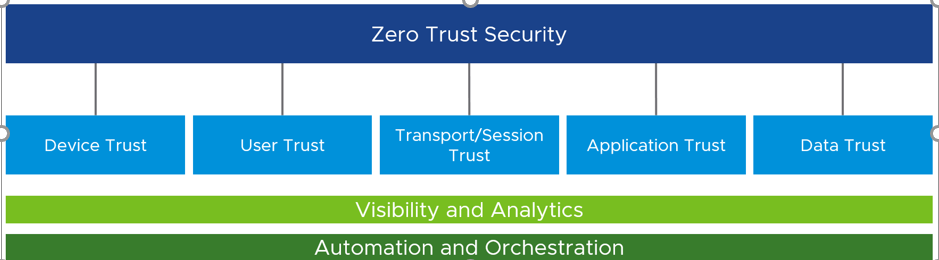
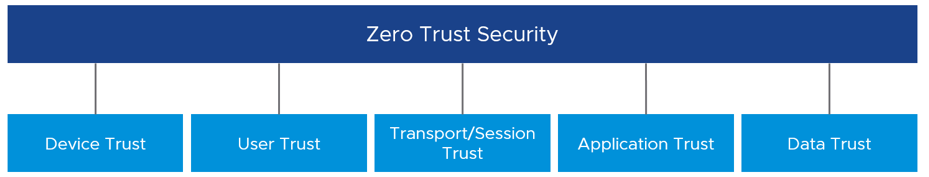
A Practical Guide To Zero Trust Security Threatpost How to use zero trust architecture effectively in today's modern cloud dependent infrastructures. Realizing the zero trust motto of “never trust, always verify” is more urgent than ever to combat cybercriminals who thrive on identity theft. however, zero trust is a journey, not a destination. it’s a continuous evolution, shifting from old perimeters to identity first security. Learn the zero trust security model, its 3 core pillars, and how to implement it step by step using microsoft's framework to protect your business in 2026. In practice, zero trust is an operating model: assume no user, device, workload, or network path should be trusted by default, and require verification and policy enforcement at every meaningful access decision. the reader outcome of this guide is practical rather than theoretical. By way of definition, zero trust is essentially a security paradigm for making sure that people and entities attempting to connect to company resources are who they say they are, which requires explicit permission for every action and continuous monitoring to look for signs of trouble. How to use zero trust architecture effectively in today's modern cloud dependent infrastructures.

Zero Trust For All A Practical Guide Threatpost Learn the zero trust security model, its 3 core pillars, and how to implement it step by step using microsoft's framework to protect your business in 2026. In practice, zero trust is an operating model: assume no user, device, workload, or network path should be trusted by default, and require verification and policy enforcement at every meaningful access decision. the reader outcome of this guide is practical rather than theoretical. By way of definition, zero trust is essentially a security paradigm for making sure that people and entities attempting to connect to company resources are who they say they are, which requires explicit permission for every action and continuous monitoring to look for signs of trouble. How to use zero trust architecture effectively in today's modern cloud dependent infrastructures.

Zero Trust For All A Practical Guide Threatpost By way of definition, zero trust is essentially a security paradigm for making sure that people and entities attempting to connect to company resources are who they say they are, which requires explicit permission for every action and continuous monitoring to look for signs of trouble. How to use zero trust architecture effectively in today's modern cloud dependent infrastructures.
Practical Guide To Understanding And Implementing Zero Trust
Comments are closed.